Biometric Security
Barracuda Networks, Inc., a trusted partner and major provider of cloud-first security solutions, announced that Neal Bradbury has been elevated to the role of Chief Product Officer. In this new role, Neal will lead a unified product, engineering, and advanced technology team to steer the vision for Barracuda’s comprehensive cybersecurity platform and drive customer-centric innovation across the entire portfolio. The platform is designed to protect customers across all attack surfaces inc...
The economic fallout of the COVID-19 epidemic was felt in supply chain disruptions, higher prices, and shortages of certain goods. The physical security industry was not spared, although the epidemic also presented opportunities for security companies. Changing access control trends triggered by the pandemic are still reverberating throughout the industry, for example. Four years later, the impact of the pandemic is still being felt in the security market, lingering like the symptoms of "long CO...
Genetec Inc., a renowned technology provider of unified security, public safety, operations, and business intelligence solutions, announced that its new enterprise-grade SaaS solution, Security Center SaaS, gives organisations the complete freedom to choose the door controllers, cameras, and devices that work best for their business. Based on an open platform architecture, Security Center SaaS enables organisations to connect direct-to-cloud with the latest Axis, Bosch, Hanwha, and i-PRO camera...
When it comes to preventing theft and ensuring overall safety, technology offers a robust toolkit for retail stores to enhance security in several ways. From intelligent surveillance systems to RFID tags used to avoid shoplifting, today’s retail and loss prevention strategies are more effective than ever. Beyond security, the newer technologies can also provide benefits related to merchandising, inventory control, customer service, and the list goes on. The combination of abundant data and...
British universities are cited as some of the best in the world; working on cutting-edge and revolutionary research. Physical security measures The Director General of MI5 and senior politicians warned last week these institutions are being targeted for their intellectual property (IP) by hostile states and spies and as a result, this is a threat to national security. In the face of this, universities must work at speed to increase their physical security measures and keep their academia and...
Gunnebo Entrance Control has announced its acquisition of DG Concept and Diadem, a French entrance control, design, installation, and service specialist, marking a significant step in reinforcing its commitment to providing innovative solutions and exceptional service to global clients. DG Concept and Diadem is a family-owned business servicing the French market, with a team committed to delivering high-quality service solutions tailored to the unique needs of its clients. Service expansion G...
News
Fingerprint Cards AB has partnered with Lapa Electric, an Indian-based premium electric mobility start-up, to bring the best security to two-wheelers and create India’s first biometric-enabled electric scooter (e-scooter). The use of e-scooters in India has sky-rocketed in recent years, and this growth is expected to continue. In 2023, the penetration rate of e-scooters in India was 13%, yet by 2030 this is projected to grow to 75%. Use of biometrics Adam Philpott, CEO of Fingerprints, comments, “Over the last 10 years, biometrics has become the preferred authentication method for consumers and businesses alike. From our phones, laptops, and payment cards to our homes and workplaces, biometrics is adding security while removing friction." He adds, "As our lives, and our vehicles, become increasingly connected, we must enhance security processes and biometrics is a natural progression to underpin the future of mobility.” Biometric smartness Users won’t have to worry about losing or having their keys stolen anymore as they become the key By replacing traditional physical keys with biometric authentication, only enrolled users will be able to use the e-scooter, drastically reducing the risk of theft. In addition, users won’t have to worry about losing or having their keys stolen anymore as they become the key. Pavan Kumar at Lapa Electric, said, “At Lapa Electric we are on the verge of bringing in a new engineering approach to E two-wheelers like for example replacing heavy steel chassis with weddings and bolts and nuts with light and robust seamless monocoque carbon fiber chassis. Now we’re replacing physical keys with biometric smartness. The resulting scooter embodies premium and performance.” Biometric sensor and algorithm Lapa Electric’s key challenge was to find the smallest sensors that could be integrated into its patented console and throttle system. This is where the engineering collaboration between Fingerprints and Lapa started. Lapa Electric’s e-scooter will integrate Fingerprints’ proven biometric sensor and algorithm. The biometric-enabled e-scooters are presently under vehicle road testing and will be launched in limited numbers by early 2025.
Global technology solutions provider - Arrow Electronics, Inc. (ARW) announced that Broadcom selected it as the sole provider for its CloudHealth from VMware offering. CloudHealth is designed to help businesses simplify financial management and operations (FinOps) across multi-cloud environments effectively. Arrow Electronics and Broadcom partnership “Arrow is pleased to build upon our strategic relationship with Broadcom by becoming the exclusive provider of the CloudHealth offering,” said Eric Nowak, President of Global Enterprise Computing Solutions at Arrow. Eric Nowak adds, “Our expansive knowledge of the Broadcom and VMware technology portfolios and our deep experience in cloud delivery and management services will help ensure a fluid transition for those partners and customers leveraging the CloudHealth offering. We are excited about the opportunity to help them continue to grow their businesses and experience the added benefits of working with Arrow.” Arrow offers sales and technical support for CloudHealth Arrow will provide sales, marketing and technical support for CloudHealth Arrow will provide sales, marketing and technical support for CloudHealth and enhance the user experience through streamlined accessibility, specialised knowledge and personalised assistance. As a result, CloudHealth partners and customers receive the most value from their investment in the platform, while Broadcom continues to invest in the innovation of CloudHealth. Arrow’s deep familiarity with as-a-service technologies “Arrow’s deep familiarity with as-a-service technologies, innovation and flexibility to explore new business models play a central role in helping Broadcom execute on our global go-to-market strategy,” says Cynthia Loyd, Vice President of Global Partner and Commercial Sales at Broadcom. Cynthia Loyd adds, “Arrow has the talent, operational excellence and reach to make CloudHealth available to more businesses in more markets, while creating additional value for those already using the offering.” CloudHealth to be available via ArrowSphere Cloud marketplace CloudHealth will be available through the ArrowSphere Cloud marketplace starting May 6. The SaaS offering is the latest addition to Arrow’s fast-growing cloud portfolio, built to give organisations of all sizes greater flexibility, scalability and affordability in managing and optimising their cloud business. There is no planned service outage to CloudHealth, including to those customers who consume CloudHealth through the AWS marketplace. Partners and customers currently using the CloudHealth offering can find more information here about how to transition their business to Arrow without interruption.
In an industry-first, Safetrust provisions employee and visitor badges directly into Apple Wallet via an email link or text message, eliminating the need to download an application. This innovative app-free approach ensures a seamless experience for people requiring access to buildings or enterprise IT systems, whether visitors, contractors, or employees. It enables the deployment of mobile credentials in minutes rather than months. Universally compatible credentials “A major barrier to adopting mobile phones for building access has been requiring people to download multiple apps on their iPhones to enter different buildings with various hardware providers,” explained Jason Hart, CEO and Founder of Safetrust. “This app download insanity has increased complexity and costs, resulting in a poor user experience." "Safetrust addresses this challenge by enabling the direct push of physical access credentials into the Apple Wallet via text message or email links, streamlining the user experience. Safetrust’s use of universally compatible credentials across multiple hardware vendors significantly reduces adoption costs for organisations.” Operational support and InfoSec Removing the need for mobile applications eliminates the expenses associated with developing Removing the need for mobile applications eliminates the expenses associated with developing, maintaining, and certifying new applications for credential provisioning. Operational support and InfoSec become much simpler when users are not required to install additional software on their mobile devices for credential provisioning. Security and policy compliance Employee and visitor badges stored in Apple Wallet possess the same high security and policy compliance levels. This includes features such as support for biometric authentication via Face ID and Touch ID, utilisation of the Apple Secure Element even in low-power situations, remote revocation of credentials, and compatibility with external biometric-on-card solutions, among other functionalities. Safetrust’s over-the-air provisioning solution supports a range of functionalities, including full-time and time-limited credentials, visitor and contractor scheduling with start and expiry times, and enterprise login with FIDO2 credentials, ensuring flexibility and security.
Matrix Comsec, a well-known producer of Security and Telecom solutions, has officially announced its presence at the SAFE West Expo. The event will take place at the Bombay Exhibition Centre, NESCO, Mumbai, from May 9th to May 11th, 2024. Matrix will be highlighting its IP Video Surveillance, Access Control, Time-Attendance, and Telecom solutions at Booth No. A-21. All-Color camera Matrix is excited to reveal its newest product lineup at the SAFE West Expo. One notable addition is the launch of its All-Color Camera, engineered to capture vibrant images even in low-light or complete darkness. Equipped with warm LEDs and housed in the same enclosure as the Turret IP Camera, these cameras facilitate effortless post-installation adjustments. Ruggedized IP camera The cameras deliver top-notch video quality, excellent low-light performance, and flexible monitoring capabilities Additionally, Matrix will showcase its recently released Ruggedized IP Camera, which meets EN50155 standards, ensuring suitability for demanding settings such as roadways and railways. These cameras deliver top-notch video quality, excellent low-light performance, and flexible monitoring capabilities, including the ability to capture images within fast-moving vehicles. Bullet and dome cameras, NVRs Furthermore, Matrix will showcase its Project Series and Professional Series Bullet and Dome Cameras, recognized for their cybersecurity functionalities aligning with OWASP ASVS 4.0 L2 standards and verified by STQC, Delhi. Additionally, the company will display its assortment of Network Video Recorders and Server-grade Enterprise-NVRs equipped with integrated VMS. GDPR-compliant access control and time-attendance One of its major highlights will be its latest feature of Whatsapp integration, providing users with real-time alerts A key aspect that sets Matrix apart in the Access Control and Time-Attendance sector is its internal manufacturing of all architectural components, which encompasses panels, door controllers, software, and readers. At the Expo, Matrix will showcase its GDPR-Compliant Access Control and Time-Attendance Solutions. One of its major highlights will be its latest feature of Whatsapp integration, providing users with real-time alerts and notifications. COSEC ARGO FACE200T, COSEC PANEL200P Moreover, Matrix will unveil its state-of-the-art facial recognition time-attendance terminal, COSEC ARGO FACE200T, renowned for its exceptional accuracy, swift identification speed, and extensive user capacity. This device provides seamless connectivity options, including PoE and Ethernet. Matrix will also showcase products such as the COSEC PANEL200P, an Access Controller Hub with the capacity to manage up to 255 COSEC door controllers and 25,000 users. Media Gateways, Hybrid PBX systems Matrix stands out as the sole OEM providing a complete suite of business communication products and solutions Within the telecommunications sphere, Matrix will spotlight its wide range of telecom offerings, which encompass Media Gateways such as SETU VFXTH0032 and SETU VTEP 4P. The lineup will also feature Hybrid PBX systems like ETERNITY GENX, alongside fully IP-based solutions like SPARK200 and the premium standard SIP phone, SPARSH VP510E. Matrix stands out as the sole OEM providing a complete suite of business communication products and solutions in the telecommunications industry. Showcasing security solutions Kaushal Kadakia, the Marketing Head at Matrix Comsec, eagerly anticipates the SAFE West Expo, viewing it as an exceptional opportunity to present groundbreaking security solutions to industry pioneers, project managers, and consultants. The objective is to comprehend individual requirements and illustrate how Matrix products can adeptly fulfill organizational needs.
Honeywell security, fire, and life safety technologies will be on interactive display at The Security Event on April 30 – May 2 in Birmingham at Stand 5/F20. The showcased Honeywell technologies help building (or facility) decision-makers and operators manage threats while improving uptimes and driving operational efficiencies all delivered within an optimal occupant experience. Security technologies In line with Honeywell’s focus on delivering robust, digitalised automation solutions, Honeywell security technologies on display include: Next-generation technologies for enterprise building video security – The latest 60 & 70 Series IP cameras and NVR offerings provide an NIS2 and NDAA-compliant, cost-effective, and more operationally efficient security solution suitable for large indoor and outdoor applications. The latest updates include a 60S multi-sensor, 60S IR PTZ with Wiper, 70S Speed Dome, and a 70S Corner camera, along with the 35S PRO NVRs. Streamlined video, access, and intrusion management solutions – Honeywell MAXPRO® Access (MPA) offers simple, scalable, and secure access control that is integrated with MAXPRO Cloud for total video, access awareness, and intrusion management across multi-site locations with real-time alarm notifications and operational visibility. More connected and automated alarm systems – Honeywell Pro-Watch® 6.5 provides robust, global integrated access control, video, and intrusion detection in a single view to help protect staff and property, optimise productivity, and comply with strict industry regulations all while reducing operational costs. Enterprise users can now retain exacqVision video systems with the latest Pro-Watch ecosystem integration, which saves time and money by avoiding manual correlation of alarms. Increased control with a scalable video system – MAXPRO® VMS 750 allows users to control, collect, manage, and present multiple video sources via a highly scalable system that can support video networks that range from single instances in a small- to medium-sized building to thousands of devices across an enterprise. It integrates with Honeywell security management solutions to leverage access control, intrusion detection systems, and powerful AI analytics. Fire and life safety technologies Honeywell’s fire and life safety technologies on display include: New technology for testing and inspecting life safety systems – Honeywell Gent Self-Test is a new range of detectors that are revolutionising the testing and inspection of life safety systems. This patented and approved self-test technology overcomes obstacles such as locked rooms, hard-to-access areas, high ceilings, and large sites, which often lead to detectors being un-tested and hidden risks potentially missed. Increased reliability and efficiency with all-in-one fire detection panel – NOTIFIER INSPIRE™, powered by Honeywell's Connected Life Safety Services (CLSS) platform is a fire control system with an all-in-one fire panel that delivers reliable protection, scalability, efficient monitoring as well as flexible and timely reporting. Cost-effective, intelligent fire control – Honeywell Morley-IAS Max, is a cost-effective, powerful, and intelligent fire alarm control panel that offers installers and end users a technically advanced range of functions that is simple to install, commission, and maintain.
HID, a worldwide pioneer in trusted identity solutions, announces the availability of its new HID Seos Essential Bundle, providing small to mid-size businesses (SMBs) in Europe with the benefits of advanced access control in an all-in-one packaged solution that simplifies installation and deployment. With HID's legacy of security excellence spanning over 30 years, the new bundle combines the latest access control technology to provide premium security and enhanced user experience at a competitive cost. HID Seos Essential Bundle “We believe that premium security should be accessible to all businesses, regardless of their size. The HID Seos Essential Bundle delivers this belief by providing smaller businesses with a solution that includes the essential features of our award-winning access control solution,” says Gerald Grattoni, HID’s VP & Head of Mature Markets, Physical Access Control Solutions. “The supporting bundle simplifies the complexities often needed for larger enterprises, offering a straightforward, cost-effective solution that equips every business with top-tier security with ease.” Key features Simplified access control Included in the bundle is a secure, certified next-generation RFID and Bluetooth® HID Signo Express reader The HID Seos Essentials Bundle offers a combination of a reader and a choice of preprogrammed credentials including support for HID Mobile Access®, making it a highly versatile solution for smaller, non-enterprise installations. Included in the bundle is a secure, independently certified next-generation RFID and Bluetooth® HID Signo Express reader which is easy to install using a simple terminal strip and Wiegand connection. Cost-effective alternative It is a more secure, cost-effective alternative to CSN-based credentials, which can be easily cloneable and breached. Compatible with all standard PACS systems, this means that SMBs have total flexibility as to the type of credential they use, preprogrammed traditional PVC cards, fobs, or even the latest smartphone solution, HID Mobile Access, and access controller of their choice. Premium security meets smaller budgets The new bundle allows SMBs to maximise the value of their security investment with a solution tailored to the budgetary constraints of most organisations of this size, without compromising on the quality or effectiveness of the access control system. Easy to order, install, and manage To aid distributors and integrators, the new bundle comes with a single part number to make for easier ordering. Credentials within the Seos Essentials bundle come preprogrammed with a unique secure number. This makes rollouts seamless, saving sales partners time and money with maintenance minimal given HID’s proven device reliability. The new HID Seos Essentials Bundle is available for sale now and will be on display at The Security Event, on April 30-May 2 at Stand 5/F40.


Expert commentary
Choosing the appropriate fingerprint technology for a given application is dependent on factors including the required level of security and matching accuracy, the desired capabilities and features, and the usability to achieve adoption and productivity goals. A successful evaluation process will help ensure that this mature and proven user authentication method performs as expected. Fingerprint biometric advantages The speed, simplicity, accuracy, and cost-effectiveness of the fingerprint method have made it among the most widely used for biometric authentication across industry sectors ranging from banking and finance, retail, and healthcare, to government and law enforcement. It performs biometric technology’s “something you are” function while offering unique characteristics that make it particularly valuable for many applications. Unique identifier The fingerprint biometric has the permanency of being reasonably stable and consistent over time Among these characteristics is the pervasiveness and special nature of the fingerprint -- almost everyone has one, and each is a unique identifier. The fingerprint biometric has the permanency of being reasonably stable and consistent over time. It is also easy to acquire, measure, and process. High adoption rate Another key attribute of a fingerprint biometric is its ability to be protected against threats ranging from abuse and misuse to theft, imitation, and substitution. When it is used with recognition techniques the resulting solution performs with a combination of accuracy, speed, scalability, and ease of use. Fingerprint biometric solutions also have the highest adoption rate among biometric authentication solutions according to an industry report published by Payments Journal. Three interrelated components There are three basic components in any fingerprint biometric system as shown in Figure 1: capture (using a sensor that can capture even the most difficult finger types); liveness detection (using the Presentation Attack Detection – or PAD – technique); and matching (including preventing rejection of a legitimate user). Biometric algorithm The sensor captures and pre-processes the fingerprint data. It must be able to successfully capture fingerprint images for a range of skin types and print conditions under diverse temperatures, humidity, light, surface oil, dust, dirt, and other environmental conditions. A biometric algorithm then extracts minutiae data about the fingerprint ridges (endings, bifurcations, islands, etc.) and their orientation and position. PAD technique Implementing a presentation attack detection (PAD) technique at this stage activates the fingerprint biometric system’s second key element: liveness detection. This verifies the fingerprint’s authenticity and that it belongs to a living person. The system’s third element – matching – occurs after the PAD-verified fingerprint dataset has been securely stored as a record, known as a template, inside an enclave with cryptographic protection. Check for liveness The corresponding template of the legitimate user is then retrieved from secure storage When the fingerprint is presented for matching, it is rechecked for liveness. The corresponding template of the legitimate user is then retrieved from secure storage and the process of matching the fingerprint with this template is executed. This must be completed accurately and without rejecting a legitimate user. Types of fingerprint sensing technologies There are four prevailing categories of sensing technologies used with fingerprint readers: optical, capacitive, thin-film transistor (TFT), and multispectral imaging (MSI). Optical and capacitive method Optical is the most mature sensor technology and offers the benefits of a compact size, good capture Optical is the most mature sensor technology, and offers the benefits of a compact size, good capture and matching performance, a small enough size to fit in most desktop environments or shared workstations, and a high level of accuracy at a cost-effective price point across all use cases. The capacitive method, on the other hand, is less prone to fake finger attempts while also offering a thin and compact size for space-limited applications, the power efficiency to support battery-operated devices, and the ability to handle both indoor and outdoor lighting conditions. TFT technology The third technology goes a step further in capture accuracy. TFT technology can accurately recognise the smallest fingerprint features with ultra-high resolution and is used either as a larger-size matrix capacitive proximity detector (capacitive fingerprint sensor) or a larger-area matrix light detector (optical fingerprint sensor). It is ideal for in-the-field mobile identification applications that require a cost-effective, ultra-slim, and lightweight solution with low power consumption. MSI technology MSI technology differs from all three approaches, projecting multiple colors of light into the finger from different angles to collect both surface and subsurface biometrics data. It captures the most difficult fingerprints of diverse demographics, in a wide range of challenging environments. HID has used this patented technology in fingerprint readers that are compliant with ISO 30107-3 PAD Level 2 for advanced anti-spoofing against fraud. The technology also improves matching and offers sophisticated endpoint security that prohibits cyber criminals from gaining unauthorised access to networks by turning fingerprint readers into secure endpoints. Best practices for technology selection Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership Much is expected of the current fingerprint solutions, including delivering a low total cost of ownership. There are three top considerations: security, suitability, and usability. Each is important and the best approach is to strike a balance between all three. Following are the questions to ask during the selection process: Security: What is the regulatory environment? Financial and government services, healthcare, and law enforcement are some examples of highly regulated sectors with elevated security compliance requirements. Are there mandates in place for advanced capturing and biometric authentication specifications? How important is it to ensure anti-spoofing through liveness detection? Will endpoint security be required so that, if the fingerprint device is hacked, no network, system, or data behind the firewall will be impacted? Suitability: Where will the biometric technology be implemented? There will be additional considerations if it is to be embedded in portable, battery-operated devices that require low power consumption. Where will the technology be used? Will it need to fit into small spaces or be used in challenging indoor or outdoor conditions and environments? Will durability be important? Some deployments will face unpredictable weather and difficult lighting conditions for image capture. Will the technology be used for mission-critical border control or a more common – and less demanding -- commercial use? Usability Is it critical that the technology easily and consistently perform capture and matching? Will there be high volumes of fingerprint captures and matches? Is “friction frustration” a concern? If so, the solution must perform matching quickly and accurately to sustain high levels of user productivity. Will the fingerprint device be used by one person exclusively, or multiple people in a shared workstation setting? How diverse is the user population? Some readers are designed to handle all types of fingerprints and diversified demographics. Different applications Fingerprint biometrics is a proven solution to address real-world challenges, each with its requirements The answers to these questions will help determine the best choice of fingerprint technology. Different applications apply fingerprint biometrics to very different use cases but in all cases. It is a proven solution to address real-world challenges, each with its requirements. For instance, in a healthcare clinician’s terminal area or a similar shared environment with limited space, a durable, low-profile capacitive sensor may be the right answer. For an organisation in a highly regulated, mission-critical environment like a bank or border control agency, advanced technologies such as MSI readers may be needed to avoid the serious repercussions of a spoofed identity or the rejection of a legitimate one. Requirements for a biometric solution These are just a few of the requirements to consider when choosing a fingerprint solution. In banking and finance, alone, fingerprint biometrics is used for applications ranging from transacting at the ATM to customer onboarding (eKYC), compliance (AML/KYC), and fraud prevention. The retail sector adds even more, including age verification, loss prevention, point of sale (POS) security, self-service checkout, and secure time and attendance. Law enforcement organisations have their unique requirements, using fingerprint biometrics for background checks, criminal booking, crime investigation, inmate management, mobile identification, and more. For government agencies, typical applications include benefits distribution, border security, citizen ID, employ authentication (SSO/MFA), and voter registration. Each application requires a thorough assessment of the best fingerprint technology for the job. The right touch The right solution will deliver the optimal balance of security, suitability, and usability Fingerprint biometric solutions empower a wide range of use cases with the simple touch of a finger. The right solution will deliver the optimal balance of security, suitability, and usability based on an analysis of criteria including specific application requirements, the characteristics and size of the user population, and challenges posed by environmental conditions. Accuracy, efficiency, and security The world faces increasingly dangerous fraud, account takeover, and impersonation threats. As industries and enterprises work to improve and evolve their identity and access strategies to combat these threats, fingerprint biometrics continue to prove their value through solutions that meet the key selection criteria while delivering the highest levels of accuracy, efficiency, and security.
With the rise of organised retail crime (ORC) making headlines, retailers are grappling with the dual challenge of safeguarding both their staff and store assets, while addressing the economic pressures that impact profitability and consumer demand. RFID technology The key lies in identifying effective solutions to counter the current surge in ORC, enabling retailers to secure their vulnerable staff and protect inventory for paying customers. Technology plays a crucial role in supporting brands on this mission, with RFID technology continuing to be a valuable solution. It aids retailers in gaining better control over retail crime, leveraging inventory data. The ongoing surge in retail crime Inflation has elevated the challenges around affording items, prompting criminals to target the retail sector Seen as a global issue, the British Retail Consortium recently reported that incidents of theft have increased by 27% across 10 of the largest cities in the UK, with some cities reporting up to a 68% increase. In the US, retailer Target reported an inventory loss of $500 million for 2023, amounting to a 100-basis point hit to gross margins in 2023. The current surge in theft is not attributed to a singular cause. Inflation has elevated the challenges around affording items, prompting criminals to target the retail sector. Lack of preventive measures A significant contributing factor is the lack of sufficient preventive measures by law enforcement, which in some cases has led to a rise in more severe incidents. However, the implementation of technologies like RFID allows retailers to efficiently build cases against criminals, putting them in a stronger position when it comes to reporting thefts. Not all retail crimes are orchestrated by large entities or executed through sophisticated methods. Some stores have seen a reduction in staff numbers and, as a result, there are fewer people on the shop floor, making it easier for shoplifters to carry out their activities unnoticed. The true impact of retail crime Over 70% of retailers believed the threat of ORC had increased over the past five years, according to a recent survey The impact of retail crime on businesses extends beyond financial and economic consequences; it has also led to a surge in violence against retail staff, an ongoing trend elevated by the pandemic. Over 70% of retailers believed the threat of ORC had increased over the past five years, according to a recent survey conducted by the National Retail Federation. This escalation in violence not only results in immediate repercussions but also contributes to long-term mental health issues for staff, fostering an atmosphere of insecurity that has compelled some retailers to close their physical stores. Policy implementation Given the challenge of staff retention across various businesses, addressing retail crime becomes an even more urgent matter. Additionally, retailers are wary of their employees facing potential danger and the prospect of legal action. Consequently, many have implemented policies prohibiting employees from actively intervening when confronted with shoplifters. Privacy concerns with facial recognition Retail crime also affects customers, as businesses seek to offset losses by raising prices Retail crime also affects customers, as businesses seek to offset losses by raising prices, further burdening financially strained consumers. The presence of visible security systems not only makes stores more hostile but also diminishes the overall customer experience. While facial recognition technology is considered a potential solution, privacy concerns have emerged in its various applications. Today’s problems, yesterday’s solutions Retailers are resorting to historic measures such as steel cables, physical monitoring, or plastic screens to resolve customer issues. However, the reality is that these solutions are unfit for solving the problem, causing friction for both customers and staff. Digital solutions The newer approach involves equipping retail staff with body cams and providing new training The newer approach involves equipping retail staff with body cams and providing new training to deter shoplifters. Some stores are even offering the police discounted food and beverages to encourage their presence. The responsibility lies with management teams to seek effective solutions. In an era dominated by data and technology, retailers must shift their focus from traditional security methods to digital solutions that align with the challenges of today’s society and modern retail environments. Shrinkage When discussing theft or organised retail crime, retailers commonly use the term "shrinkage," referring to not only theft but the broader issue of lost inventory. Additional drivers of shrinkage include damage, fraud, and internal theft. A significant problem arises as losses are often based on guesswork and estimates rather than concrete numbers. Retailers may lack a comprehensive understanding of their inventories, further increasing the issue of shrinkage. Combating shrinkage Utilising RFID technology notably helps in boosting inventory accuracy Some retailers still struggle with limited knowledge of the whereabouts of items, a challenge heightened by the issue of shrinkage. Utilising RFID technology notably helps in boosting inventory accuracy. This enhancement enables retailers to obtain a clearer understanding of their inventory and the precise locations of items. Comprehensive strategy Changes in the in-store experience have highlighted the relevance of RFID, especially as self-service checkouts encounter double the shrinkage levels compared to traditional checkout stores. To combat retail theft effectively, a comprehensive strategy should involve the integration of labels, deactivation, electronic article surveillance, and data analytics. This combination works synergistically to reduce shrinkage and enhance product availability. Retail data analytics platforms RFID data can swiftly alert nearby stores, providing an opportunity for staff to monitor shop floors Linking hardware to an underlying data analytics platform empowers retailers to make more informed decisions. Retail data analytics platforms delve into alarms, deactivations, and visitor metrics, providing a deeper understanding of theft patterns. RFID technology drives efficiency by pinpointing frequently stolen items, allowing for the identification of theft patterns. In instances of flash mobs in major metropolitan areas, RFID data can swiftly alert nearby stores, providing an opportunity for staff to monitor shop floors and incoming customers. Real-time optimisation The crucial question remains whether both shoppers and retailers are prepared to shoulder the responsibility for these additional precautions. Nevertheless, these changes leverage data more effectively, optimising loss prevention strategies almost in real-time rather than relying on biannual inventory counts, therefore transitioning from static to dynamic loss prevention. Holistic approach Striking a balance between security measures and providing a seamless shopping experience is key In a retail environment, not all items require protection, and prioritising the safeguarding of the most frequently stolen and valuable items can significantly impact shrinkage. A holistic approach to retail theft is imperative, considering the entire journey of an item through the retail environment. Striking a balance between security measures and providing a seamless shopping experience is key. Protection without hindrance As stores move towards being checkout-free, retail criminals (or ORC gangs) will be presented with lucrative opportunities to steal, so retailers need to be one step ahead by introducing unobtrusive and effective technology solutions. For example, case building can be improved with item-level data. RFID data offers a more precise means of assessing the value of stolen items compared to relying solely on CCTV. It provides detailed insights into the specific items removed from the store and the timing of these incidents. This proves beneficial in tracking repeat offenders. Increased visibility with a proactive approach The modern retail environment continues to evolve and criminals are never far behind. RFID technology plays a crucial role in minimising shrinkage by enhancing inventory visibility. Moreover, it leverages the power of data to stay ahead, enabling better predictions of retail crime and the formulation of prevention strategies. This proactive approach allows for the implementation of more tailored solutions to alter outcomes positively.
