Radio frequency Identification - Expert commentary
The outlook for advancements in door security solutions is proving to be an extension of the positive trends that have emerged over the past few years and that continue to evolve in exciting new ways. That’s a good sign as we make our way along the road toward an ever-safer world. Improvements in a hybrid workforce Here’s what we’re seeing: More and more companies are rethinking the office space and how electronic access control (EAC) security and data can help better s...
There’s a new security paradigm emerging across malls, server farms, smart office buildings, and warehouses, and its advantage over the status quo are so broad they are impossible to ignore. Instead of a lecture, let’s start with a short narrative scenario to illustrate my point. Darryl's work Darryl works as a security guard at the Eastwood Mall. Like any typical evening, tonight’s shift begins at 9:30 PM, as the stores close and the crowds thin. His first task: Ensure that...
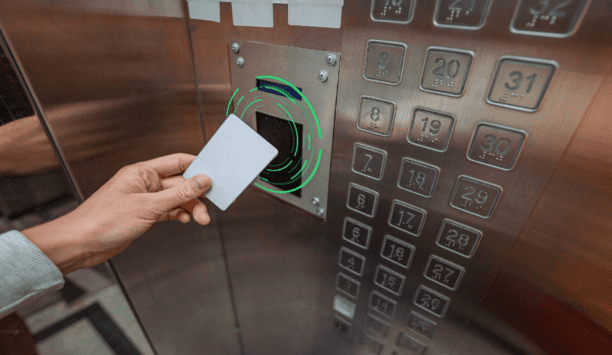
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
You’re no psychic. You probably don’t have the power of clairvoyance. But guess what? When it comes to your security, none of that matters. You can still create future-proof security by properly equipping yourself. Here’s how. Understanding access control Security is changing faster than ever before. With new threats inside the workplace and smaller security teams taking on more tasks, IT and security personnel must automate their processes using new technology. One difficu...
Although inflated fuel prices have somewhat settled since the summer, recent changes in legislation mean construction sites are particularly vulnerable to attempted fuel thefts. Read on to find out what’s changed, and what’s proving effective in mitigating the threat. What are the changes? As of April, this year red diesel can no longer be used in a range of vehicles, including those in construction. That means fuel bowsers are now filled with the same white diesel available to m...
The growing mobile ownership rate, the emergence of more user-friendly banking apps, the tech-native younger generation, and, of late, the pandemic-induced shift to online, all create a fertile ground for mobile banking. Unfortunately, the acceleration of banking app adoption today goes hand in hand with the increase of targeted security threats. In 2022, a month wouldn’t go by without a headline-making mobile banking attack or incident that resulted in stolen funds and sensitive personal...
It’s clear that despite recent layoffs in the tech industry and general unease about the economy, there are still significant gaps in the number of jobs available and the amount of workers available to fill them. According to the Labour Department, there are 5.5 million more job openings than workers available. The physical security industry is not immune to these shortages. Last fall, Allied Universal reported being unable to fill thousands of open roles nationally while other smaller s...
The smartphone is an integral part of our daily routines. The communication and entertainment device of yesteryear has become a serious player with which we increasingly handle sensitive processes, such as payment transactions. BLE or NFC authentication At the supermarket checkout, more and more customers are pulling out their smartphones instead of their wallets. Apple Pay, Google Pay, or specific banking apps make it possible: to hold the smartphone in front of the reader of the checkout sys...
Although video camera technology has been around since the early 1900s, it was not until the 1980s that video started to gain traction for security and surveillance applications. The pictures generated by these initial black and white tube cameras were grainy at best, with early colour cameras providing a wonderful new source of visual data for better identification accuracy. But by today’s standards, these cameras produced images that were about as advanced as crayons and coloring books....
For the past few years, security professionals have had to change the way that they go about protecting their organisations. From challenging old assumptions around access control through to implementing more access management and authentication policies, security has been at the heart of how companies have responded to the pandemic. The journey to more modern security processes that could support more flexible working was a rapid one. Remote work programmes have bedded in, based on how IT sec...
Nowadays to save costs by making full use of old devices while upgrading the old security projects, many integrators or installers prefer to use video management software to manage multiple brands of video devices (such as IP cameras, and NVR), instead of only one single brand. So that they could have more flexible choices to earn profits while saving costs. Multi-brands video device management On other hand, with market segmentation and specialisation, instead of managing the video by themsel...
Cloud-based video surveillance as a service (VSaaS) is in a period of significant growth at present. In fact, the global VSaaS industry was valued at $2.2 billion in 2020 and is expected to reach $4.7 billion by 2025. Part of the reason for this growth is the increased adoption of the technology within shops, restaurants, and other retail settings. A cloud-based video management system can be valuable for businesses of all kinds, but those in the retail or restaurant industries are often able t...
The banking market continues to evolve through the growing use of digital and mobile devices, as more branch operations aim to enhance convenience and service for the customer. These advancements also create more significant opportunities for fraud and loss. Together, these two trends come full circle: Increasingly sophisticated fraud techniques require organisations to pursue new approaches to preventing and detecting such activities. Digital transformation But before we lead down that path,...
One of the biggest security trends in the last two years has been the adoption of cloud-based services, spearheaded mainly by an increasing number of video surveillance-as-a-service (VSaaS) offerings. VSaaS market value According to MarketsandMarkets Research, the global VSaaS market value is expected to reach $6.2 billion by 2026. This growth is propelled by demand for remote access video services, less local hardware to maintain, new internet-enabled devices, and a lower total cost of owners...
Enterprise security directors often count on an integration firm to handle jobs ranging from day-to-day activities to long-term, technology-laden projects. However, before entering a relationship, you must know what's reasonable to expect from an integrator – as not all are created equal. Here are some tips that might make the selection process easier. Completing comprehensive classwork An integrator's experience working in an enterprise environment is an obvious consideration. Ideally...
One key aspect of hardware design is choosing an appropriate form factor for your product. In today's world, form factor not only defines your product's size and shape but also includes its aesthetic appeal. While size and shape are important, another aspect that is prominent when dealing with RFID card readers (including NFC and BLE mobile credential readers) is the reader's location within the end device and the size of the RF antenna. This article focuses on some key considerations relating...
Today, RFID readers can be found in numerous devices requiring user authentication, authorisation and access control, from doors to multi-function printers to point of sale terminals to computers and more. RFID is a simple, secure and convenient access control solution for end users and original equipment manufacturers. RFID readers/writers come with a broad range of form factors, capabilities and configurations. Choosing the right RFID reader When choosing a reader to embed into a system or d...
With increasing security and public health concerns, contactless credentials are gaining more and more importance. Contactless credentials can be divided into two main categories: soft credentials that include mobile phone applications that tap into their BLE/NFC hardware and transmit the data, and hard credentials that typically include low frequency (125 kHz) and high frequency (13.56MHz) based passive RFID transponders. With the help of these credentials, organisations can tackle safety conc...
More and more business security practices are going digital. Mechanical keys are still the backbone of most corporate security plans, and it can be very expensive for companies to switch to electronic access control on a large scale. Therefore, enterprises need to choose the most suitable access control system. What is key management? Key management is the process of protecting, tracking, and scheduling mechanical keys. Why is this important? Because the key carries access to sensitive locatio...
The concept of security has substantially upgraded because of technological advancements. We have seen a shift from mechanical locks to electronic locks and door access control systems which are more relied upon nowadays for watertight security and safety. But, choosing the system that is the best for you requires understanding how both these technologies work. In this article, you will get a clear idea of: How electronic locks are better than traditional locks The difference between access...
The emergence of smartphones using iOS and Android is rapidly changing the landscape of the IT industry around the world. Several industries, such as digital cameras, car navigation, MP3, and PNP, have been replaced by equivalent or even better performance using smartphones. Smartphones provide increasing portability by integrating the functions of various devices into a single unit which allows them to connect to platforms with network-based services and offer new services and conveniences that...
Public spaces in cities and suburbs are important places for community development and promoting outdoor recreation. These areas may include main streets, parks, promenades, band shells and fields. Such locations are often utilised by public event planners for community activities, including summer festivals, wintertime ice skating rink installations, music concerts and art fairs. As the year drew to a close, holiday and Christmas markets as well as major New Year’s Eve events, presented...
It amazes me how in a few short years security systems have gone from simple, dumb cameras witnessing events to intelligent eyes, ears, speech and touch solutions that boost situational awareness far beyond human capabilities. It seems the only senses missing from the equation now are smell and taste. And who knows, someone might be working on those in a lab somewhere right now. But what’s really fascinating to me is how the Internet of Things (IoT) has opened a world of possibilities for...
From satellite imagery to street views to indoor mapping, technology has disrupted our past world. This has left us dependent upon new ways to visualise large spaces. This new world has brought many benefits and risks. But what does that mean for the security professional or facility manager today and what technologies can be used to secure buildings and improve facility operations? A brief history of 3D technology Starting May 5, 2007 (inception 2001), Google rolled out Google Street View to...
In 1901 New York state made a pioneering regulation move and became the first US state to require automobile owners to register their vehicles. This marked the beginning of regulation on modern traffic, which - following decades of development - resulted in a multi-layer concept of regulation relating to vehicles and driver’s licenses, traffic signs and insurance mechanisms that we are all familiar with nowadays. While certain parallels can be drawn between the early days of cars and our...
Over the past few years, biometrics has rapidly expanded into consumer applications, like the financial market for customer authentication, to payment services and withdrawing cash from ATMs in high-fraud markets. However, its adoption as an additional authentication factor for physical access control systems (PACS) and other enterprise applications, hasn’t been as rapid. But this is changing. Biometrics offers numerous benefits at the door and throughout the enterprise. With the advent o...
The Food Standards Agency (FSA) in the UK has begun investigations into meat wholesalers after a raise in concern for food hygiene. This investigation has impacted businesses such as Wetherspoons, as well as schools and care homes up and down the country. Consumers are beginning to lose trust in businesses that are supplied by untrustworthy production companies and it seems to be becoming more common, if we are to look back to the horse meat scandal in 2013. But what are the benefits of havin...
The most important trend that developed in 2017 was the increasing focus on cybersecurity. As more and more devices move to the Internet of Things (IoT) model to provide added convenience and intelligence, the ability of hackers to use those devices to infiltrate systems – and the need for oversight to protect organisations – has also increased. Another trend we saw was an increase in the number of compliance and audit requirements related to physical security. An example of this i...
The use of drones has increased dramatically in the last few years. Indeed, by 2021, the FAA says the number of small hobbyist drones in the U.S. will triple to about 3.55 million. With that growth, drone capabilities have increased while costs have decreased. For example, the DJI Phantom 4 can deliver a 2-pound payload to a target with 1.5m accuracy from 20 miles away for the less than $1000.00. This is an unprecedented capability accessible to anyone. This new technology has created an entirel...
Since the introduction of smartphones with downloadable applications, vendors have been trying to replace the traditional plastic identification (ID) card with a mobile phone application. People might lose or misplace an ID card, but most people immediately recognise if they are without their mobile phone. Mobile ID badges for access control Bluetooth Low Energy iBeacon technology Technical challenges of mobile ID apps The logical extension is to replace or augment the traditional corpor...
One system, one card
DownloadAligning physical and cyber defence for total protection
DownloadUnderstanding AI-powered video analytics
DownloadEnhancing physical access control using a self-service model
DownloadHow to implement a physical security strategy with privacy in mind
Download