Intercom: Audio, Video Intercom Systems (2,306)
Browse Intercom: Audio, Video Intercom Systems
- Type of Kit/ System
- Audio Only
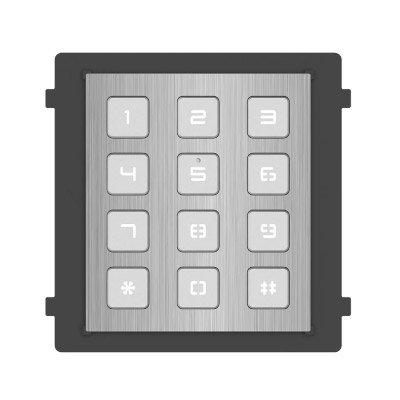
- Keypad & Audio
- Video, Keypad & Audio
- Video & Audio
- Panel Type (separate)
- Audio Panels
- Video & Audio Panels
- Vandal Resistant
- Yes
- Mount Type
- Desk Mount
- Flush Mount
- Surface Mount
- Wall Mount
Audio, video or keypad entry products updated recently
Audio, video or keypad entry - Expert commentary

If you were to ask people outside our industry what door and access security entails, chances are their answers would reflect their common encounters with locks, security guards, c...

Organisations of all types have made it a priority to better track who is coming and going inside their facilities and on their property. This can include an HVAC technician who...

In the past five years, the retail landscape and the relationship between consumers and businesses has shifted drastically. It wasn’t too long ago when shopping at malls was...
Related white papers
The critical role of access control in K-12 school security
Three essential reasons to upgrade your access control technology in 2022
10 top insights in access, cloud and more
Mobile access articles
HID Global, a provider trusted identity solutions, announced the OMNIKEY Secure Element that sets a new simplicity standard for reader manufacturers and others integrating RFID-based security technolo...
HID®, a worldwide pioneer in trusted identity solutions, announced that Baiduri Bank, a member of Baiduri Bank Group and the largest conventional bank in Brunei Darussalam, has implement...
Level Home, Inc., the company redefining the smart home, announced the release of professional installer editions of its industry-renowned, award-winning smart locks, Level Bolt and Level Lock+ includ...
The most common wearable device deployed by security professionals is the body-worn camera. Traditionally used by law enforcement professionals, these devices are finding more and more uses in the cor...
Sharry, a global workplace experience platform built around digital employee badges, has successfully delivered its enterprise solution to London’s new international hub opened by PATRIZIA, a gl...
Since the beginning of the Corona pandemic, MOBOTIX thermal cameras have been increasingly used in the healthcare sector, as well as airports, train stations, public authorities, and companies, to det...
The revolutionary approach to mobile access taken by ABLOY CUMULUS has been recognised by ISJ’s 2024 Leaders in Security Awards. ABLOY CUMULUS was named the 2024 winner in the Innovation Initia...
Genetec Inc., a major technology provider of unified security, public safety, operations, and business intelligence solutions, is pleased to announce its debut at PropTech Connect, taking place at the...
iDenfy, a Lithuania-based RegTech company offering automated KYC/KYB and AML solutions, partnered with Gopher, an innovative on-demand marketplace that connects users with qualified local workers for...
Sustainability is a hot topic. Everyone knows about it. Governments have active Net Zero strategies and implementation plans, while organisations are establishing plans and activities to reduce their...
Zimperium, the global pioneer in mobile security, is proud to announce that it’s collaborating with Okta, the independent identity provider to deliver a significant advancement in identity threa...
HiveWatch, a physical security software company reimagining how organisations keep their people and assets safe, announced a partnership with globally renowned security technology provider - SAGE Inte...
Morse Watchmans, the industry pioneer in key control and asset management systems, will showcase its innovative key control solutions for correctional facilities at the 154th American Correctional Ass...
Pyronix is excited to unveil the BatteryCam2 and SolarPanel2, designed to upgrade security peace-of-mind with exceptional performance and convenience. With the fully wireless BatteryCam2, prope...
Having doors with mechanical security can be a drag on the effectiveness and efficiency of facilities management. While wiring ever more locks to make access control more flexible is expensive and dis...
The security challenges of data centers
DownloadSecurity practices for hotels
DownloadAccess control system planning phase 2
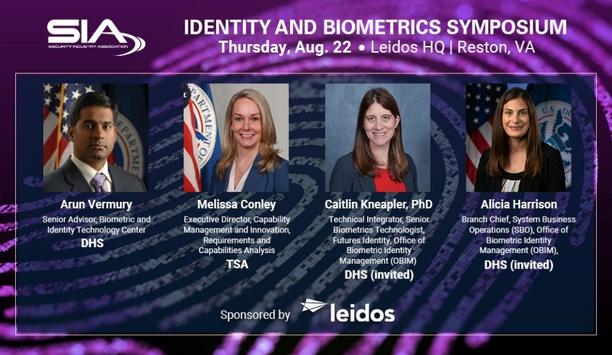
DownloadSIA Identity and Biometrics Symposium
DownloadFacial recognition
Download- Modern public address and voice alarm system from Bosch speeds up boarding at Chopin Airport in Warsaw
- An Indian conglomerate invested in Matrix Telecom Solutions for a transition from wired to VoIP communication
- Traka takes care of key management at Kingston Hospital NHS Foundation Trust
- Morse Watchmans' Key control for K-12 schools