As we head into a new year, it’s fair to say that it isn’t easy out there for the security integrator community. That’s understandable given the big ruptures felt in the market for physical security in 2023. Typically, Commercial Real Estate (CRE) landlords are the biggest and most influential buyers of physical security hardware and software, but this is starting to wane as heightened borrowing costs and biting inflation cause real estate valuations to plunge. Building security upgrades A lot of CRE landlords are in a fight for survival which unfortunately doesn't leave much room for budget spend on building security upgrades. This state of affairs is a problem for security integrators with extensive connections in the CRE space. Where do they pivot their services to keep their business growing in 2024? From the conversations I’ve been having with integrators and customers alike over the past few months – the answer is that the growth potential lies in the enterprise space. The trajectory of enterprise IT and physical security Aren’t enterprises carrying out cost-cutting efficiency drives and downsizing office space to reflect hybrid working It might initially feel unnatural to see the enterprise segment as a potential driver of demand for physical security services and products. Aren’t enterprises carrying out cost-cutting efficiency drives and downsizing office space to reflect hybrid working habits? These things are true but also present an opportunity for the right physical security proposition. Standardisation of enterprise IT Take efficiency drives as an example. A key element of such efforts is an acceleration towards the standardisation of enterprise IT platforms, hardware, and solutions, using the cloud. What was once a focus on moving on-prem systems and workloads to the cloud has shifted to efforts to keep cloud OpEx costs down by centralising as much as possible. Practically, this means utilising APIs to plug disparate IT applications and services into central platforms that boast a “single pane of glass” view. APIs APIs drive consumption, open new business models, and foster cross-industry partnerships APIs aren’t anything new to enterprises. They drive consumption, open new business models, and foster cross-industry partnerships. However, the use of APIs in the physical security sphere has been surprisingly slow to take off. There are multiple elements to this but a key reason is that some security software products on the market aren’t cloud-based. Adding cloud-based solutions to network Others are cloud-based, however, and these are the solutions that security integrators need in their portfolio to serve the influential enterprise market segment and its approach to IT networks. Selling the value of these solutions requires integrators to take it a step further by speaking the language of the enterprise IT buyer and understanding their goals. The power of cloud-based access control in the enterprise Hybrid working and the occupancy rate fluctuations it brings require closer monitoring of access events The continued relevance of physical security for enterprises can’t be understated. After all, hybrid working and the occupancy rate fluctuations it brings require closer monitoring of access events – not less. Despite the discourse around office downsizing, the reality for most enterprises is that the office can’t be done away with completely and there’s always going to be growth experienced by successful companies that require an upgrade in physical square footage. Physical security Access control systems that are cloud-based will be preferred by the enterprise to fulfill the essential function of physical security. That’s because they align with the push towards centralisation in the cloud that enterprises are carrying out business-wide. Access control has the potential to result in lots of disparate dashboards and apps. Think video management, license plate recognition, building management software, elevator monitoring, hot desking solutions, guest booking software, room booking functions, and more. Uniting all of these functions in one platform suits enterprise security teams well. Access control solutions Linking employee databases to an IAM solution, or creating seamless experiences by tying access credentials But this only scratches the surface. Access control solutions that can be integrated with hugely popular corporate software applications like Okta, Azure Active Directory, and Google Workspace quickly catch the eyes of enterprise IT security teams by pulling in the same direction as the broader tech stack. Whether it’s applying AI analytics to anomaly detection, linking employee databases to an Identity Access Management (IAM) solution, or creating seamless experiences by tying access credentials to things like meeting room bookings, it’s through APIs that cloud-based access control can thrive in an enterprise setting. Security integrators It’s worth also noting that as enterprises grow, access control gets harder. Managing the access requirements of thousands of employees across a global real estate footprint requires the scale that cloud computing is best placed to bring. Security integrators who can join the dots to make that link are well positioned to pivot toward the enterprise. Broadening horizons Concepts like smart access and applying AI to access data to automate the monitoring of occupancy rates This pivot is understandably a daunting prospect but the potential for natural synergy shouldn’t be overlooked. Concepts like smart access and applying AI to access data to automate the monitoring of occupancy rates and security anomalies won’t be completely alien to cloud-first enterprises. That’s an opportunity for integrators to upsell more sophisticated security set-ups in a way that they may have found more difficult with CRE clients and prospects. Tailored propositions It would be remiss to avoid mentioning that ‘enterprise’ is a very loose term that encompasses businesses across multiple industry verticals. To better pivot, security integrators need to offer tailored propositions specific to set verticals that cover all bases as opposed to offer, for example, piecemeal alarm or video product solutions. Enterprise industry verticals Security integrators should be weary of all-encompassing narratives in 2024. Whether or not the global economic picture darkens, there are always going to be pockets of growth within certain enterprise industry verticals. Plus, anecdotally, the indicators point to enterprises being the driver of demand for cloud-based access control as we head into the new year. Integrators who can dial into that shift have a lot to gain and nothing to lose.
Security beat
Security professionals are recognising the intelligence value of leveraging publicly and commercially available information. This information can now be accessed more effectively from typically hard-to-reach regions. Also, the technological capabilities have matured in our age of artificial intelligence, machine learning, and data science. Intelligence has historically been based on classified data. However, today’s unclassified data, including open-source intelligence (OSINT), is increasingly being used to provide context and queuing for other types of intelligence. Advanced identity intelligence Babel Street is a technology company providing advanced identity intelligence and risk operations using an AI-enabled data-to-knowledge platform to unlock insights from a flood of data. The company provides advanced data analytics and intelligence for the world’s most trusted government and commercial organisations. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally The sheer volume of data is growing exponentially. Experts have predicted that by 2025 over 463 exabytes of data will be generated each day globally. Not only are we seeing exponential growth in the volume of data, but there is also disparity in the veracity and the variety of data. This is being compounded by the ‘app economy’ in which data is created in a new format for every app added around the globe. Human language technology “The problem is that the data ‘junk’ and the ‘crown jewels’ are in the same bucket, and government and commercial entities need better and faster ways to extract intelligence from these torrents of data,” says Farid Moussa, VP, Strategy & Public Sector, Babel Street. Prior to joining Babel Street, Farid retired from the National Security Agency (NSA). He has guided video, image, speech, and text analytics (VISTA) and developed an appreciation for human language technology. An elusive source of data is the Dark Web, where every user, by design, is attempting to obfuscate their identity, and bad actors are hiding much better. “This presents a cat and mouse game – the cat must be smarter than the mouse, but the mouse is continually getting smarter,” says Moussa. Intelligence tools for data analysis SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence There are several intelligence tools for analysing data. One of them is signals intelligence (SIGINT), which refers to electronic transmissions collected by ships, planes, ground sites, or satellites. Another is human intelligence (HUMINT), which is collected in a human-to-human fashion. Open-source intelligence (OSINT) is obtained by searching on topics or entities of interest that are publicly available on the Internet at large. Today, these various categories are often done in ‘silos of excellence.’ However, the best practice is using all forms together in a holistic fashion. SIGINT and HUMINT – while both vital – are also the most expensive forms of intelligence, while OSINT, which is growing in importance, is most cost-effective. All are vital forms of intelligence; OSINT is complementary and crucial to holistic intelligence practices. Holistic intelligence practices When it comes to physical security of people and places, OSINT has become a critical source of actionable information. Security directors leverage Publicly Available Information (PAI) to safeguard against threats to individuals, property, travel routes, and event sites. By monitoring PAI, security teams can detect and respond to potential dangers, including during and after events where thorough preparation is vital. Online information can contain warning signs of impending threats. It informs security professionals in uncovering digital traces, confirming intentions, and addressing risks across language barriers, ensuring proactive risk management for the protection of people and property. Role of Natural Language Processing (NLP) The Internet and social media were mostly English language by default, but that has changed exponentially Natural Language Processing (NLP) is a crucial capability that has evolved to recognise the richness and variety of words and names in multiple languages and scripts, and their use across cultures. Using machine learning and linguistics algorithms, the technology simultaneously considers numerous types of name variations. At one time, the Internet and social media were mostly English language by default, but that has changed exponentially. Babel Street’s world-class entity matching technology measures over 100 features to calculate the similarity of entities across multiple languages. Despite advances in data management and the cloud, there are still multiple challenges and complexities with integration of these data elements. Challenges include spelling variances/phonetics, language translation issues, criminal evasion, human error upon input, typos, etc. Accessing data from a scattered landscape While there have been advancements in cloud technologies, agencies utilising open-source data are typically working within a highly scattered data landscape and must use a wide array of tools to get at the relevant pieces. This fragmentation makes it difficult to run analytics and apply AI and machine learning at scale in order to derive actionable insights. Unstructured and relationship data are visualised through advanced link analysis As with many disciplines, artificial intelligence (AI) is changing the game when it comes to intelligence. NLP and AI algorithms are employed to enhance datasets for greater quality, usability, and completeness. Unstructured and relationship data are visualised through advanced link analysis, geographic heat maps, influential entity carousels, topic clouds, and patterns by time and day. Geographic heat maps The advanced algorithms accurately score and prioritise critical entities within the relationship network while providing the citations from which an AI/ML-based decision was made. “With the democratisation of AI, the world is becoming flat,” says Moussa. “Just like the most prosperous countries, even the poorest countries have the most advanced capabilities to do damage. Third-world economies often present a scenario where the financial gain of nefarious schemes and low-to-no regulation combine to incentivise bad actors.” The Challenges of Name Matching Identity has been an ongoing challenge for intelligence analysis due to the vast complexity of linguistics, spelling and cultural variances, human error, as well as human evasion. Technology and data science approaches are maturing, however machine translation can still struggle with meaning. The best-of-breed natural language processing capabilities run against the data while it still is in its native language. This minimises the occurrence of analytic errors caused by inaccurate machine translations. This minimises the occurrence of analytic errors caused by inaccurate machine translations It’s tempting to think that name matching is like doing a keyword search. The complexity of language makes it more challenging. New names are constantly created, with multiple spellings and no set of rules to encompass how names are formed. They are variable across languages, scripts, cultures, and ethnicities. Culturally specific nicknames and aliases add to the complexity. Replacing human involvement The investigation of the Boston Marathon Bombing in 2013 spotlighted an example of the significance of intelligence analysis. Even though the FBI had issued a detain alert for Tamerlan Tsarnaev back in 2011, Tsarnaev managed to travel to Russia in January 2012; and in July 2012, he returned to Boston. He was not detained on either occasion because there were too many names on the lists, and Tsarnaev’s last name had been spelled differently from the way it was on travel documents, thus enabling him to get through security. With the Internet, social media, and the dark web, there’s been an exponential increase in public communications in various languages, adding significantly to the amount of analysis required to keep societies safe. Name matching, using AI, analyses multiple contextual data points across languages to arrive at matches. Name matching, using AI, analyzes multiple contextual data points across languages to arrive at matches A common misconception is that this technology will replace human intelligence. “It’s more accurate to recognise its role as a force-multiplier, allowing humans to focus on the on the harder problems and/or vetting the results of AI,” says Moussa. “The technology can efficiently analyse massive volumes of data and distill it into actionable information in a timely manner. It augments human capabilities, enabling analysis at speed and scale beyond human capacity, without replacing human involvement.” Commercial Technology to the rescue “When it comes to threat and identity intelligence, we face a risk-confidence gap, underscored by the challenge of integrating traditional tactics with the modern digital landscape,” adds Moussa. “We cannot ‘hire’ our way out of this problem. Instead, it is imperative that we adopt technology to scale our efforts and free humans to solve the harder problems that machines cannot solve yet.” The public sector loves to build things, but there are time-to-value and return-on-investment considerations to the ‘build or buy’ decision. When commercial technology can be leveraged by government, it frees resources up to work on problems that the commercial world hasn’t yet figured out, says Moussa. “The public and private sectors need to come together – one team, one nation, working together with mutual trust and collaboration,” he says.
