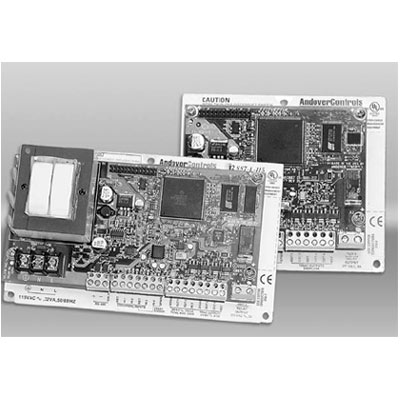
TAC i2887 Access control controller
Technical Specification
- Make: TAC
- Model code: i2887
- Series: Infinet II Series
- Controller Type: Standalone
- Networkable: Yes
The Infinet II (i2) 887 is a fully programmable, low cost, general purpose terminal controller. It has all the power of an Infinet II controller, but with a small form factor. With its unique mix of three universal inputs, one Smart Sensor/room sensor input, four triac outputs and one relay output, the i2887 can be easily configured to control Heat Pumps, Fan Coils, or AC units. Use the i2887 for direct control of fans, staged heating and cooling and monitoring of room temperature, outside air temperature, return air temperature or occupancy status.
Read more| Make | TAC |
|---|---|
| Manufacturer | TAC Satchwell |
| Category | Access Control>Access control controllers |
| Model code | i2887 |
| Controller Type | Standalone |
| Networkable | Yes |
| Communication Type | RS-485 |
| Onboard No/Type of Inputs / Outputs | 4 inputs, 6 outputs |
| Universal / Wiegand Reader Interface | Yes |
| Electrical Specifications |
Voltage: 24 V AC Power Consumption: 10 VA |
| Physical Specifications |
Dimensions mm: 111 x 130 x 30 Weight g: 230 |
| Environmental Specifications |
Operating Temp oC: 0 ~ 49 Operating Humidity %: 10 ~ 95 |
| Additional info |
The Infinet II (i2) 887 is a fully programmable, low cost, general purpose terminal controller. It has all the power of an Infinet II controller, but with a small form factor. With its unique mix of three universal inputs, one Smart Sensor/room sensor input, four triac outputs and one relay output, the i2887 can be easily configured to control Heat Pumps, Fan Coils, or AC units. Use the i2887 for direct control of fans, staged heating and cooling and monitoring of room temperature, outside air temperature, return air temperature or occupancy status. |
| Download PDF version Download PDF version | |
You might be interested in these products
Related Whitepapers
Cybersecurity in keyless access management
Three essential reasons to upgrade your access control technology in 2022
Securing unmanned infrastructure at the network edge








![$common_vars['trending_topic_article_popup'][0]->title](https://www.sourcesecurity.com/img/news/612/barracuda-920x533.jpg)
