Add March Networks to the growing list of companies in the physical security market that are addressing the possibility of cyber-threats. Cybersecurity is especially relevant to two of March Networks’ primary vertical markets – banking, whose focus on money requires stringent cybersecurity; and retail, which has been the target of recent cybersecurity attacks.
“People just don’t know what to do with cybersecurity,” says Dan Cremins, Global Leader, Product Management at March Networks. “The thing is, you have to figure out how to make your products, solutions and networks more secure, and then let them know what you are doing about it.”
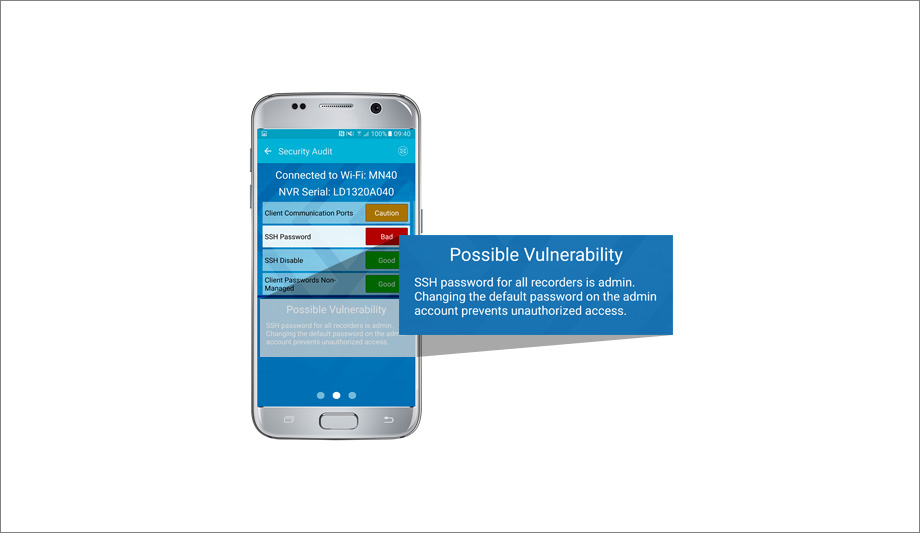
Cybersecurity mobile app
As the profile of cybersecurity has increased in the physical security market, March Networks has added cybersecurity features to its GURU app. GURU is a mobile app for integrators to use when installing and diagnosing equipment in the field. Using a wireless dongle, the system can read the QR (Quick Response) code on a camera, for example, and provide installation information specific to that camera.
As the profile of cybersecurity |
GURU’s new Security Audit tool enables the app to scan a unit and check to make sure it is cybersecure; that is, the right ports have been closed and default passwords have been changed. Simple green, yellow and red coding communicates the cybersecurity status of equipment as it is being installed – and it takes less than five minutes. After installation, the GURU app can be used to conduct an extra check to ensure cybersecurity.
There is also a section on the March Networks web site identifying security vulnerabilities (listed by CVE [Common Vulnerabilities and Exposures] number), explaining whether they affect March Networks equipment, and the availability of any patches. “Cybersecurity is the number one threat to any industry, including ours,” says Cremins. “We offer a tool to help people address it. We are trying to be as proactive as possible, and stay ahead of it.”
Integrating inventory tracking & video
There are other developments at March Networks, too, including a new integration partner in the retail sector. Tracking inventory is critical to retail loss management, and March Networks has integrated its video system with the Zebra RFID system for inventory tracking. Zebra uses radio frequency identification (RFID). Asset tags are used in combination with sensors mounted throughout a facility to keep track of where goods are transported in a retail store, warehouse or other location.
If something goes missing, |
The Zebra RFID system generates inventory tracking information that is integrated with March Networks video in much the same way that point-of-sale (POS) information has been used with video. Information from inventory tracking is associated directly with each frame of video. The integration allows video cameras to watch equipment as it moves around a warehouse or retail space. If something goes missing, video of that item, tied to tracking information from the RFID system, is available instantly to aid with an investigation.
In addition to retail, there are also applications of RFID inventory tracking in medical environments, where expensive equipment is used throughout a hospital, for example. Integration of video with inventory control would allow video cameras to watch medical equipment as it travels from floor to floor and room to room. Video provides a valuable investigation tool if a medical device goes missing. “They can review the video to see where it was and see what happened with it,” says Cremins.
HDR cameras for banking applications
At the recent ASIS show in Orlando, March Networks introduced the new ME4 series of multi-exposure, 4 megapixel cameras. The cameras are aimed at improving video image performance in situations with varied light, such as a glass-enclosed ATM enclosure, bank branch, or a retail location where bright windows can cause backlighting and other problems. In addition to better image quality and resolution, the cameras have been designed very economically, says Cremins. They strike a balance between video clarity and bandwidth and storage efficiency.
The cameras use HDR (high dynamic range) technology designed for the most extreme lighting conditions. Even in an environment surrounded completely by glass, the cameras can still see the person in the foreground and details in the background. Facial details are critical in applications at banks and financial institutions.
Find out about secure physical access control systems through layered cybersecurity practices.