LEGIC’s trusted service Connect enables everyone to securely use mobile services on smart devices – at the touch of a button.
Mobile services like mobile access, sharing economy, cashless payment or identification serve new individual or corporate concepts in daily life. Those concepts address the increasing need for efficiency and individuality as well as customer loyalty – all by integrating users via a simple app download.
Security against cybercrime
LEGIC Connect is a unique trusted service for the secure creation and instant deployment of virtual credentials to smart devices. It is a security enabler for any mobile service and fulfills their current and future need for security against hacker attacks or cybercrime.
Mobile services based on smart devices as user interface are quickly and successfully integrated anywhere to maximise convenience
By integrating LEGIC Connect into existing system infrastructures, a smartphone or smartwatch can become anything – a door opener, train ticket, time & attendance tracker, car key and much more.
Reliable data analysis
Mobile services based on smart devices as user interface are quickly and successfully integrated anywhere to maximise convenience and improve customer loyalty. All of them share three important, but difficult challenges:
Protection of “things” (and credentials) might be the most important issue when it comes to mobile service providers and is crucial when connecting users via smart devices to sensitive assets.
Fully automated business models rely on 24/7 real-time processing of credentials. They require dynamic changes in business logic and need seamless integration of an unlimited number of users.
Improved service quality and transparency due to verified and reliable data analysis which contribute to the user's business knowledge. This is the key to today’s and future service success.
End-to-end data security
Service processes are facilitated and open in respect of technology and user interface
Integrity, meaning that data must not be modified in the whole processing, is very important. Any change must be authorised, transparent and understandable. With its sophisticated end-to-end security, LEGIC Connect is the perfect choice for all services where security matters.
Personalisation, such as the choice between iOS and Android or the possibility of integrating a second factor of authentication such as PIN and/or fingerprint, is of high importance for providers and users. Service processes are facilitated and open in respect of technology and user interface. A 24x7 availability completes a convenient mobile service. LEGIC Connect offers all these features to simplify mobile business models.
Convenient security integration
LEGIC Connect is a SaaS solution, which can be used as a security enabler for any mobile service model:
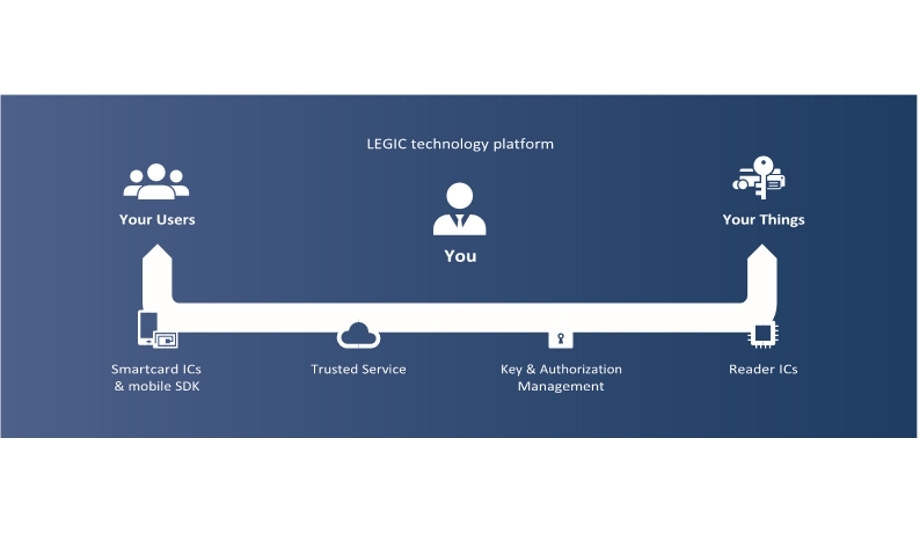
- LEGIC’s offering combines standardised basic components, which can be simply integrated into any mobile business model.
- By directly interfacing with the user's mobile business model, LEGIC’s solution serves as the easiest connection of users, things and the respective service business logics.
- LEGIC’s concept offers highest individual security standards — and so protects you against the increasing threat of hacker attacks.
- With LEGIC Connect, customer specific data packages are transferred securely. Hence, interaction is not limited to a predefined set of commands.
- LEGIC’s technology platform allows customers to combine RFID or NFC-HCE and BLE technology on the same eco-system or upgrade their business model with one or the other.
Mobile access solutions
Corporate access – Mobile ID is an addition to existing smartcard infrastructures and makes the dynamic assignment and withdrawal of access rights much easier and cost-efficient. Temporary access can be given to visitors, customers or contractors within seconds. With LEGIC Connect, these scenarios can easily be realised.
Thanks to the innovative and multi-technology platform, every user can be connected with his smart device to any “thing”
Hospitality – In the hotel industry, customer experience is most important. Mobile room keys are fundamental for several major benefits: Guests don’t need to check-in at the reception and wait for their key cards. Booking their favourite room in advance and receiving the keys directly on their smartphones or changing a room without waiting again in line at the reception are just a few to mention.
Mobility – Mobility business models like vehicle sharing, e-charging or fleet management serve new concepts for individual or corporate mobility. All of these services integrate any user via a simple app download. LEGIC Connect allows the secure creation and instant deployment of virtual car keys, fleet access rights, e-charging credentials or the like on smart devices.
Individual application – Corporate access, hospitality, mobility, residential access, etc. are just a few possible use cases. Thanks to the innovative and multi-technology platform, every user can be connected with his smart device to any “thing”.
iOS or Android integration
LEGIC Connect ensures operational security with a range of features and benefits:
- All-inclusive security enabling service
- Securely and easily connects any user to any “things”
- Specialised on mobile business models
- Integration of LEGIC mobile SDK in iOS or Android apps
- Simple integration within existing service
- Supports BLE and NFC, no matter if smart devices management system via API and/or “things” are online or offline
- Highly scalable for any size of project
- Immune against man-in-the-middle and replay attacks
- Contactless credentials can be personalised “over-the-air”
Secure business operations
LEGIC Connect integrates into customer back-end via API and supports any kind of credentials or data packages
LEGIC Connect integrates into customer back-end via API and supports any kind of credentials or data packages.
LEGIC mobile SDK enables easy integration of users with smart devices into LEGIC secured business models. It fully supports customer specific apps and white labelling solutions.
LEGIC reader ICs come with an EAL 5+ certified secure element and allow you to combine RFID, NFC and BLE technologies.
LEGIC Orbit provides customer specific key management for convenient and secure management and distribution of application keys and configurations.
Stay ahead of the trends on securing physical access control systems through layered cybersecurity practices.