In the competitive world of physical access control, Big Tech companies are seeking to play a larger role. Physical access competition Apple Wallet continues to stake its claim on mobile credentialing. Amazon One Enterprise is pushing a palm-based identity service. Google/Nest offers smart locks for home access control, with identity and access management provided in the Google Cloud. The entry of these big companies in the historically fragmented physical access control market is causing disruption and foreboding new levels of competition. Apple Wallet impacting credentialing trends The popularity of mobile wallets and contactless technologies in general has grown, creating more demand At Apple’s Worldwide Developer Conference in June 2021, the company announced support for home, office and hotel keys, including corporate badges and student ID cards, in Apple Wallet. Later, the company announced Hyatt as the first hotel partner to support the technology. Since then, the popularity of mobile wallets and contactless technologies in general has grown, creating more demand for a seamless solution such as Apple Wallet. Easy access In 2023, HID Global announced the availability of their employee badge in Apple Wallet, allowing staff and guests to easily access corporate spaces with their iPhone or Apple Watch, including doors, elevators, turnstiles, etc. Employees just need to hold their iPhone or Apple Watch near the reader to unlock. Factors affecting the rate of adoption However, implementing and maintaining an Apple Wallet-based access control system can incur costs for hardware updates, software licencing, and ongoing maintenance. Factors affecting the rate of adoption include the need to upgrade existing infrastructures to accommodate the technology, and the necessity for access control manufacturers to develop and implement integrations with Apple Wallet. Benefits of adoption Keys in Apple Wallet take full advantage of the privacy and security built into the iPhone and Apple Watch With larger companies leading the way, some smaller ones might take longer to catch up. There is also a need to educate building owners and administrators to see the value and benefits of switching to Apple Wallet-based access control. Convenience and greater security can accelerate adoption. Keys in Apple Wallet take full advantage of the privacy and security built into iPhone and Apple Watch. Sensitive data protection A compatible app, specific to the building’s access control system, is needed. Once added, credentials are securely stored in the iPhone's Secure Enclave, a dedicated hardware chip designed for sensitive data protection. Holding an iPhone near an NFC-enabled reader enables transmission of encrypted credentials. In addition to Near Field Communication (NFC), some systems also utilise Bluetooth Low Energy (BLE) for added security, longer read range, and hands-free unlocking. Phones need sufficient battery charge to function. Amazon One Enterprise Enables Palm-Based Biometrics In November 2023, Amazon Web Services Inc. (AWS) announced an identity service providing comprehensive and easy-to-use authentication for physical and digital access control. The system enables users to employ their palm as an access control credential, allowing organisations to provide a fast and contactless experience for employees and others to gain access to physical locations as well as digital assets. Physical and digital locations Physical locations include data centres, office and residential buildings, airports, hotels, resorts Physical locations include data centres, office and residential buildings, airports, hotels, resorts, and educational institutions. IT and security administrators can easily install Amazon One devices and manage users, devices, and software updates using AWS’s Management Console. Elimination of physical credentials An advantage of the Amazon approach is the elimination of physical credentials such as fobs and badges, and digital elements such as personal identification numbers (PINs) and passwords. AWS says security is built into every stage of the service, from multi-layered security controls in the Amazon One device, which is the same technology used in the Amazon Go retail stores, where shoppers can pay for purchases by scanning the palm of their hands. The devices combine palm and vein imagery for biometric matching and deliver an accuracy rate of 99.9999%, which exceeds the accuracy of other biometric alternatives, says the company. AI and ML The palm-recognition technology uses artificial intelligence and machine learning to create a “palm signature” that is associated with identification credentials such as a badge, employee ID or PIN. Boon Edam, a revolving door and turnstile manufacturer, offers Amazon’s palm biometric technology on its equipment, and IHG Hotels & Resorts uses the technology to provide employees a convenient way to identify themselves and gain access to software systems. Google and Nest Devices in Access Control When the Nest × Yale Lock is connected to the Nest app, a resident can unlock a door from their phone Google’s Nest devices include smart locks for home access control. The Google Nest × Yale Lock allows access control via both physical keys and passcodes accessible through the Google Home app. When the Nest × Yale Lock is connected to the Nest app, a resident can unlock a door from their phone. Passcodes can be created for family, guests, and other trusted persons. Alerts can be provided whenever someone unlocks and locks the door. When Nest “knows” a resident is away, the door can lock automatically. Voice control, Google Home app Voice control, using Google Assistant integrated with various Nest devices, enables use of voice commands to lock and unlock doors, thus adding another level of convenience. Smart home devices from various manufacturers can be controlled through the Google Home app. SMART Monitoring ADT’s Self Setup smart home security systems integrate Google Nest smart home products with ADT security and life safety technology, including SMART Monitoring technology. Microsoft Azure is another company that could impact access control. The Microsoft Azure Active Directory is an identity and access management platform that could be extended to physical access control, leveraging existing user credentials. Long-Range Impact on the Security Marketplace Big Tech companies are creating platforms for managing access control data, integrating with other security systems Increasingly, Big Tech companies are creating platforms for managing access control data, integrating with other security systems, and offering analytics for optimising security and building operations. Big Tech is also actively researching and developing new technologies for access control, such as facial recognition, voice authentication, and AI-powered anomaly detection. Access control communication and integration As their involvement in physical access control grows, Big Tech companies could potentially gain more influence in setting industry standards for access control communication and integration, similar to how they have become dominant in other areas such as mobile platforms. Given their expertise in user interface design and data analysis, Big Tech companies could help to direct how future access control systems are managed and how users interact with them, including more intuitive and user-friendly operations. Future of physical access control Existing concerns about privacy, security, and potential dominance by a few Big Tech companies could spill over into physical access control. However, traditional security companies, startups, and industry consortiums are also actively developing innovative solutions. Ultimately, the future of physical access control will likely be shaped by a combination of many different players and technologies – large and small.
