Physical Security Information Management (PSIM) - Expert commentary
It is the time of year when city centres transform, as outdoor Christmas markets fill town squares and high streets. An estimated 6,000 markets will open across Europe during the festive season, with some of the largest — including Nuremberg’s Christkindlesmarkt, London’s Hyde Park Winter Wonderland and Craiova in Romania — welcoming millions of visitors. Sadly, these popular events have in recent years been the subject of attacks, most notably Berlin in 2016 and the tra...
The Internet of Things is growing quickly. It has moved far beyond a few smart gadgets at home. Today, connected technology is in homes, factories, hospitals, farms, and cities. Experts expect the global market for IoT devices to rise from about $70 billion in 2024 to more than $181 billion by 2030. This means more devices, more data, and more opportunities for industries everywhere. This growth comes from several advances working together. 5G connections make it possible to send and receive d...
Where and how to store security camera footage usually depends on the scale of the video surveillance project, the way you are using to record the video and how long you want to keep the recordings. If there are only few IP cameras, say 2~3 IP cameras for example, and you don’t need to keep the recordings for the month, usually using SD card which is installed in the camera is enough. Video management software A VMS provides a unified platform to manage all cameras and record footage on...
A key characteristic of many successful companies is that good ideas come from everyone, not just specific departments or job titles. What one person sees as obvious may be questioned by someone else who is less familiar with the product or process. This simple interaction can spark a whole new, faster, and better approach. While valuing tradition is important, if someone uses the phrase “that’s how we’ve always done it,” it’s essential to analyse the process...
The importance of data is ever-growing. For every profession, we’re witnessing the increasing reliance on data and its ability to promote efficiency for corporate decision-makers. The security industry is no different. The growing reliance on data and technological tools has allowed for a new breed of professionals with specialised skill sets. This evolution reflects the changing nature of security challenges in the digital age. The new security environment We know one thing from near...
Where access control is concerned, architects and design teams must find the right balance between aesthetics, functionality and security, says Daniel May of Consort Architectural Hardware. Following a period of innovation and integration, access control has developed into an ever-prominent facet of building design over the past decade. Where systems were once rudimentary, modern user requirements have led to several operational and technological advancements, resulting in a versatile selection...
Dr. Henrik Siegle has been the CTO at Bosch Building Technologies since November 2021. In this interview, he speaks about the megatrends of energy efficiency and sustainability, and about new developments in the building technology sector. Dr. Siegle, the building industry is currently facing major challenges in the form of climate change and energy shortages. How is Bosch Building Technologies dealing with these challenges? Dr. Henrik Siegle: Energy efficiency and sustainability have long...
Video surveillance has become the king of data—and is known to be the largest producer of data in the world. A single day of video surveillance is estimated to produce more than 500 petabytes of data—for context, a single petabyte is equivalent to 1,000 terabytes – and that number is only expected to grow. Why is it expected to grow? The answer lies with new and emerging technology, and the way that technology operates. For physical security teams, the rapid amount of data the...
Managing the technology stack and known vulnerabilities is becoming a key criteria for cyber insurance pay outs. Open source software has once again made the headlines following warnings to organisations about the release of a new version of OpenSSL. Released on 1st November 2022, the new version patched vulnerabilities in version 3.0 and above of the nearly ubiquitously used cryptographic library for encrypting communications on the Internet. Remote code execution The OpenSSL Project team to...
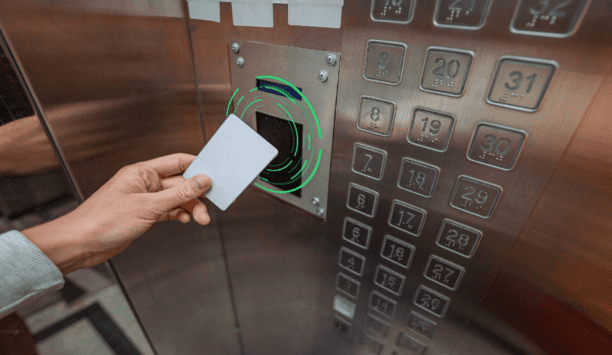
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from building entry to printer access. The right RFID reader can help reduce complexity by migrating diverse older technologies into a single convenient solution. Ways RFID Works Radio-frequency identification (RFID) and smartphone-based credentialling systems using Bluetooth® Low Energy (BLE) or Near-Field Communication...
You’re no psychic. You probably don’t have the power of clairvoyance. But guess what? When it comes to your security, none of that matters. You can still create future-proof security by properly equipping yourself. Here’s how. Understanding access control Security is changing faster than ever before. With new threats inside the workplace and smaller security teams taking on more tasks, IT and security personnel must automate their processes using new technology. One difficu...
At the start of the millennium, GRC was still very much in its infancy. Fast forward to 2022 and it is no longer seen as a siloed process. Now it is an organisation-wide concern that permeates every decision from C-suite to the shop floor. And its evolution shows no sign of slowing down as modern solutions are changing the way that GRC processes are delivered and embedded into day-to-day operations within organisations. So, what does the future look like? In an era where risk is accelerating, w...
If defence is the best form of attack, then in security, planned preventative maintenance (PPM) is the best way to protect your business from harm. Also known as PPM, the service ensures that your security efforts are up-to-date and effective. In the latest how-to guide, discover the benefits of planned preventative maintenance and learn how to add PPM to your building. What is Planned Preventative Maintenance? You have installed all of the necessary security measures for your business, now wh...
It’s clear that despite recent layoffs in the tech industry and general unease about the economy, there are still significant gaps in the number of jobs available and the amount of workers available to fill them. According to the Labour Department, there are 5.5 million more job openings than workers available. The physical security industry is not immune to these shortages. Last fall, Allied Universal reported being unable to fill thousands of open roles nationally while other smaller s...
Identity management is an important element of both data security and physical security in an organisation. But all ID management solutions are not the same—especially when it comes to security. There are no uniform security standards for the industry, and many off-the-shelf systems fall short when it comes to data protection. To protect people, property, and data, make sure you select a system that maximises security at every stage. What is identity management? Identity management&mdas...
For the past few years, security professionals have had to change the way that they go about protecting their organisations. From challenging old assumptions around access control through to implementing more access management and authentication policies, security has been at the heart of how companies have responded to the pandemic. The journey to more modern security processes that could support more flexible working was a rapid one. Remote work programmes have bedded in, based on how IT sec...
In the UK there is a new data reform act working its way through the legislative process. As the law changes, the market changes – so this year will see many companies trying to read the tea leaves and adapt their offerings to take advantage of the emerging changes. The security marketplace is, apparently, constrained by the need for great privacy – it appears to be a zero-sum game – you can have privacy, or you can have security, you can’t have both. In the second half...
Enterprise security directors often count on an integration firm to handle jobs ranging from day-to-day activities to long-term, technology-laden projects. However, before entering a relationship, you must know what's reasonable to expect from an integrator – as not all are created equal. Here are some tips that might make the selection process easier. Completing comprehensive classwork An integrator's experience working in an enterprise environment is an obvious consideration. Ideally...
Integrators need to be well versed in Total Cost of Ownership (TCO), when discussing video surveillance options with their customers. Business leaders are looking for the best, most economical technology that will address their security needs, and they also want to avoid being blind-sided by unplanned technology operations and service costs. While most folks understand that the initial cost of a video surveillance system is not the same as the total cost of ownership, many might be surprised to...
Back in 1890, Samuel Warren and Louis Brandeis published a ground-breaking article in the Harvard Law review called ‘The Right to Privacy’. To this day, it is regarded as one of the most influential essays in the history of American law and is widely regarded as the first publication in the United States of America to advocate a right to privacy, articulating that right primarily as a ‘right to be let alone’. In this essay, the authors questioned whether the arrival of p...
Many people, quite correctly, point to Salesforce.com—which launched in February of 2000—as the first example of cloud computing. In the years following, the term ‘cloud’ became so popular and was applied to so many products and service offerings, that it became almost meaningless. The result was cloud confusion in the business world and in the media. In one stark example from 2008, Oracle CEO Larry Ellison described news stories about cloud as, ‘complete gibberis...
We must leverage existing technologies like social media monitoring, gunshot and weapons detection, and real-time watchlist alerting. We owe it to our children. The recent news of the Dallas elementary school shooting absolutely gutted me. It’s a tragic and incomprehensible loss of life. A question I hear being asked again and again – could technology have made a difference? From my experience, modern technologies can help schools mitigate some of the damage and provide an early w...
Currently and unfortunately, there is no such thing as Cloud Police. If there were, two-thirds or more of the companies using ‘cloud’ in their advertising and documentation would be in Cloud Jail for seriously misusing the word in their marketing. The term ‘Cloud’ is over-used and misused—sometimes intentionally and knowingly, but also often in ignorance. It’s just a word—but in the context of cloud computing technology, it does have a specific meaning...
Trevor Dearing, the EMEA Director of Critical Infrastructure Solutions at Illumio, said “It is encouraging to see NIST releasing updated guidance acknowledging the increase in cyber-attacks targeting the supply chain and the consequent necessity to bolster the supply chain’s cyber security. We can no longer turn a blind eye to the exponential increase in attacks on the IT systems of manufacturers, logistics companies and organisations, which ultimately target the operational part of...
Today, RFID readers can be found in numerous devices requiring user authentication, authorisation and access control, from doors to multi-function printers to point of sale terminals to computers and more. RFID is a simple, secure and convenient access control solution for end users and original equipment manufacturers. RFID readers/writers come with a broad range of form factors, capabilities and configurations. Choosing the right RFID reader When choosing a reader to embed into a system or d...
In the era of the ‘Great Resignation’, it may seem counterintuitive to say that people will power business security in 2022. However, a convergence of challenges over the past few years has led to an undeniable trend in the security industry: With more technology comes the need for more people to monitor, analyse and leverage the data that technology produces. Always-on approach to security Since businesses were forced into lockdown two years ago, we’ve seen technology adopti...
Most individuals have strong opinions about what is more essential to our civilisation: personal privacy or security. After more than a decade of technology enabling greater and greater amounts of Personally Identifiable Information (PII) and data harvesting, now the pendulum is swinging towards a society that places more emphasis on individual rights and privacies. This shift is manifesting in a variety of ways, quickly changing the technology, security and cyber security landscapes, and requi...
Software as a Service (SaaS) provides computer equipment, OS, and software customised to the user’s purposes as a service. Access control can work in the same way. If you work in the physical security industry, especially concerning access control, you have probably heard about the term ‘ACaaS’ recently. ACaaS is a combination of ‘access control’ and ‘SaaS’ (Software as a Service). From a semantic point of view, ACaaS means providing cloud-based access c...
Technology continues to transform the physical security industry, helping companies become more aware of the full spectrum of risks their organisation faces. Our new survey provides strong evidence that the use of these tools is solving some problems, but their implementation may create new challenges. In our 2022 State of Protective Intelligence Report, 93% of respondents said their company was actively adopting new threat intelligence, monitoring and alerting solutions for physical security,...
This is an era of digital revolution and with it comes dozens of new security dangers. Every gadget, from our smartphones to our security cameras, need some kind of protection from external hacking. However, how can we assure the safety of our devices, workplaces, etc.? Biometric security is one such security method that has emerged, since it is both efficient and perceived foolproof. It offers an additional layer of security for businesses and personal security systems. Biometric security syste...
Aligning physical and cyber defence for total protection
DownloadUnderstanding AI-powered video analytics
DownloadEnhancing physical access control using a self-service model
DownloadHow to implement a physical security strategy with privacy in mind
DownloadSecurity and surveillance technologies for the casino market
Download