 |
| Intelligent searches of video archives provide investigators faster access to any needed video clip |
That video analytics can be immensely useful in forensics is relatively less known. However, forensic search capabilities offered by some modern video analytics solutions can not only save investigators significant amounts of time but also help them find results more accurately. These solutions leverage facial recognition and advanced object tracking, demographic analytics, license plate recognition capabilities and other such powerful features to take forensic investigation to a whole new level.
Video analytics have earned a reputation as solutions that can provide real-time intelligence to enable immediate response. However, another aspect of video analytics is how the technology can be used for forensics. Basically, intelligent searches of video archives provide investigators faster access to any needed video clip based on the content of the video. It’s a monumental improvement over the old days of searching for hours while rewinding and fast-forwarding videotape.
The use of video analytics for forensics is a less well-known benefit of the technology, says Zvika Ashani, chief technology officer (CTO), Agent Video Intelligence (Agent Vi). “Most people associate it with events, like detecting a person approaching a perimeter,” says Ashani. “But video analytics can also be useful in a forensic sense. It can help an investigator who needs to go into a video archive and find evidence of an event.”
Defining queries with analytics speeds up forensic investigation
Analytics-based forensics enable investigators to define their queries. For example, a user might want to see all the blue trucks in an area in a specific time frame. “In seconds, we can provide results in terms of thumbnails – images that fit that query,” says Ashani. “They can zoom in and see what they’re looking for. Some customers understand this, and for some, it’s something new.”
Most of the video recorded on an NVR/HVR (network video recorder/hybrid video recorder) is never viewed, says Brian Lane, director of marketing, 3VR. But, when the time comes that a short piece of video is needed and there are thousands of hours of recorded video, analytics can greatly simplify the task. ”For example, say you are looking for a male between 40 and 50 years old, wearing a red shirt, headed west,” says Lane. “Using analytics on a 3VR system, you can type these parameters into the search fields, and the system will send back video of the closest results. If you know the face of the suspect, using a face analytic makes the search even easier. In a world where time is money, analytics can be used to save countless hours searching through video.”
Using facial, advanced object |
Tracking individuals and movements in forensic mode
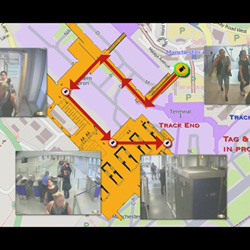
One of Ipsotek’s latest generation developments is Tag and Track, a video content analysis-based tracking system that operates on a network of overlapping and non-overlapping CCTV cameras to track a “tagged” individual. In the forensic mode of operation, the system can be used to analyse hours of incident-related video footage in minutes to produce a detailed account of individual movements in the surveillance area.
This product has the ability to identify behaviour, selecting persons/objects of interest and enabling them to be tracked going forward. The system can also analyse where that person has come from, the path they have previously taken through the network and therefore where they have been. This system can analyse thousands of hours of video footage within minutes, therefore assisting greatly in investigations in which tracking evidence is essential.
It is possible to search |
Facial recognition provides forensic capabilities
Another recent development is Ipsotek’s use of facial recognition technology to provide forensic functionalities. For example, it is possible to search for a new face within historical data, providing information on when and where a new person of interest was in a facility over the previous month.
In an operational role, once a person has been tagged, the system takes over and automatically follows the person, intuitively waiting and reacquiring them should they disappear into areas not covered by the CCTV network. The system will also track the tagged individual backwards in time to show where that person has been. Tagging is either performed by operators using the Graphical User Interface or automatically with certain video content analysis and/or other if triggers (e.g., intrusion) have been satisfied or another sensor input trips (e.g., facial recognition).
The system memorises the appearance of the tagged individual (based on a number of different visual identifiers) and tracks this collection of information. The Tag and Track system automatically learns the geometry of the camera network and understands where an object is likely to reappear when it goes out of one camera view.
Discover how AI, biometrics, and analytics are transforming casino security












