In the 2023 cyber security report, Check Point’s research teams reported that in 2022, 21% of initial entry vectors were due to phishing incidents.
Well-known brands, such as Microsoft, Google and LinkedIn, Wells Fargo, and Walmart, are frequently imitated by cybercriminals in their attempts to steal individuals’ personal information or payment credentials.
Account threats, fraudulent emails
As an example, LinkedIn users faced the risk of account theft through fraudulent emails disguised as reports, while Wells Fargo customers received emails requesting account information under false pretenses.
Walmart customers were enticed with fake promises of gift cards in exchange for personal information. Similarly, customers of local banks, e-stores, and travel organisations are also often targeted in phishing incidents involving loyalty points, important account-related messages, and fake transaction alerts.
How does the attack work?
Users may be redirected during web browsing or via a fraudulent mobile application
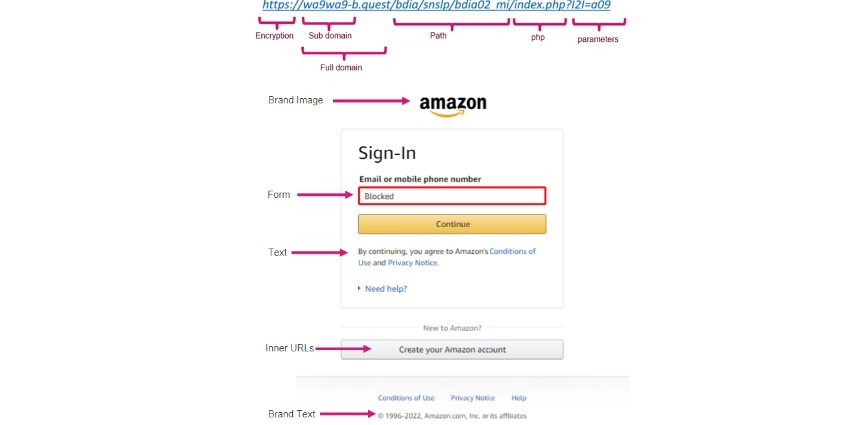
In a brand phishing attack, criminals try to imitate the official website of a well-known brand by using a similar domain name or URL and a web page design that resembles the genuine site.
The link to the fake website is then sent to targeted individuals by email or text message. Users may be redirected during web browsing or via a fraudulent mobile application.
Fake website details
The fake website often contains a form intended to steal users’ credentials, payment details, or other personal information.
Attackers target these mimicked brands from reputable companies because they are confident that these companies have a solid reputation for trustworthiness. Cybercriminals also know that it is difficult for even large companies to stop such brand impersonations by themselves.
Understanding local brand spoofing
In a Local Brand Spoofing attack, the attacker will target local individuals with a Local Brand
While global brands are a common target for spoofing, a significant and growing number of attacks use local brands to create the most compelling social engineering mechanism.
In a Local Brand Spoofing attack, the attacker will target local individuals with a Local Brand that the target will be familiar with.
Convincing and successful tricks
The use of local brands in attacks is extremely effective for attackers as it is highly convincing and often successfully tricks top-level executives and even security professionals. Local Brands used are often banks, financial services, post offices, and government websites.
It is therefore key to understand that defending against attacks using Brand Spoofing needs to take into account the massive challenge of covering not only global brands but local brands on a global scale.
An example of a local brand attack:
Recently the new engine blocked a zero-day Phishing attack trying to impersonate an Indian multinational bank and financial services company headquartered in Mumbai, India.
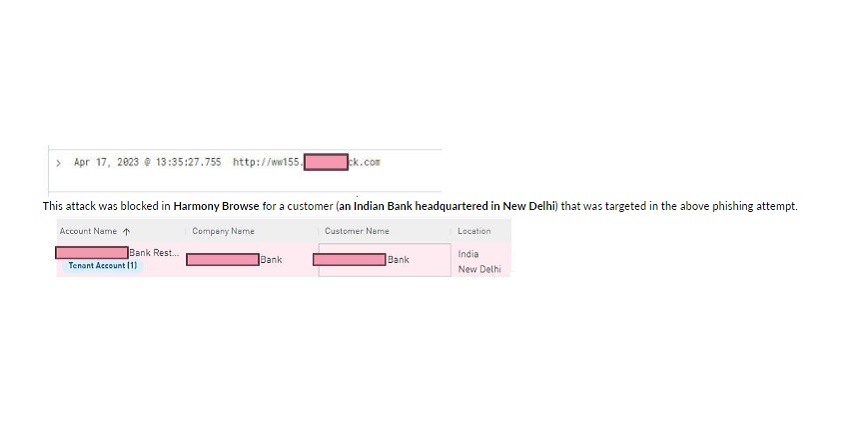
This attack was uniquely detected and blocked by Check Point. Since its launch, Check Point’s patented inline ‘Zero Phishing’ technology has prevented dozens of zero-day phishing campaigns.
Brand Spoofing Prevention
Pre-emptive AI-powered identification and blocking of local and global brand impersonation
Check Point introduced an industry-first, inline security technology, called ‘Zero Phishing’ in its Titan release
To enhance online safety and security, Check Point introduced an industry-first, inline security technology, called ‘Zero Phishing’ in its Titan release, T81.20, leveraging patented technology based on dedicated AI engines.
This Zero-Phishing Security is also available in all Check Point product lines – Quantum, Harmony, and CloudGuard.
AI-Powered engine
Check Point is expanding its Zero-Phishing offering, introducing an innovative new AI-Powered engine to prevent local and global brand impersonation employed in phishing attacks across any attack vector from networks, emails, files mobile devices, SMS, and endpoints to SaaS with a 40% higher catch rate than traditional technologies.
The newly developed engine blocks links and browsing associated with both local and global brands that have been impersonated and exploited as bait to deceive victims in phishing attacks, spanning multiple languages and countries.
Capability to block fake websites
This newly developed engine will have the capability to block fake websites
Capabilities to block spoofed global brands such as Microsoft, and LinkedIn impersonation have been in existence for some time, but this newly developed engine will have the capability to block fake websites impersonating even local and regional brands.
For example, it can detect and block a Spanish Post Office attack or a spoofed site disguised as a local bank in the Netherlands.
Pre-emptive prevention
An additional capability of the new engine is what Check Point calls Pre-emptive prevention, where it scans domains immediately upon registration to detect spoofed domains.
The spoofed domains are then stored in Check Point’s ThreatCloudAI, enabling pre-emptive protection to customers across all Check Point products, with collaborative intelligence across all surfaces, blocking access to links in emails, files, messaging, etc, or while browsing the web.
AI, NLP algorithms
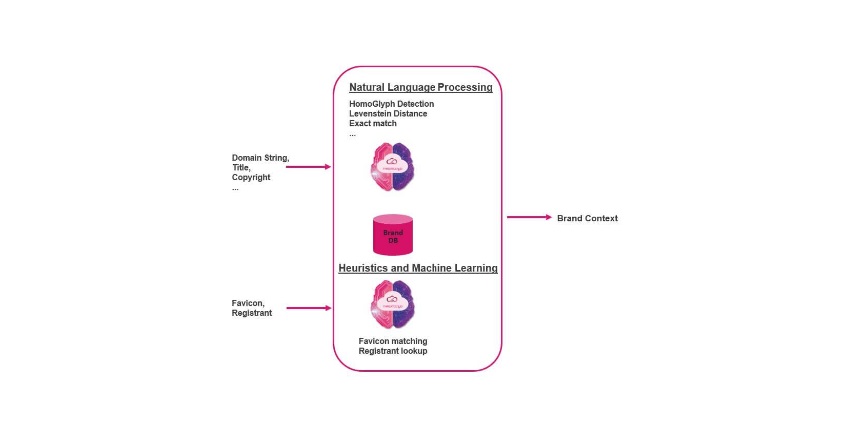
These algorithms compare the structure of the inspected content against a database of known brands
The new engine uses advanced AI, Natural Language Processing (NLP) algorithms, and image processing, to detect similarities to well-known brands.
These algorithms compare the structure of the inspected content against a database of known brands to determine if there is an indication of brand spoofing.
How does it work?
- Uses URL string or web page content as input.
- Extracts features and compares them with many anchors of the original web page, such as domain, favicon, copyright, title, text similarity, and more, to identify the impersonation.
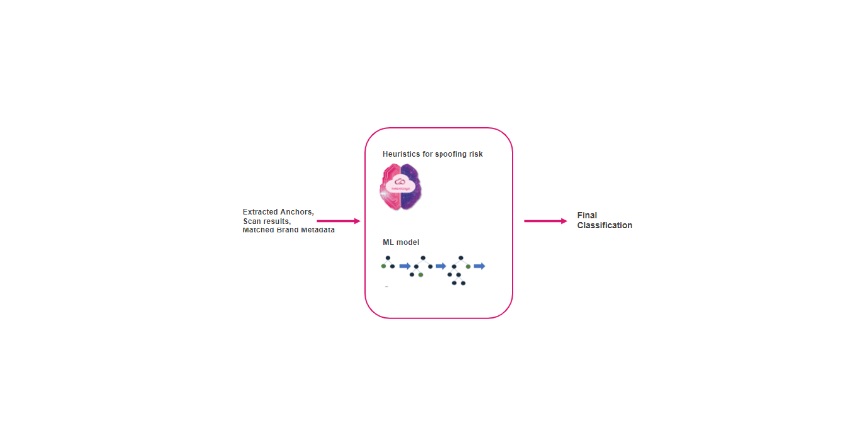
- Uses machine learning and heuristic engines to classify the phishing attack.
- Pre-emptive Prevention – newly registered domains are immediately inspected for Brand Spoofing attempts, being detected and blocked before the attacker's campaign can even begin.
3 classification phases
There are 3 key phases to the classification. In the first step, features are extracted from the URL or page content that will, later on, be used for analysis.
In the second step, using the extracted features and NLP, AI, and heuristics, the brand context is derived.
In the final step, the brand context along with its anchors and all of the extracted features are again run through a classification layer using heuristics and AI for a final classification if the content is genuine or spoofed.
Keep users safe
How to identify URL phishing
URL phishing attacks use trickery to convince the target that they are legitimate. Some of the ways to detect a URL phishing attack are to:
- Ignore Display Names: Phishing emails can be configured to show anything in the display name. Instead of looking at the display name, check the sender’s email address to verify that it comes from a trusted source.
- Verify the Domain: Phishers will commonly use domains with minor misspellings that seem plausible. For example, company.com may be replaced with cormpany.com or an email may be from company-service.com. Look for these misspellings, they are good indicators.
- Check the Links: URL phishing attacks are designed to trick recipients into clicking on a malicious link. Hover over the links within an email and see if they go where they claim. Enter suspicious links into a phishing verification tool like phishtank.com, which will tell users if they are known phishing links. If possible, do not click on a link at all; visit the company’s site directly and navigate to the indicated page.
Check Point’s Zero-Phishing engine, running as part of ThreatCloud AI, revolutionises threat prevention, providing pioneering security as part of Check Point’s Quantum, Harmony, and CloudGuard product lines.
Discover how AI, biometrics, and analytics are transforming casino security













