Lenel CCTV Multiplexers (1)
Browse CCTV Multiplexers
- Make
- Lenel
Multiplexer products updated recently
Multiplexers - Expert commentary

Technology is changing the look and function of today’s security control rooms. Old-school CRT (cathode-ray tube) monitors are giving way to the thinner, flat screen monitors...
Selecting the optimum power supply for a system is critical to an installation When it comes to selecting power supplies, knowledge is power. Determining the power req...
Latest LenelS2 news

Dubai World Trade Centre — Sheikh Saeed Hall 2, Stand C43, January 12–14, 2026. Organisations of every size and type have discovered how connected digital access helps...

ISC West 2025 in Las Vegas showcased the latest advancements in security technology, offering security professionals a glimpse into the future of the industry. This year's expo hig...

Altronix, the recognised pioneer in power and data transmission products for the professional security industry, is displaying the company’s latest innovations here at I...
Related white papers
Choosing the right storage technology for video surveillance
Trending topic articles
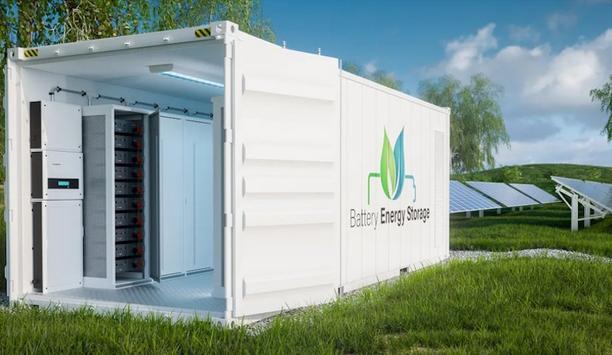
As the world transitions to renewable energy, Battery Energy Storage Systems (BESSs) are helping meet the growing demand for reliable, yet decentralised power on a grid scale. These systems gather su...
Having an emergency response plan is essential for businesses of all sizes, across every industry. But in energy facilities, particularly those dealing with hazardous or explosive materials, it become...
The use of Photovoltaic power systems (PV), also known as solar panels, has grown over the last decade in commercial settings as many corporations have made commitments to reach zero-carbon emissions...
Acoem, a pioneer in advanced physical security solutions, announced that a large North American utility is utilising its ATD Gunshot Detection system to protect critical infrastructure at multiple sit...
ZeroEyes, the creators of the first AI-based gun detection video analytics platform to earn the full US Department of Homeland Security SAFETY Act Designation, announced now that Ki Charter has expand...
As 2025 draws to a close, the Door & Hardware Federation (DHF) is reflecting on a hugely productive year. Indeed, it has been defined by achievement and collaboration, and by a tireless commitment...
It took just seven minutes to steal more than $100 million in jewels from the Louvre, in an operation so swift and precise it exposed a deeper flaw in how even the most secure institutions protect wha...
With Idesco Oy acquiring Exilight, effective January 1, 2026, they will start providing safety and emergency lighting products as part of the offering. Exilight products will remain under Exilight bra...
Hikvision, a world-pioneering manufacturer and supplier of security products and solutions that deliver the ideal combination of high performance and extreme value, now announced the release of its Hi...
Hornets Sports & Entertainment (HSE) and Honeywell announced a multi-year strategic partnership that designates Honeywell as the Official Building Automation Partner for the Charlotte Hornets.&nbs...
Dubai World Trade Centre — Sheikh Saeed Hall 2, Stand C43, January 12–14, 2026. Organisations of every size and type have discovered how connected digital access helps them implement smart...
Integrated access control and security manufacturer TDSi is delighted to welcome Damian Garner to the team. Damian joins as New Business Sales Associate and brings over 20 years of sales an...
Kitakobushi Resort operates multiple distinctive properties in Shiretoko, Hokkaido – a UNESCO World Natural Heritage site since 2005. Their portfolio includes a large resort hotel overlooking th...
To date, there is no standardised or unified verbal communication protocol specifically tailored for effectively and precisely prioritising intrusion alarm calls to Emergency Communication Centres (EC...
For a global oil and gas organisation, achieving and maintaining PCI compliance across its USA and EMEA operations was becoming increasingly complex. Their existing PCI auditing system lacked the visi...
One system, one card
DownloadAligning physical and cyber defence for total protection
DownloadUnderstanding AI-powered video analytics
DownloadEnhancing physical access control using a self-service model
DownloadHow to implement a physical security strategy with privacy in mind
Download- Imperia enhances security with Dallmeier cameras
- Jashanmal, a Middle East retailer attracts more customers with innovative LED and LCD displays from Hikvision
- Bosch video surveillance solution installed at PETCO Park in San Diego, California
- Vicon’s surveillance system provides retail security at the Bullring shopping centre