Beyond Identity, the global provider of the strongest passwordless authentication on the planet has formed a strategic partnership with Ignition Technology to distribute Beyond Identity’s solutions through its extensive network of IT resellers and MSSPs in the Nordics as well as in Benelux.
Recently ransomware attacks have been on the increase, close to doubling from the first half of 2020 to the first half of 2021. Passwords are the number one cause of ransomware attacks and other data breaches, and stolen credentials are at the heart of 85% of all cyberattacks. Beyond Identity addresses this by eliminating passwords as an authentication method. When passwords can’t be used to authenticate, organisations can slam the door on all credential-based attacks.
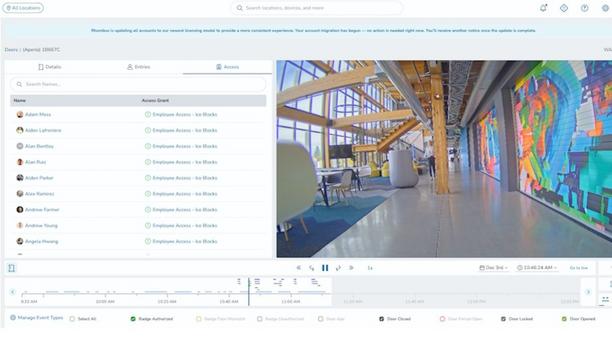
Passwordless method of user verification
The solution eliminates passwords and cryptographically binds the user’s identity to their devices
With the Beyond Identity Platform, organisations can eliminate passwords, positively verify user identities, confirm device trust, and enforce risk-based access controls. The solution eliminates passwords and cryptographically binds the user’s identity to their devices, using asymmetric cryptography, which is the same proven, secure, and scalable technology used to protect trillions of transactions daily across the internet.
Beyond Identity extends the chain of trust established with TLS (modern-day SSL) to end-users and their devices. In this way, it is possible to bind the device to identity, thus making passwords obsolete.
Identity and access management solutions
“We are delighted to start working with Ignition Technology in the Nordics. They were an obvious choice because of their proven ability to deliver cybersecurity, identity, and access management solutions.”
“Like us, they see a huge market opportunity and that the market for this type of solution can be expected to grow rapidly. Together we will work hard to make Beyond Identity a recognised leader in passwordless authentication in Northern Europe”, said Juha Hakava, Regional Director Nordics for Beyond Identity.
The setup of Beyond Identity’s solution is completed in a matter of hours and integrates with all leading single sign-on solutions.
Authentication solutions
Beyond Identity's advanced passwordless platform and solutions complements Ignition Technology's offering" “Ignition Technology is a specialised security distributor for the Saas world and we are focusing on helping our great channel partners to gain advantages of the market with leading new technologies. We have strong experience in identity solutions and have seen increasing demand for authentication solutions that are radically helping customers to improve their security postures and enabling them to reduce risks relating to passwords and trust.”
“We are very pleased to partner with Beyond Identity. Their world-class advanced passwordless platform and solutions are complementing our market-leading Identity offering successfully and we are looking forward to working with their talented and superior team in the Northern European market”, said Marko Lindstedt, Sales Director for Ignition Technologies NEUR.
“Beyond Identity has a 100 % channel-centric business in EMEA. Now that we have the key people on board and a European data centre up and running it’s time for us to work together with our partners to help us grow in the Nordic and Benelux markets,” said Juha Hakava.
Discover how AI, biometrics, and analytics are transforming casino security