Developing a bill of materials for an infrastructure is not difficult if you have the right information. One word of caution: Infrastructures are unique. Each is individual, so don’t depend on drop-down menus; it simply will not work. If one component within the infrastructure changes, take the time to check and see if the rest of the components need to be changed, too.
Let’s look at some questions and considerations when designing a network infrastructure for use by an IP/PoE (Internet protocol/power over Ethernet) video security system.
First, you should work with individual collection points. This could be when all devices (cameras/access controller) are routed to a single location or when there are multiple locations as in the case of individual IDFs (intermediate distribution frames).
For each location determine the following:
Cameras and number of cameras
- What are the manufacturer and model numbers for each camera? Knowing this will help to determine the bandwidth and PoE requirements.
- How many cameras are going to this location? If there are different cameras from different manufacturers, please list all of these by number.
- Break down these numbers further according to those that are 290 feet or less and those greater than 290 feet from a network connection and PoE source. You may think of IP/PoE limits in terms of 328 feet (100m) but conservative planning takes into account wire bends, which can contribute to increased resistance and decreased performance.
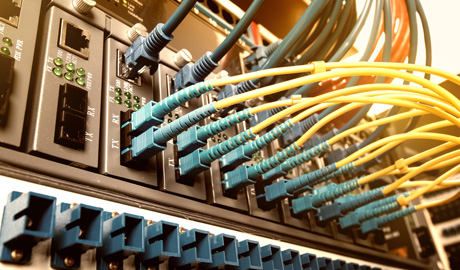
Type of cable
- What cable is installed? Existing installations, those which will convert from analogue to IP, probably already have either coax or fibre. For coax almost all existing installation will have RG59, but it’s important to confirm. Very old installation may even use aluminium shield cable, which will probably have to be replaced due to its high resistance.
- New installations will use Cat 5e or Cat 6.
- Fibre is more complex as you have to first determine the mode – single mode or multimode. Then you have to know the fibre size, which is usually a function of the mode. Single mode will generally be 9/1.25 while multimode can either be 62.5/1.15 or 50/1.25, depending on distance. Regardless, your fiber modems must match both of these aspects and bandwidth as well.
 |
| The type of cable will also determine if you need extra equipment |
The type of cable will also determine if you need extra equipment as only UTP or Ethernet cable can be directly connected within a network. Coax, single pair and fiber will all require some form of media conversion.
Cable length
- Choose necessary extenders. As previously noted at each collection point, divide your device connections into those less than 290 feet and those greater than 290 feet. For the latter, use the longest cable distance as your reference and determine the type of extenders required to meet the bandwidth and PoE device requirements. Using any device in the transmission path will require you to take into account its effect on bandwidth and PoE.
Network and PoE source (this can be the most difficult part)
- Managing the variables. While there are many IEEE standards governing network interconnections and PoE, the most important variables we are concerned with have no standards at all. They range from determining a real PoE budget, to how PoE is programmed, if at all, to internal switch bandwidth, sometimes called switch fabric, to the ability of individual ports to pass the required bandwidth from a camera.
- Two important things to keep in mind. First, your bandwidth must remain consistent throughout the transmission path. Second, your PoE source must be able to provide not only the power required to operate your device and any other devices in the path, but also power in the event of startup surges to avoid PoE shutdowns.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance













