We can add another technology category to those aspects of the physical security market on the verge of being changed by cloud technology. The new category is the printing and encoding of ID cards.
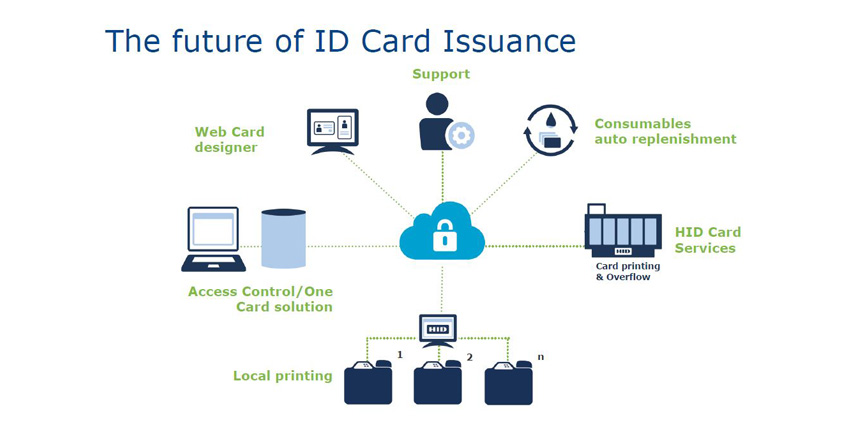
HID Global is adapting the benefits of cloud computing to the ID card printing market with the introduction of HID Fargo Connect, a cloud-based personalisation and issuance system for ID cards. The new cloud approach, which will be introduced at the ASIS 2017 show in Dallas, converts standalone card printers and encoders into edge devices in the Internet of Things (IoT). In effect, ID cards can now be printed from any device anywhere on any other device anywhere else.
Evolving ID card market
Historically, ID cards were printed by local standalone printers connected to on-premises personal computers (PCs). Using the cloud approach, a card can be printed from a tablet or similar device and directed to a cloud-connected card printer.
The cloud approach is a new twist in a mature market that has been largely unchanged for the past two decades. HID Global, which acquired the Fargo printer business in 2006, is seeing customer needs evolving to include both printing and encoding ID cards. In the future, customer needs will broaden to encompass every aspect of managing identity issuance, according to Craig Sandness, Vice President and Managing Director of the Security Issuance business unit at HID Global.
“This is not a one-off product but a new platform, and new solutions will continue to be introduced and evolve in the market,” says Sandness. “We are initially focusing on the higher-education market, but there are lots of opportunity in several major verticals, such as corporate environments with multiple locations. The solution can be centrally managed for all the locations.” Other HID Global vertical markets include government and public administration, healthcare, financial, transportation, and enterprise.
Benefits for end users
Benefits for end users include greater flexibility in how card printing systems are designed and operate, says Sandness. More flexibility enables end users to streamline processes and promote a better “customer experience” when issuing ID cards and credentials.
 |
| The new cloud approach converts standalone card printers and encoders into edge devices in the Internet of Things |
For example, students no longer have to wait in long queues at multiple PC workstations to be issued cards in a higher education environment. Instead, card issuance can be managed in a more casual, relaxed environment, with operators using tablet computers to input data and capture images for the cards, which can then be printed in bulk at a large production facility connected to the cloud. Kent State University, Kent, Ohio, is an early user of HID Fargo Connect.
The cloud approach also takes away the need to manage software and other IT resources. End users get better visibility and more control of the card issuance processes, according to HID Global.
New economic models for security integrators
For integrators, the approach introduces new economic models for their business. It allows their customers to transform the issuance of ID cards from a capital expenditure (capex) to an operating expense (opex). Security dealers no longer need to be just in the business of selling card printers; they could also be in the business of providing cards as a service, payable as a monthly operating expense based on how many cards are needed, for example.
Providing a service rather than a product can position dealers for a longer-term relationship with a customer, in effect promoting “stickiness” (customer retention). The service aspect also provides dealer/integrators new opportunities to realise recurring monthly revenue (RMR).
Benefits for dealers
Dealers can also benefit from automated replenishment systems. A cloud-connected printer can signal a dealer automatically when it needs a new ribbon, for example, thus boosting a dealer’s ongoing business in consumables.
“There could be an annual or monthly contract that allows the integrators to provide much better and more timely service and faster consumables,” says Sandness.
As with any IoT approach, cybersecurity is paramount, and HID Global emphasises the cloud card issuance system is secure. The system uses HID’s Identrust Certificates and end-to-end encryption, and all personal data is transcient, not stored, and communicated between highly secure end points. “The print systems have unique firmware and will only work with Fargo Connect,” says Robin Tandon, Director of Product Marketing, Cloud Solutions, Secure Issuance Business Unit of HID Global.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance














