Throughout the UK there are many examples of smart city transformation, with key industries including transport, energy, water and waste becoming increasingly ‘smart’.
A smart city is a one that uses information and communication technologies to increase operational efficiency, share information with the public and improve both the quality of government services and resident welfare. Smart access is an important step forward in providing technologically advanced security management and access solutions to support the ambitions of smart cities and their respectively smart industries.
Explaining smart access
If we used the standard definition of smart, it would be to use technology to monitor, control and manage access, but the technology must be adapted to both the physical and management characteristics of smart cities.
Smart access is an important step forward in providing advanced security management and access solutions to support the ambitions of smart cities
For example, it would not make sense to install an iris biometric sensor at an isolated water storage tank, which is out in the open and may not even have electrical power. Nor would a permissions management system work, one that does not let you update permissions simply and easily and cannot be customised.
With high volumes of people entering and exiting different areas of the city, it is important to be able to trace who has been where, when and for how long. Advanced software suites can provide access to all operations performed by users, including a complete audit trail. This information is often used by business owners or managers for audits, improvements or compliance.
When initiating a new access control system it is important that the supplier and customer work together to understand:
- Who can enter a secure area
- Where in the building each individual has access to
- When an individual can enter a secure area
- How an individual will gain access to a secure area
This information can be crucial in the event of a security breach, enabling investigators to find out who was the last known key holder in the building and what their movements were whilst there.
 |
| Installing an electronic lock does not require electrical power or batteries, much less a connection to send information |
Modernising locks and keys
Installing an electronic lock does not require electrical power or batteries, much less a connection to send information, which means that it can be installed on any door as you would a mechanical lock without maintenance requirements.
Permissions are stored within an intelligent key. If you have authorisation for that lock, it will open. If you don’t, you won’t be allowed to enter and all of the activity carried out by the key will be recorded.
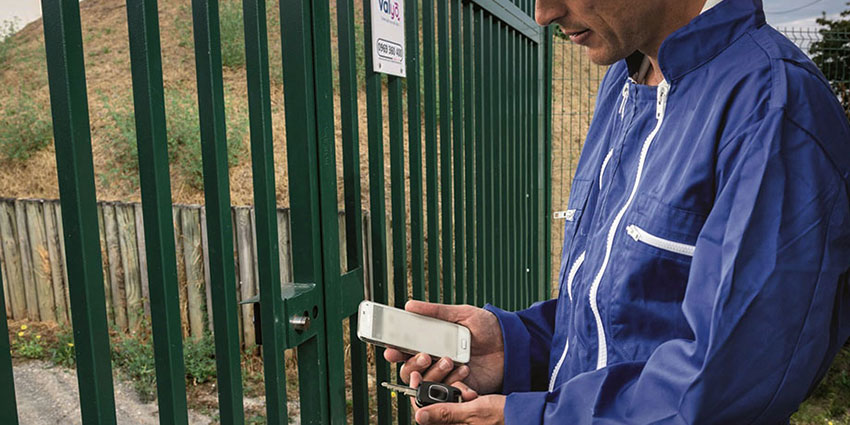
You can update permissions from a computer or using an app on a mobile phone at the time of access, which will update the key's permissions via Bluetooth. This allows shortened validity periods, constrains movements to be in line with company access policy and removes travel and fixed authoriser costs. This then delivers increased flexibility and higher levels of security.
Remote access control utilities
Access rights can be set at any time and on any day, and if required can allow access on just one specific occasion
Using an app improves access control by updating access rights in real time with the Bluetooth key. It also provides notification of lost keys, joint management of access schedules, protection of isolated workers and much more. Combined with new technological solutions, an app allows contextual information to be sent, such as on-site presence, duration of an operation, authorisations and reporting of anomalies.
Access rights can be set at any time and on any day, and if required can allow access on just one specific occasion, for example to repair a failure. Access can be restricted to enable entry only during working hours, for example.
Permissions can be granted for the amount of time required, which means that if permission is requested to access a site using a mobile app, the company should be able to access it, for example, in the next five minutes.
Once this time has passed, the permission expires and, if a key is lost or it is stolen, they will not be able to access the site. The rules for granting permissions are infinite and easily customisable, and the system is very efficient when they are applied; as a result, the system is flexible and adapted to suit company processes and infrastructures.
Using an app improves access control by updating access rights in real time with the Bluetooth key
Finding applications to create solutions
In many cases, companies themselves find new applications for the solution, such as the need to obtain access using two different keys simultaneously to prevent a lone worker from accessing a dangerous area.
The software that manages access makes it smart. It can be used from a web-based access manager or through personalised software that is integrated within a company's existing software solution, to automatically include information, such as the employee's contractual status, occupational risk prevention and the existence of work orders.
In some companies, the access management system will help to further improve service levels by integrating it with the customer information system, allowing to link it for instance with alarms managers, intrusion managers or HR processes.
With over one million access points currently secured worldwide, this simple and flexible solution will play a strategic role in the future of security.
Find out about secure physical access control systems through layered cybersecurity practices.