The sale of Carrier’s Global Access Solutions to Honeywell in December amounted to a dramatic finish to a big year in 2023 for mergers and acquisitions (M&A) in the physical security market. In the transaction between two industry giants, Honeywell sought to enhance and strengthen its building automation capabilities with the acquisition of Carrier’s Global Access Solutions business for $4.95 billion, in an all-cash transaction. Honeywell acquires Carrier Access business The acquisition, which includes both hardware and software solutions, will mean a new corporate owner for the LenelS2 brand, a pioneering business for over 25 years in commercial and enterprise access solutions, including well-known offerings Onguard and Netbox. In addition, the acquisition covers the Onity brand of electronic locks, including hospitality access, mobile credentials, and self-storage access; and the Supra brand of cloud-based electronic real estate lockboxes. ADT sells commercial business, which rebrands as Everon ADT Inc. announced the sale of its commercial security, fire, and life safety business unit to GTCR ADT Inc., another industry giant and a trusted brand in smart home and small business security, announced the sale of its commercial security, fire, and life safety business unit to GTCR, a private equity firm, for a purchase price of $1.6 billion. ADT Commercial, a security integrator and premier provider of commercial security, fire, and life safety in the United States, announced that it will move forward as a standalone organisation and rebrand as Everon. Bosch to sell building technologies products Bosch Building Technologies announced in 2023 that it is realigning its Building Technologies division to focus solely on its regional integrator business, with solutions and services for building security, energy efficiency, and building automation. Therefore, Bosch plans to sell most of the Building Technologies division’s product business. At year-end, Bosch was seeking a buyer who would take on all three business units with their associates and locations. This includes the Video, Access and Intrusion, and Communication business units, and affects some 4,300 associates at more than 90 locations worldwide. Building its integrator business earlier in 2023, Bosch announced the acquisition of Paladin Technologies, Inc., headquartered in Vancouver, Canada, a provider of security and life safety solutions and system integration services in North America. Motorola acquires IPVideo, creator of HALO Sensor In another deal emerging late in 2023, Motorola Solutions acquired IPVideo Corp., Bay Shore, N.Y., the creator of the HALO Smart Sensor, an all-in-one intelligent sensor that detects real-time health and safety threats. The powerful capabilities of the HALO sensor extend Motorola’s end-to-end physical security offering by integrating a non-video threat detection product into the safety and security ecosystem. IDIS acquires Costar Technologies Costar has a sales channel of over 100 distributors and 1,000 systems integrators across the U.S. Korean video manufacturer IDIS and U.S. company Costar Video Systems had enjoyed a long-term existing ODM (original design manufacturer) relationship, and approximately 60% of Costar Video products were already made by IDIS. Therefore, it made sense when IDIS Co., Ltd. and Costar Technologies Inc. announced an agreement and plan to merge, with IDIS acquiring Costar. Leveraging Costar's established distribution networks and sales channels in the U.S. gives a significant boost to IDIS' growth strategy, which is founded on building long-term relationships with systems integrators. Costar has a sales channel of over 100 distributors and 1,000 systems integrators across the U.S. that will benefit from IDIS’ NDAA-compliant and 100% Korean-made technology. SECOM invests in Brivo and Eagle Eye Eagle Eye Networks, a cloud video surveillance company, and Brivo, a provider of cloud-based access control and smart space technologies, announced one of the largest investments to date in cloud physical security in 2023. SECOM CO., LTD, based in Japan and one of the largest security integration companies in the world, has made a primary equity investment of $192 million in the two companies, $100 million in Eagle Eye Networks, and $92 million in Brivo. $100M primary equity investment Brivo will also use the additional investment to continue expanding in Europe, Latin America, and Asia Pacific Eagle Eye Networks, a global pioneer in cloud video surveillance, announced it will use the $100M primary equity investment to expand its suite of AI-powered products, fund geographic expansion, and enhance its enterprise features. Brivo will use the investment to grow sales and marketing, accelerate product development scale support and operational functions, and evaluate strategic acquisitions. Brivo will also use the additional investment to continue expanding in Europe, Latin America, and Asia Pacific, and enhance the smart spaces and AI functionality in the Brivo Access Platform. ACRE buys PremiSys Portfolio ACRE, a security company built on acquisitions, is continuing to broaden its portfolio and serve the expanding needs of its customer base. In 2023, ACRE acquired the PremiSys software and hardware portfolio and assets from IDenticard. PremiSys’ technologies enable organisations to self-manage door access and view integrated video and lockdown facilities. The acquisition extends opportunities for ACRE in healthcare, education, data centers, and senior living facilities. Qognify is a part of Hexagon Qognify extends Hexagon’s real-time monitoring and security reach to detect, assess, and respond Qognify, a provider of video (VMS) and enterprise incident management (EIM) solutions announced that it has become a part of Hexagon. Qognify joins the Safety, Infrastructure & Geospatial division of Hexagon, following the completion of its acquisition originally announced on Dec. 19, 2022. Qognify extends Hexagon’s real-time monitoring and security reach to detect, assess, and respond to incidents, providing a more robust offering. ASSA ABLOY continues acquisition trend ASSA ABLOY continued to acquire companies in 2023 to strengthen its position in mature markets by adding complementary products and solutions to the core business. Among the companies acquired in 2023 were Ghost Controls, a U.S. supplier of automated residential gate openers, and Securitech Group, a manufacturer of high-security mechanical and electronic door hardware products in the U.S. Door and fencing ASSA ABLOY also acquired Leone Fence, a Canadian manufacturer, distributor, and installer of fencing products for commercial and residential applications, and Lawrence Hardware and Gallery Specialty, providers of commercial hinges, locksets, exit devices, and door hardware accessories in Canada. Another new acquisition is Inovadoor Portas Industriais Ltda, a Brazilian manufacturer of sectional and high-speed doors. Earlier in 2023, ASSA ABLOY completed the acquisition of Spectrum Brands’ Hardware and Home Improvement division and the divestment of Emtek and the Smart Residential business in the U.S. and Canada to Fortune Brands.
Case studies
San Luis Obispo (SLO), the gem of California's central coast, is renowned for its picturesque vineyards, historic architecture, and vibrant community life. Quiet but lively, it is also home to the California Polytechnic State University, located halfway between San Francisco and Los Angeles. Ensuring safety and security Because of its distance from major metropolitan areas, SLO has retained its rural, small-town character, along with a bustling downtown and beautifully preserved Spanish Mission. The San Luis Obispo Police Department (SLOPD) is focused on ensuring safety and security across expansive terrains, reducing crime, and enhancing the quality of life while upholding the principles of service and integrity. The challenge The secluded Reservoir Canyon is just one area that has been a hotspot for vehicle break-ins For San Luis Obispo, two priorities were crime prevention and the protection of sprawling outdoor spaces popular for hiking and biking. Hidden from public view, the secluded Reservoir Canyon is just one area that has been a hotspot for vehicle break-ins. However, its remote nature made installing a traditional security system nearly impossible. The initial cost to secure three city parking structures was also cost-prohibitive, with quotes of over $1 million for network connectivity alone. Need for a robust and reliable solution "We've dealt with products that were essentially consumer-grade equipment repackaged as professional security solutions,” said Chad Pfarr, Administrative Lieutenant. "We needed a more robust and reliable solution. Creating our own was time-consuming and beyond our expertise, highlighting the need for a specialised, cost-effective solution.” Why Verkada A system that could operate in remote locations, areas typically beyond the reach of standard CCTV “We were drawn to the hardware and software quality. But what truly set Verkada apart was the willingness to innovate in ways that traditional security solutions did not. We can now bring Verkada devices into the wild, in the middle of nowhere, without traditional city network infrastructure." A system that could operate in remote locations, areas typically beyond the reach of standard CCTV technology was a leap forward for community safety. Use cases include: Protecting remote locations with the GC31 Cellular Gateway. Licence Plate Recognition (LPR) monitoring to streamline vehicle investigations. Protecting evidence in cold storage with Air Quality Sensors. Improving check-in and registrant compliance with Workplace solutions. "Verkada's willingness to venture into uncharted territory with us to ensure security systems could be deployed where they were most needed, regardless of existing connectivity, was what got us so excited. Beyond just adapting to what’s available, it’s continuously improving to meet our needs." Protecting remote locations with the cellular gateway In San Luis Obispo, the GC31 Cellular Gateway bridges the gap between the need for remote security and limited infrastructure. The police department protects areas previously deemed inaccessible without the high costs of traditional network installations, leading to savings of over $1 million for connectivity alone. Bridging the connectivity gap "Before Verkada, the idea of installing a security system in remote locations was a logistical nightmare. The cost of establishing connectivity alone was prohibitive, not to mention the technical hurdles of operating without power or a network." "But with the Cellular Gateway, we've been able to overcome these barriers, bringing security and peace of mind to once vulnerable areas." Licence Plate Recognition (LPR) capabilities SLOPD can install Verkada products in locations that are hard to wire or lack connectivity SLOPD can install Verkada products in locations that are hard to wire or lack connectivity, such as parking lots, construction sites, trailheads, and natural terrain. Within the city, the GC31 also protects busy intersections by supporting cameras with Licence Plate Recognition (LPR) capabilities. Streamline vehicle investigations Paired with the cellular gateway, CB62 outdoor bullet cameras are deployed on streetlight poles to monitor moving traffic, covering up to three lanes with a single camera. Using Verkada’s edge-based processing and computer vision technology, the LPR solution captures licence plates at speeds of up to 80 mph (128 kph). Flexibility and versatility The cameras' versatility in both covert and overt operations allows SLOPD to adapt its security tactics The cameras' versatility in both covert and overt operations allows SLOPD to adapt its security tactics to each location. This includes monitoring busy intersections, remote trailheads, or railroad crossings. This flexibility is crucial in a community that values its open spaces and balances accessibility with safety. "We've not only deterred potential criminal activities but also enhanced the overall safety for residents and visitors alike. The ability to monitor these areas remotely has been a game-changer, allowing us to extend our reach without stretching our resources too thin." Protecting evidence in cold storage with air quality sensors The introduction of Verkada's air quality sensors into the SLPD’s evidence management protocol has marked a significant improvement in securing critical evidence that requires refrigeration. “Sensors protect the evidence entrusted to us." "They monitor the conditions within our cold storage facilities in real-time, ensuring that any deviation from the norm is immediately flagged. This allows us to act swiftly to address any issues before they impact the evidence.” Sensors mitigate the risk of loss and help maintain the overall integrity of the evidence, which is crucial for the judicial process. Ensuring that evidence is stored under optimal conditions preserves its validity and reliability, which can be decisive in court cases. Guest and Workplace Solutions Verkada Guest supports security and compliance as well as administrative processes At the police department, Verkada Guest supports security and compliance as well as administrative processes and community interactions. "We're not just looking at improving how we manage security systems; we're also opening up opportunities to better serve our community in every interaction they have with us. This is about making our department more accessible, efficient, and responsive to the needs of San Luis Obispo.” Automated notification "Registrants can sign in digitally, similar to the check-in process at a doctor's office. This system automatically notifies the assigned detective, who can then prepare before meeting the registrant." "It's a welcome shift from our current, more manual process, and we're excited about the potential to make our operations more efficient while improving the experience for everyone involved.” Digitisation of visitor check-in The registration of certain types of visitors is a legal requirement that, until now, has placed a burden The registration of certain types of visitors is a legal requirement that, until now, has placed a burden on the department's space and resources. By digitising the initial check-in and form completion process, the department can handle sensitive registrations with greater discretion and efficiency. "We can integrate specific forms and requirements into the Guest system." Minimising congestion "This customisation ensures that we can maintain legal compliance while respecting the needs of our community and the constraints we operate under." "Guest reduces wait times, frees up essential space in the lobby, and minimises the congestion that can occur during peak registration periods.” Solar and Battery SLOPD is also exploring alternate power options to enable more deployments across San Luis Obispo, further ensuring the safety and security of their community. "Our partnership with Verkada has already improved our operations. The next step involves incorporating solar and battery backup systems for our cameras and bridge devices. This will not only expand our public safety reach but also ensure that our security measures are sustainable and resilient against power outages."
