Advancements in biometrics have reached a point where the technology can reliably replace passwords, eliminate threats, and enhance the customer experience all at once. It’s time for enterprises to take a multi-modal approach to biometric authentication and identity management.
Biometrics, a single-modal approach
Biometrics are fast, easy, and eliminate reliance on passwords and PINs, however, despite their growing popularity and benefits, biometrics have their own unique challenges when it comes to widespread adoption, mainly due to reliability and privacy.
Most solutions on the market today only offer single-modal biometrics to authenticate users, this could be one of the reasons that the adoption of biometrics has been slow, particularly at the enterprise level in industries that would benefit most from the technology in terms of user experience, but require greater assurance that their users or employees are who they claim to be. The reliability of single-modal biometric systems plays a part in this.
Multi-modal biometrics offers a solution to finally part ways with passwords and other authentication methods
Single-biometric solutions are less likely to withstand advanced spoofing threats and are also less likely to correctly match biometric templates as a user’s physical characteristics change, whether due to the natural aging process or suddenly as a result of an accident or disability. As a result, the reliability of single-modal biometrics is often questioned. Multi-modal biometrics offers a breakthrough solution to these challenges empowering businesses to finally part ways with passwords and other archaic authentication methods.
Why multi-modal?
Multi-modal solutions that combine physical and behavioural biometrics enable companies to enhance security, without disturbing the user experience.
What is physical biometrics?
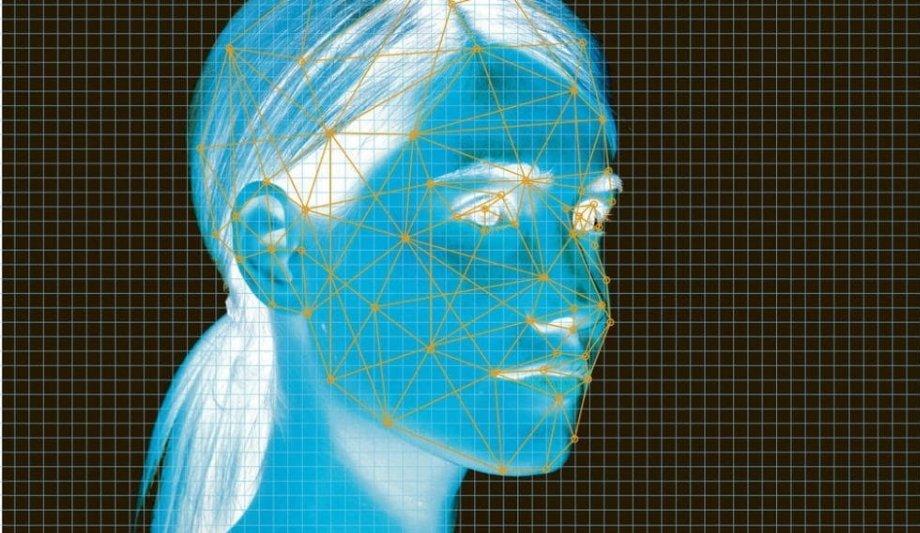
The most popular biometric solutions leverage a user’s unique physical traits to authenticate them. Biometric templates are created by mapping a user’s unique physical traits. For example, Keyless uses Neural Networks, a deep learning technique to extract high-dimensional feature vectors from sequences of images of the user’s face.
What is behavioural biometrics?
Behavioural biometrics leverage deep learning to recognise unique patterns in how a user interacts with a device over time
Behavioural biometrics, on the other hand, leverage deep learning to recognise unique patterns in how a user interacts with a device over time. These patterns could be based on how the user taps, swipes or holds their device. Once patterns have been recognized, they can be transformed into biometric templates that can be used to monitor access to a user’s device in real-time.
Behavioural biometrics offer enhanced usability as they require no conscious effort from the user, allowing for continuous, frictionless authentication, enabling companies to frequently verify that a user is who they say they are, without disrupting the user. Physical biometrics, on the other hand, is better suited to one-time authentication, as they typically require conscious effort from the user.
Frictionless security
When it comes to enabling fast, secure authentication, because biometrics are inherently user-friendly, a multi-modal approach to authentication can directly solve the trade-off between convenience and security.
Multi-modal solutions give companies greater control over managing remote access to their private systems and data. For example, if an employee logs in but then the system recognises unusual behaviour (such as different keystrokes or tapping patterns), then it can log the user out.
Approach to biometric authentication
The keyless protocol allows for physical biometric modalities including facial, fingerprint, voice, and iris recognition
Keyless takes a multi-modal approach to biometrics, leveraging both physical and behavioral biometrics to offer a seamless authentication solution that allows companies to reliably identify users.
The Keyless protocol allows for several physical biometric modalities including facial, fingerprint, voice, and iris recognition; as well as behavioural modalities like keystroke and swipe recognition.
Using deep learning to ensure high-accuracy
To offer behavioural biometrics, one must first learn how users interact with their devices. Keyless does this by feeding deep-learning algorithms unique, user-generated data captured through sensors on the user’s mobile device.
Each input can be gauged on its reliability in authenticating an individual user. Once it’s considered reliable enough for identifying the user with high accuracy, the feature can be added to the user’s biometric templates.
Ensuring privacy compliance
Since biometrics are uniquely linked to the individual, companies processing biometric data must take extra measures to protect it against both new and emerging threats. “Biometrics has the potential to make authentication dramatically faster, easier, and more secure than traditional passwords, but companies need to be careful about the biometric data they collect,” said Maria Korolov.
Keyless ensures that the biometric data captured is never at risk of being stolen, compromised, or lost by combining multi-modal biometrics with privacy-enhancing technologies. The combination of privacy-enhancing technologies, deep-learning, and multi-modal biometrics uniquely addresses the greatest barriers facing the adoption of biometric authentication solutions.
Closing the gap between security and convenience
Multi-modal solutions protect private systems and data in the rare event of spoofing attempts
Multi-modal biometric solutions enable a high level of security without causing undue disruptions to the authentication experience. Rather, multi-modal solutions can enhance the authentication experience by offering frequent, unconscious authentication that can be used to detect advanced threats.
By presenting multiple biometric challenges to users, multi-modal solutions protect private systems and data in the rare event of successful spoofing attempts or account takeovers that take place after the point of authentication.
Thus multimodal biometric solutions can help companies close the gap between security and convenience, allowing for more seamless authentication and identity management experiences that enhance security and privacy compliance, without sacrificing the authentication experience or productivity.
Discover how AI, biometrics, and analytics are transforming casino security