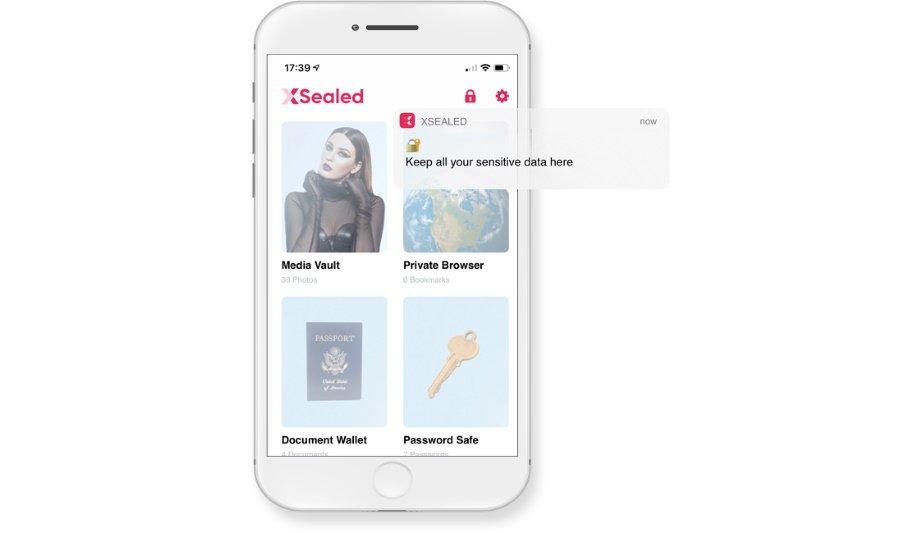
iPhone users have a new way to keep their data and information safe from hackers with XSealed, an app that creates a maximum-security room to securely house private data and activity.
XSealed iOS app
The newly launched XSealed iOS app is available now in the AppStore and allows users to manage passwords, browse privately, and store their private pictures, files and other information in an encrypted room, which hackers cannot decipher, even if the phone is compromised by an intruder.
According to Pew Research, 64% of Americans have experienced a major data breach of some sort and when it comes to smartphones, devices can be compromised by phishing attempts, public Wi-Fi, poor password management, malware, and other common hacking attempts.
Enhancing personal data security
When a user downloads the XSealed app and sets up a private room, they can securely browse the internet
The XSealed app ensures that user data is protected, even if a phone is accessed physically by someone who obtains the password or by online hacking. When a user downloads the XSealed app and sets up a private room, they can securely and privately browse the internet, without their activity being accessible to outsiders.
They are able to access a secure password manager and they can safely store their most private pictures and videos, as well as their banking information, contacts and anything else that they want to keep private.
Secure cloud backup and restoration
With XSealed, users get maximum security through configurable locks, encryption, lockout attempts protection to stop hackers, lock and key protection to keep keys private, account recovery for lost or forgotten keys, and quick wipe to erase the vault contents. Additionally, XSealed provides a secure cloud backup and restoration feature to recover lost data.
Another feature available with XSealed is a secure password manager, which enables the user to load their favourite sites, long passwords and usernames, and assign an icon of choice for each. Once the password item is created, a user only needs to click the assigned icon and they are automatically logged on to the corresponding site, allowing for quick access to frequently visited websites.
“With XSealed, iPhone users now have the most secure way to keep private information private, whether from a snooping intruder or an online attempt to access the phone by hackers,” said the XSealed development team.
Configurable locks
With the XSealed app, lockout attempts have security features to protect against hackers
Configurable locks for the app work by giving the user a choice of up to 3 lock options for their private room, including biometric, pattern, and password unlock.
With the XSealed app, lockout attempts have security features to protect against hackers trying to access the phone, yet the app still enables account recovery for genuine lockouts, if in the case keys are forgotten.
Lock and key protection
Lock and key protection with XSealed works by creating unique keys after setup is completed. Unlike passwords, keys are not saved anywhere on the device. This increases security in the event of a hack as keys are matched to the locks by hashing, an algorithmic method that creates the keys at the time of each successful unlock.
Once inside the XSealed vault, users can access a main control panel with sections that organise their private activity or storage. Everything in the vault is encrypted and secure unless exported outside of the app.
Free and paid subscription options
Anyone interested in trying the XSealed app can do so for free by downloading the app in the AppStore. The free version includes limited entries, while the paid monthly subscription option for XSealed allows unlimited entries to be made in the private room.
Discover how AI, biometrics, and analytics are transforming casino security