The Winston-Salem Police Department (WSPD), internationally accredited by the Commission on Accreditation for Law Enforcement Agencies (CALEA), is dedicated to proactive, data-driven approaches to law enforcement. Through initiatives like "Smart Policing," a collaboration with the local community and Winston-Salem State University, the department aims for systemic change in crime reduction and community safety. Real-time intelligence Lieutenant Ben Jones oversees the Real Time Crime Center (RTCC) housed in the Criminal Intelligence Bureau, a crucial nerve in the department’s operations. Under his stewardship, the team assists officers in protecting over 253,020 people across 133.7 square miles. “A more informed officer makes better decisions. We provide as much real-time intelligence as possible to detect, deter, and solve crime.” The challenge Get Connected Winston-Salem campaign integrates community-owned cameras into the police's video security Facing violent crime and an annual increase in homicides, the WSPD emphasises rapid responses underpinned by precise and accurate data. A particularly innovative step is the "Get Connected Winston-Salem" campaign, which integrates community-owned cameras into the police's video security system through Fūsus. This not only broadens the scope of crime monitoring but also exemplifies the department's commitment to collaborative crime-fighting. However, finding suspects’ vehicles was a logistical nightmare and still relied heavily on witness accounts. “We began looking at LPR solutions to assist in shootings, homicides, and cases involving vehicles.” Intelligence gathering with LPR and Multisensor To elevate its crime-solving capability, the city has strategically placed Verkada License Plate Recognition (LPR) and Multisensor cameras at traffic light intersections. “Our goal is to improve the solvability and speed of investigations by being able to identify suspects' vehicles across different intersections. We tie LPR with the Multisensor, which gives a four-way view across the intersection. No other solutions we evaluated offer this capability.” The nature of the incident When an incident is reported, the initial call is directed to the Patrol Divisions, and first responders are dispatched accordingly In partnership with the Winston-Salem Department of Technology (DoT), Jones plugs Multisensor cameras directly into the city system where there's Fiber and power. When an incident is reported, the initial call is directed to the Patrol Divisions, and first responders are dispatched accordingly. The nature of the incident determines its next course: for instance, serious shooting incidents are relayed to the Violent Firearms Investigative Team, while homicides are dealt with by the Criminal Investigation Division. Real-time Verkada Analytics “Before, we relied on witness information. Now, with Verkada and Fūsus, finding what we need can take just minutes instead of days.” The Verkada software, in conjunction with Fūsus, enhances the accuracy and speed of investigations, particularly in locating vehicles associated with a crime and finding missing people. People and Vehicle Analytics allow for the swift identification of both suspects and missing people throughout the city. Finding missing people - Detailing a success story, Lt. Jones recounts, “We found a missing person on a Verkada camera, and used People Analytics to find her at different times. We were able to confirm that she was alive at particular times, which gave investigators a starting point.” Coupled with ShotSpotter, a gunfire detection system, the team swiftly locates suspects using real-time analytics Finding suspects by vehicle - Coupled with ShotSpotter, a gunfire detection system, the team swiftly locates suspects using real-time analytics. “As soon as there is a shooting, the team uses Verkada to quickly locate suspects’ vehicles based on their description and colour." "A high percentage of violent crimes involve suspects who arrive, leave, or commit the crime from a vehicle. Verkada helps us identify where they’ve been, where they are, and where they’re headed.” Alerting with video context - Verkada goes a step beyond the image of a vehicle tag, providing a video of the car, its tag, and other vital details. “In the past, we might’ve stopped every red car. With Verkada, we have higher accuracy and less chance of mistaken identity." "I've been in the LPR market for a while and found that most solutions only give you a picture of the tag and vehicle. Verkada associates a video with each tag, so we have additional context easily available for intelligence gathering.” What's next Entering phase two, the goal is to place Multisensors closer together and increase the Verkada security These use cases with Verkada are just the beginning. Lt. Jones envisions a future where the department can seamlessly locate vehicles from one intersection to another, making suspect identification efficient and precise. Entering phase two, the goal is to place Multisensors closer together and increase the Verkada security coverage across the city. Real-time problem solving "The LPRs and Multisensor fit into our overlapping technology strategy, and we plan to increase the density of our deployment. If we’re pursuing an active shooter for example, having the cameras near our shotspotter areas allows us to use both technologies in conjunction with one another to locate the shooter.” Furthermore, by showcasing the efficacy of Verkada to other police departments, Winston-Salem aims to set a benchmark in crime-solving on the East Coast. Lt. Jones adds, “My goal is real-time problem solving; witnessing events as they unfold, not after. With Verkada, we’re turning that goal into reality.”
HID, the worldwide pioneer in trusted identity solutions, announces that Royal Jersey Laundry has introduced a new tracking feature of HID’s linen management platform at each of its 5-star hotel customer sites to guarantee that drivers drop off and collect precise linen stock and that costly errors are avoided. Linen tracking This new feature replaces a paper-based system used by drivers for the management of cages filled with clean/soiled linen delivered/collected at customer sites. It provides detailed end-to-end tracking of linen cages across multiple customer locations throughout the whole cycle of washing, packing, delivery, and collection, a complex process given that 550,000 pieces are laundered each week for numerous clients. Royal Jersey Laundry Royal Jersey Laundry works with most five-star hotels in London including The Dorchester, The Carlton Tower Jumerah Founded in 1915, Royal Jersey Laundry is one of the few cleaners servicing the luxury hotel sector. Based in a 25,000 square-foot purpose-built facility in Dagenham, rebuilt in 2021 for £15 million after a fire, it works with most five-star hotels in London including The Dorchester, The Carlton Tower Jumerah, The Peninsula London, and The Ritz. Need for constant communication Supporting the five-star segment is demanding given the constant communication required between the hotel and laundry, exacting standards, and the quantity and range of items to be laundered. This includes duvets, sheets, towels, and bath robes along with smaller items such as foot mats, drink coasters, shaving towels, and dry cleaning for guests themselves. Royal Jersey Laundry operates 24/7, employs 150 staff members, and washes 40 tons of linen per day. Maintaining laundering schedule Five-star hotels prefer to use linen they own with five sets kept of everything, allowing them to maintain a schedule In contrast with budget and mid-level hotels, five-star hotels prefer to use linen they own with five sets kept of everything, allowing them to maintain a rigorous laundering schedule and ensure guests always receive fresh, cleaned linens. “An average 300-bed hotel will have around 30,000 items of linen which will cost around £250,000,” says James Lincoln, Royal Jersey Laundry’s managing director. “The volume of linen is so high and it’s always moving such that accurate inventory control was a major challenge verging on the impossible.” HID cloud-based RFID linen management system Before the HID cloud-based RFID linen management system, everything was done manually. Laundry staff would check items off ironing/folding machines, a wholly error-prone process, and log the quantities on pieces of paper. The operational overhead for the laundry was exacerbated as the various linen items from the different hotels had to be kept separate, too. “Linen is everywhere: on beds, in cupboards, in transit, and at the laundry, yet no one had full insight into stock levels and, when things went missing which often happened, typically we’d get blamed,” says Lincoln. Real-time linen inventory management LinTRAK tags are sewn into linen items by laundry staff or linen manufacturers during the production process To address these problems, Royal Jersey Laundry installed a real-time linen inventory management system from HID combining LinTRAK® RFID tags, a full set of RFID equipment including table-top and conveyor-belt scanners, one RFID portal and one cabin scanning unit, and cloud-based Acuity software. The discrete LinTRAK tags are sewn into linen items by laundry staff or linen manufacturers during the production process. Some hotels also use LinTRAK tags to manage staff uniforms and restaurant linens such as napkins and tablecloths. HID LinTRAK textile tags Around 40% of Royal Jersey Laundry hotel customers have transitioned to the HID linen management solution and connect via Acuity’s web portal. Once cleaned, the linen is packed into cages, and scanned in seconds through HID’s RFID cabin station. Items are automatically counted, with delivery notes generated including billing information. HID’s Acuity software integrates with the laundry’s Sage accounting software to generate invoices. Benefits of textile tags The implementation of HID LinTRAK textile tags, RFID stations, and the Acuity software platform has radically changed how Royal Jersey Laundry operates, delivering a range of benefits: Fast Return on Investment: Since the installation of the HID equipment in 2019, the system has already paid for itself given the efficiency and productivity gains. Better use of people resources: Laundry and housekeeping staff no longer waste time on dull and resource-intensive activities like manually counting linen. They have been redeployed to more productive work, generating 10-20% savings in labor costs. Better visibility of stock levels: As hotels know exactly the location and quantity of linen, they are better able to cater to peak demand, reducing linen expenditures by up to 30%. Improved responsiveness and customer satisfaction: Access to in-depth data generated by the Acuity platform means the laundry can quickly answer customer queries. “We give hotels complete transparency about where their linen is in the cleaning and delivery cycle. There are just no grey areas anymore,” says Lincoln. Increased security of expensive linen assets: While theft of linen at five-star hotels is rare, it does happen. RFID tagging enables better monitoring of expensive bedding and towel investments. Enhanced reliability and productivity: Operations are more efficient as RFID-enabled items can never be lost or misplaced. Furthermore, digital scanning results in faster processing of items. “We’re effectively two businesses: the laundry itself and a logistics operation. We run a mixed fleet of lorries and electric vans which nip in and out of London three times a day picking up and delivering garments for hotel customers using us for guest work,” adds Lincoln.
Installers JTI Brandbeveiliging was contracted to help make safety a number-one priority at a pioneering food manufacturer in The Netherlands. They achieved this by choosing Hochiki Europe’s marketing pioneering fire detection system, Latitude, alongside waterproof devices from the ESP range. This comprehensive solution ensures the highest level of fire protection throughout the facility, giving the food manufacturer peace of mind and allowing them to focus on what they do best: producing delicious food. Kervo Kervo is a specialist in the high-quality cultivation and processing of fruit in the Netherlands. Since 1980 morello cherries have been grown in the Vossen family’s orchards in Roggel, The Netherlands. The family was one of the first growers in the region to use mechanical harvesting in the ’80s, fast forward 43 years later and Kervo currently runs operations across Europe and the UK and is proud of its reputation for offering the finest quality fruit to bakeries and fresh food processors. Fire protection systems Complexities of this project was that during food production significant amounts of steam were generated JTI Brandbeveiliging was founded in 2009 and is trusted by its customers for advice, installations, repairs, and maintenance of fire protection systems across the region. The team, led by Luciën van Eldijk was commissioned in 2022 to design and fit the fire safety system that would be integrated into Kervo's new manufacturing plant in Neer. One of the complexities of this project was that during food production, and particularly during the cleaning processes, significant amounts of steam are generated, thus causing false alarms. Latitude fire safety system Lucien explains how he and the team navigated this issue, “In food production sites like this, the machinery needs to remain clean throughout the entire process. This means there is a lot of steam and water present, which, unfortunately, can trigger false alarms." "We needed to install devices that could negate this issue, Hochiki’s waterproof call points, sounders, and sensors were the perfect solution. They worked seamlessly with the Latitude fire safety system from Hochiki.” Fire detection devices and systems Latitude, which is BOSEC-approved, a requirement for fire detection devices and systems in The Netherlands, has a powerful network-wide cause-and-effect capability. The system can support 5000 entries, with up to 20,000 inputs and 20,000 outputs across the network. Benefits of Latitude The new building at Kervo is a huge facility making the Latitude system the best solution The new building at Kervo is a huge facility, at over 40 metres in height it required over 2.5km of cabling and hundreds of fire detection devices to help make the building secure, making the Latitude system the best solution. “Due to the nature of this project, there have been some technical aspects where we have needed to seek advice, but the team at Hochiki has been very helpful in working with us to create the best solution for our customer." Easy to install with high standards "We choose Hochiki products and systems because they are reliable, they are easy to install and, most importantly, meet the high standards and regulations required by the laws of The Netherlands, we would recommend Hochiki products for this reason.” Hochiki’s analogue addressable range (ESP intelligent) together with the Latitude system are EN54 Part 13 certified and with the BOSEC certification also in place, they provide the best complete and compliant fire detection system for businesses across the Belgium region as well as bordering countries such as Luxemburg, the Netherlands, and Germany.
RecFaces, a facial recognition software company, has announced the successful deployment of its flagship product, Id-Guard at Jorge Chávez International Airport in Lima, Peru. This implementation marks a significant milestone in bolstering security measures at one of South America's busiest airports, underscoring the importance of maintaining a high level of safety at public transportation hubs. Jorge Chávez International Airport Jorge Chávez International Airport serves as a vital gateway for travellers and cargo, welcoming more than 20 million international and national passengers every year. With such a high flow of people, ensuring the safety and security of passengers and airport personnel becomes crucial. Recognising this need, RecFaces collaborated with airport authorities to implement their state-of-the-art Id-Guard solution and help ensure the safety of the facility. Enhanced security measures The solution's features enable airport authorities to prevent suspicious individuals from accessing the site The implementation of Id-Guard has significantly enhanced security measures, allowing for proactive monitoring and rapid response to potential security threats. The solution's features enable airport authorities to prevent suspicious individuals from accessing the site, thereby safeguarding the safety of passengers and staff. Highest level of security “Airport representatives felt the need for facial recognition to strengthen the security structure within the airport as a whole,” notes Maria Kazhuro, Business Development Director for the LATAM region, RecFaces. Maria Kazhuro adds, “Our goal was not only to provide the highest level of security but also to simplify work processes for security guards. We can confidently say that the installation of an ID guard has significantly improved security in the facility. Now both airport visitors and employees can be sure that they are under even greater protection than before.” Id-Guard facial recognition The deployment of Id-Guard at the Peruvian airport demonstrates RecFaces' dedication to excellence and innovation in the field of facial recognition technology. As airports worldwide continue to prioritise security and passenger experience, RecFaces remains at the forefront of delivering advanced biometric solutions tailored to the evolving needs of the aviation industry.
ZeroEyes, the creators of the only AI-based gun detection video analytics platform that holds the US Department of Homeland Security SAFETY Act Designation announced that Park City School District (PCSD) of Summit County, Utah has deployed its proactive gun detection and intelligent situational awareness solution to mitigate gun-related violence. Park City School District (PCSD) Nestled within the mountains of the year-round resort town, PCSD encompasses four elementary schools, a middle school, a junior high, a high school, and a learning centre. The district educates nearly 5,000 students annually and boasts a graduation rate in the top 1 percent of the nation. Intelligent situational awareness software AI gun detection and intelligent situational awareness software is layered on existing digital security cameras PCSD is highly focused on student safety, collaborating with the Summit County Sheriff's Department and the Park City Police Department to deploy advanced electronic, physical, and procedural security measures. ZeroEyes' AI gun detection and intelligent situational awareness software is layered on existing digital security cameras at all eight student-occupied PCSD buildings. ZeroEyes Operations Centre If a gun is identified, images will instantly be shared with the ZeroEyes Operations Centre (ZOC), staffed 24/7/365 by specially trained U.S. military and law enforcement veterans. If these experts determine that the threat is valid, they will dispatch alerts and actionable intelligence, including visual description, gun type, and last known location, to local staff and first responders in as fast as 3 to 5 seconds from detection. AI algorithms The platform does not store personal or biometric data or conduct any kind of facial recognition The company's AI algorithms only search for guns, not faces or bodies. Until a gun is identified, the monitoring screens in the ZOC stay blank; the ZeroEyes Operations team does not see a live feed from any cameras. Further, the platform does not store personal or biometric data or conduct any kind of facial recognition. Gun-related violence “We hold a deep commitment to safeguarding our students and staff, and ZeroEyes is a compassionate ally in our mission,” said Michael Tanner, COO of Park City School District. He adds, “By addressing the concerns of gun-related violence while also respecting the need for privacy, this solution allows us to provide a secure yet welcoming campus environment.” Proactive safety measures “Between its collaboration with local law enforcement and the deployment of proactive safety measures throughout its schools, Park City School District has shown that it is on the cutting edge of security,” said Mike Lahiff, CEO, and Co-Founder of ZeroEyes, adding “We are proud to work alongside this dedicated leadership team to protect students and staff against gun-related threats.” Park City School District was introduced to ZeroEyes through the company’s exclusive Utah reselling partner Aegix, a provider of industry-pioneering resources, technology, equipment, and training for first responders.


Products


Round table discussion
The security industry offers a vast array of technologies and vendors. This can be overwhelming for end users, who depend on security integrators for guidance and service. But how well do security integrators provide end users with what they need? We asked this week’s Expert Panel Roundtable: What are the biggest challenges that end users face when working with integrators?
Technology offers a range of tools to bolster security at public events, including before, during, and after. This year, the 2024 Summer Olympics in Paris will draw the attention of the world, requiring the best protection available for the venues, the athletes, and the attendees. Other happenings such as the FIFA World Cup, the Super Bowl, the Tour de France, and the U.S. NBA Finals are momentous events that challenge security and law enforcement personnel to keep them safe. We asked this week’s Expert Panel Roundtable: How is technology contributing to security in the arena of public events?
There is a bright outlook for trade shows in 2024. In particular, ISC West has recently become the must-see event in the security marketplace. ISC West will take place April 9-12 at the Venetian Expo in Las Vegas. In addition to providing access to a wide range of technological innovations, the show also serves as a platform to introduce new products and services. As the industry counts down to the big exhibition, we asked this week’s Expert Panel Roundtable: What will be the big news at ISC West 2024?
White papers

Guide for HAAS: New choice of SMB security system
Download
Precision and intelligence: LiDAR's role in modern security ecosystems
Download
Integrating IT & physical security teams
Download
Top 7 trends to watch in the physical security industry
Download
How video technology is transforming loss prevention, operations, and customer experience in the retail sector
Download
2024 trends in video surveillance
Download
How intelligent video is transforming banking and financial institutions
Download
Securing data centres: Varied technologies and exacting demands
Download
Best practices for asset management
Download
Understanding the IT needs of video surveillance
Download
AI in security solution
Download
Access control: The enterprise buyer's guide
Download
Machine Operator Authentication
Download
Levelling up with campus safety
Download
The benefits of Edge AI + Cloud for security systems
Download


Multi-residential access management and security
Download
Guide for HAAS: New choice of SMB security system
Download
Precision and intelligence: LiDAR's role in modern security ecosystems
Download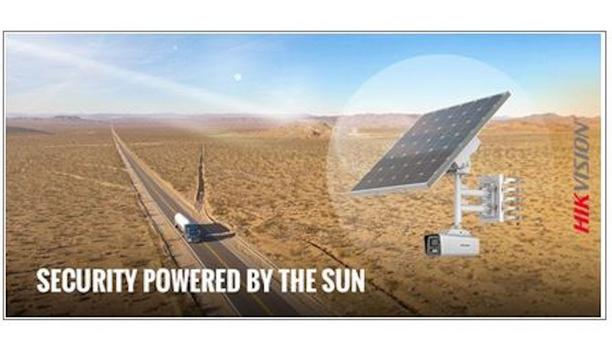
Hikvision: Solar powered product introduction + HCP
Download
Gunshot detection
Download


















































