TrueConf, an award-winning video conferencing developer, introduces a new security-focused technology at GITEX Africa 2023 in Morocco.
TrueConf Border Controller is a software solution that hides the IP addresses of TrueConf on-premises team collaboration platforms, blocks unwanted connections of external users, and provides additional protection against DDoS attacks.
Increase in DDoS attacks
Communications within large enterprises and government organisations are becoming increasingly exposed to data breaches, cyber-attacks, and other security threats that can compromise sensitive information.
According to Cloudflare, in the last quarter of 2022, the amount of DDoS attack traffic increased by 79%. Such attacks constituted 35% of all traffic to Aviation and Aerospace Internet properties, and over a third of all traffic to the Finance industries.
TrueConf Border Controller
With TrueConf Border Controller, IT departments can hide a real IP address in a private network
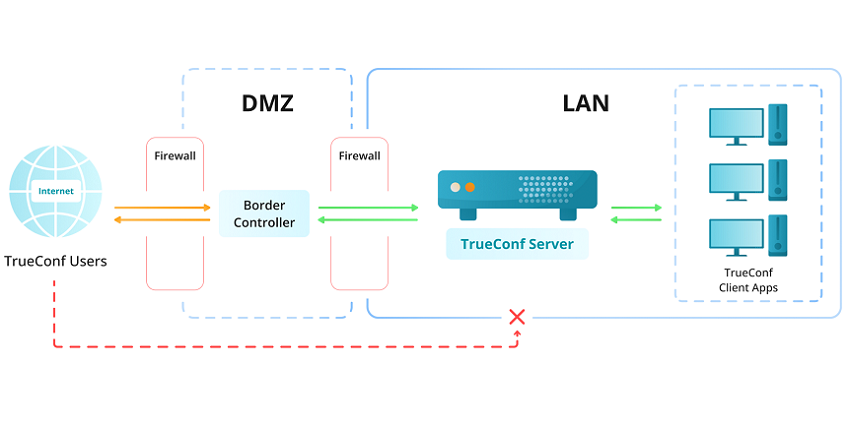
In response to the strong demand for enterprise IT security, TrueConf developed TrueConf Border Controller, a software solution that safeguards self-hosted team collaboration systems against potential external network threats.
With TrueConf Border Controller, IT departments can hide a real IP address of the TrueConf Server deployed in a private network.
Protocol verification algorithm
The solution protects on-premises video conferencing platforms from unwanted external connections. It is achieved due to the protocol verification algorithm that allows external users to connect to TrueConf Server via the secure proprietary protocol used by TrueConf client applications for Windows, Linux, macOS, iOS, and Android.
If any third-party protocol is used, the connection will not be established.
TrueConf Server platform
With TrueConf Border Controller, it is possible to additionally encrypt data transmitted via the Internet
Border Controller is a valuable addition for organisations that use federated TrueConf Server instances. Federation allows users registered on independent TrueConf Server platforms to communicate with each other.
With TrueConf Border Controller, it is possible to additionally encrypt data transmitted via the Internet with subsequent decryption on each separate TrueConf Server instance.
Stable and secure operation
In case attackers try to send multiple connection requests via third-party protocols to conduct an attack, their attempts will be immediately blocked by TrueConf Border Controller.
In its turn, TrueConf Server will remain invulnerable and continue its stable and secure operation in the private network, and its IP address will not be revealed even if TrueConf Border Controller is damaged. The company can also set up backup Border Controllers with other external IP addresses, which will be activated if the primary one is inaccessible.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems












