 |
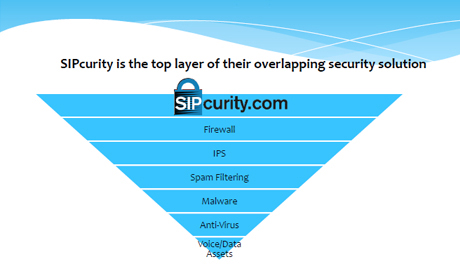
| SIPcurity is a new breed of security product that is a key element of any Advanced Threat Protection (ATP) framework |
As cyber threats continue, there’s no business or market immune from malicious takeover and data compromise. Now, systems integrators have a new, cloud-based weapon in their arsenal designed specifically as an affordable monthly subscription service to prevent telecommunications attacks and takeovers directed at small to medium businesses (SMBs).
According to the annual Ponemon Institute 2015 Cost of Cyber Crime Study, sponsored by Hewlett-Packard and released in late fall 2015, the average annualised cost of cyber-crime in the U.S. is now $15 million, up 19 percent over the 2014 report.
SIPcurity programme – simple and cost-effective
Datacom Warranty Corp. (DWC), Alpharetta, Georgia, recently announced a partnership with SIPcurity, Norcross, Georgia, to provide a cost-effective, cloud-based cybersecurity protection platform that’s a real-time solution integrated into the businesses’ existing firewall and PBX system. According to Rusty Bryan, founder of DWC, the company’s integrator-partners will now be able to provide affordable cybersecurity to the SMB market, without installing additional equipment at the customer site.
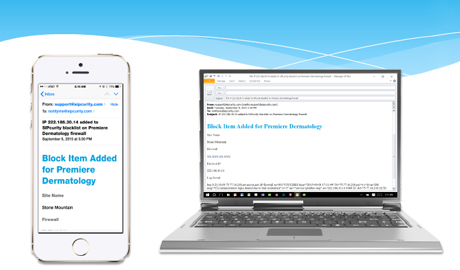
“With this service cybersecurity protection resides on the customer’s firewall and IP PBX and it blocks access to the network’s IP addresses, preventing attacks. It’s inexpensive for the reseller-partner and can be leveraged as a monthly subscription service, and simply another line item in managed services programmes. In addition, the SIPcurity programme provides regular email reports on attempted attacks, another value-add to the systems integrator and the customer, who becomes even stickier with these services,” he says.
DWC hardware warranty service
DWC’s core business provides integrators with an equipment warranty service that allows service providers to build additional recurring monthly revenue (RMR) through their service agreements and robust managed services. DWC began its hardware warranty programme, backed by sales training, marketing support, and total hardware system protection, in 1990. DWC’s Bronze Warranty™ programme helps integrators and their customers move from reactive, break-fix, time and material (T&M) services to a proactive model that takes the worries of hardware failure away from users. Now, cybersecurity can also be part of the programme.
 |
| SIPcurity protects businesses’ critical infrastructure and Internet access, detecting malicious activity, and sending out alerts when an attack is detected and blocked |
Affordable pricing, email alerts and 24/7 service
According to James Wang, Managing Partner, SIPcurity, pricing is especially affordable to SMBs who may not have internal IT staff to mitigate threats or the budget for other cybersecurity programmes on the market. “It’s affordable and there’s no additional equipment needed,” Wang says. “The monthly subscription includes updates and upgrades and is a seamless, hosted platform that has also been found to lower some insurance premiums as well,” he says.
SIPcurity is a new breed of security product that is a key element of any Advanced Threat Protection (ATP) framework, Wang continues. “The 24/7 service protects businesses by identifying, repelling and blocking cybersecurity breaches in VoIP. SIPcurity actively protects businesses’ critical infrastructure and Internet access, detecting and mitigating malicious activity, and sending out security alerts when an attack is detected and blocked.”
Protecting the communications infrastructure
SIPcurity has documented a variety of threats to the phone communications and VoIP lines at customer locations. For the systems integrator, this service could be easily applied to current customers; their own businesses; and even central station companies. The DWC and SIPcurity subscription plan targets the following end-user challenges:
- Toll fraud,
- Distributed Denial of Service (DDoS),
- Eavesdropping,
- Registration hijacking and,
- Ineffective security tools like SIPVicious and firewalls.
SIPcurity has been tracking such attacks, says Thomas ‘Hank’ Appleton, Director of Sales. “In one instance alone, Bob Foreman, a principal architect with Foreman Seeley Fountain Architecture, Norcross, Ga., got a $166,000 phone bill in a single weekend after hackers broke into the company’s phone network. Hackers had routed $166,000 worth of calls from the firm to premium-rate telephone numbers in Gambia, Somalia and the Maldives,” Appleton says.
Beyond traditional physical security, systems integrators can add value with managed services that target new challenges to the end-user market, including cybersecurity threats to communications.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems













