Edward Troha, Director of Marketing for ObjectVideo, questions the actual intelligence of some video analytics packages.
While roaming the halls of the seemingly endless stream of security and surveillance trade shows, have you ever asked yourself if all of the devices and software and solutions that claim to be "intelligent" really are? No way. Perhaps the more important question is "what can you do today to most effectively educate yourself on the fact and fiction of video analytics?"
Let's begin with a definition. There are three important criteria that will enable you to determine if a system, device or solution is truly intelligent:
First, it must be an application of artificial intelligence; specifically, computer vision. This is important because computer vision, the science of teaching a computer to see, is the basis for all truly intelligent vision-based systems.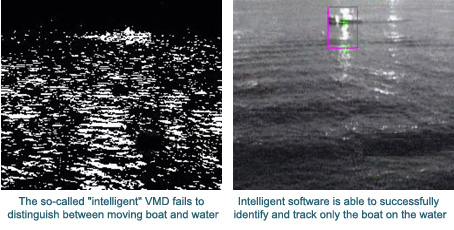
Second, the software must be capable of accurately separating foreground from background objects, and create a stream of metadata that reflects a 24/7 analysis of the view. This is important because a truly intelligent system is one that can interpret and report on actual events, rather than just react to movement.
Third, the system must be able to provide the user with relevant real-time information about these events. This is important because the human user must be able to easily and intelligently interact with the system in order to make the critical decisions that can mean the difference between proactively catching the bad guy or not.
So, which technologies are being touted today as intelligent? Here are two of them – one old, one new.
The newer one is the biometric technology facial recognition, which has a close relative in automated number plate recognition (ANPR). Although both of these are vision-based, and do analyse what they are seeing, they are probability-based. That is, they rely on the relative quality of the view to do their jobs and then can only compare 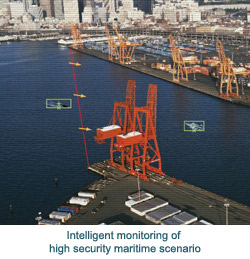 what they have with what they've already got in the database.
what they have with what they've already got in the database.
So unless you think a relational database application is "intelligent", facial recognition and ANPR are not intelligent in the way computer vision-based video analytics are. And at the same time these technologies are being touted as intelligent, they are rarely thin, meaning users can expect to make a relatively heavy investment in back-end servers and enterprise software to be able to run them.
The other technology that even more frequently is pitched as intelligent is video motion detection, or VMD. New flavours and permutations of this dinosaur seem to come out all the time, but don't be fooled by VMD – it's definitely not intelligent.
Why not? VMD does not analyse; it reacts to motion. It does not interpret events; it reacts to motion. It does not classify objects; it reacts to motion. So VMD is aptly named – in its basic form, any movement of 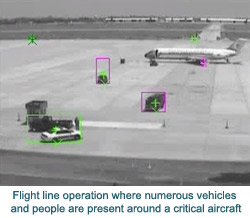 any pixel at any time will cause an alarm. How many times must the wind blow tree branches within the view, or a couple of birds fly though the scene for you to turn it off for all the false alarms?
any pixel at any time will cause an alarm. How many times must the wind blow tree branches within the view, or a couple of birds fly though the scene for you to turn it off for all the false alarms?
Users need to beware of "intelligent edge devices" that consist of VMD-enabled cameras and filtering software on the back-end. The filters must be configured for object size and a variety of other parameters in order to reduce false alarms to a tolerable level. And, despite the filtering software, the VMD on the camera is still merely reacting to movement. In fact, calling VMD solutions "intelligent" is a contradiction in terms that only adds to the confusion that reigns in this market.
Software companies, device manufacturers, end-to-end solution providers – they're all claiming intelligence for one reason: money.
Slapping VMD into a device that previously didn't have it, then calling it 'intelligent' and adding as much as a 30% price premium won't get the end-user the truly intelligent capabilities they require. These companies are late to the game and are frantically trying to catch up. They attempt to do so by creating noise and confusion in the market, rather than by creating products that have real video analytics embedded on them.
The smart manufacturers, like Verint, Tyco Fire & Security and March Networks, are the ones teaming up with the technology providers who have been doing it for quite awhile, like ObjectVideo, because these manufacturers know that they'll never be able to support the huge amounts of R&D time and money that it takes to bring a commercially viable video analytic capability to market. Really big names like GE, Siemens, Honeywell and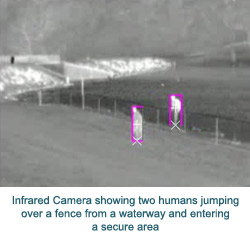 IBM have either acquired smaller analytics companies and consequently their intellectual property or just given up.
IBM have either acquired smaller analytics companies and consequently their intellectual property or just given up.
Advice: Ask pointed questions of providers who claim intelligent products according to the three criteria above. And insist that the analytics you acquire within the solution have comprehensive functionality (not just a few analytic capabilities), are very easy to integrate into any existing infrastructure and are consistent with a video analytics strategy that supports the fulfilment of your security mission.
 Edward Troha
Edward Troha
Director of Marketing
ObjectVideo
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems





















