As cyber attackers increasingly look to capitalise on accelerating digitalisation that has seen many enterprises significantly increase their reliance on cloud-based solutions and services as well as third-party service providers, software supply chain risk has become a major concern of organisations.
Seventy-nine percent of security professionals responding to a recent survey conducted by the Neustar International Security Council (NISC) indicated that their organisation’s reliance on cloud-based solutions has increased from pre-pandemic levels, with 48 percent saying their reliance has “greatly increased.” Similarly, 78 percent said their reliance on cloud-based services has increased (40 percent greatly), and 66 percent reported that their reliance on third-party services providers has increased (27 percent greatly). As a result, 76 percent of respondents said they now view supply chain risk as a top security priority.
Diligence process for external partners
Security professionals express concern about increased risk due to closer integration with third-party
Reasons cited for this growing reliance include the increased pace of digitalisation within their organisation (69 percent of those confirming increased reliance), the need to scale rapidly due to rising demand for the organisation’s products and/or services (49 percent), and the inability to find in-house talent as readily as previously (39 percent).
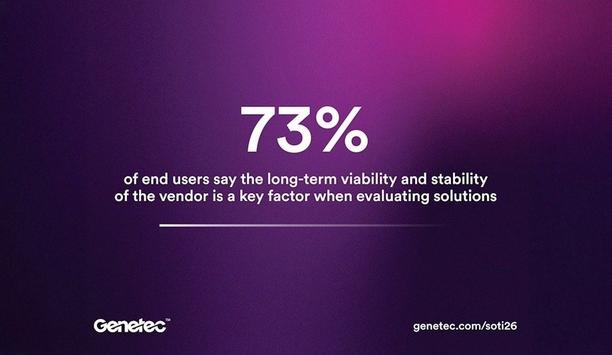
Security professionals continue to express concern about increased risk due to closer integration with third-party partners. Nearly three-quarters (73 percent) of survey respondents believe they or their customers are exposed to some degree of security risk as a result of this integration (24 percent “very significantly”), and 77 percent say they have increased the rigour of their due diligence process for external partners as a result of the Log4j vulnerability and recent attacks against service providers such as SolarWinds and Kaseya.
Security decision-makers
When asked how they feel Log4j has been handled, security decision-makers lacked confidence in the response, both internally and externally. Just 37 percent of respondents believe their own organisation has completely addressed vulnerability issues connected to Log4j, and 43 percent admitted they were unsure whether trusted third-party partners had done so while one in four (24 percent) said “no.”
While 72 percent are confident in the contingency plans they have in place should a critical service provider experience an attack that disrupts services and puts their organisation at risk, 24 percent do not feel confident about their organisation’s response and 4 percent do not know how their organisation would respond.
Author's quote
Cybersecurity due diligence is becoming an increasingly critical component of the vendor process
“Cybersecurity due diligence is becoming an increasingly critical component of the vendor and partner vetting process, as attacks can lead to repair costs and business disruption for organisations that are several steps downstream from the original target,” said Carlos Morales, senior vice president of solutions at Neustar Security Services.
He adds, “Enterprises are recognising that they need to not only optimise their own security measures by adopting a proactive security-by-design strategy — which includes an ‘always on’ approach to cybersecurity — but to invest more in supply chain auditing as well. While digitisation brings undeniable business benefits, it’s worth remembering that any organisation is only as secure as the least secure partner in its supply chain.”
Potential for DDoS attacks
In line with previous survey reporting periods, the potential for DDoS attacks remained security professionals’ greatest concern during the reporting period of May and June 2022 and was ranked the highest threat by 22 percent of respondents. System compromise and ransomware followed at 19% and 18%, respectively. Ransomware, DDoS attacks and targeted hacking were the threats most likely to be perceived by respondents as increasing during the reporting period, and vendor or customer impersonation, targeted hacking, and DDoS attacks were the threat vectors that respondents indicated their organisations were most focused on addressing.
Of the enterprises surveyed in July, 85 percent reported having been on the receiving end of a DDoS attack at some point. The majority (57 percent) reported outsourcing their DDoS mitigation, and most (62 percent) said initiation of mitigation typically took between 60 seconds and 5 minutes, in line with previous responses. The NISC survey was conducted in July 2022 and reflects respondents’ activity and concerns during May and June 2022.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems