Siemplify, the independent provider of security orchestration, automation and response (SOAR), and Anomali, the provider of intelligence-driven cybersecurity solutions, announces a partnership that delivers an integrated best-of-breed SOAR and threat intelligence platform (TIP) solution, making intelligence-driven security operations simple and accessible to organisations of all sizes.
SOAR and TIP solutions are foundational technologies for every modern security operations team looking to combat alert fatigue, embed context into security investigations, and effectively contain and respond to threats. The partnership between Siemplify and Anomali delivers a unified best-of-breed SOAR and TIP integration that enables rapid time-to-value with minimal effort.
Long-standing partnership
As part of the partnership, Siemplify is launching ThreatFuse, an add-on module to the Siemplify SOAR platform, powered by Anomali, which ingrains threat intelligence across the entire detection and response lifecycle. From enrichment with real-time threat indicators, through threat hunting and intelligence sharing, security analysts can validate, investigate and respond to threats with unprecedented speed and precision.
ThreatFuse is generally available from Siemplify. Siemplify’s ThreatFuse offering evolved from a long-standing partnership between the two companies via the Anomali ThreatStream marketplace, as well as customer-driven integrations to power Siemplify SOAR playbooks with high-fidelity threat intelligence.
Real-time threat indicators
Supporting Siemplify in its introduction of ThreatFuse was a natural evolution of our existing partnership"
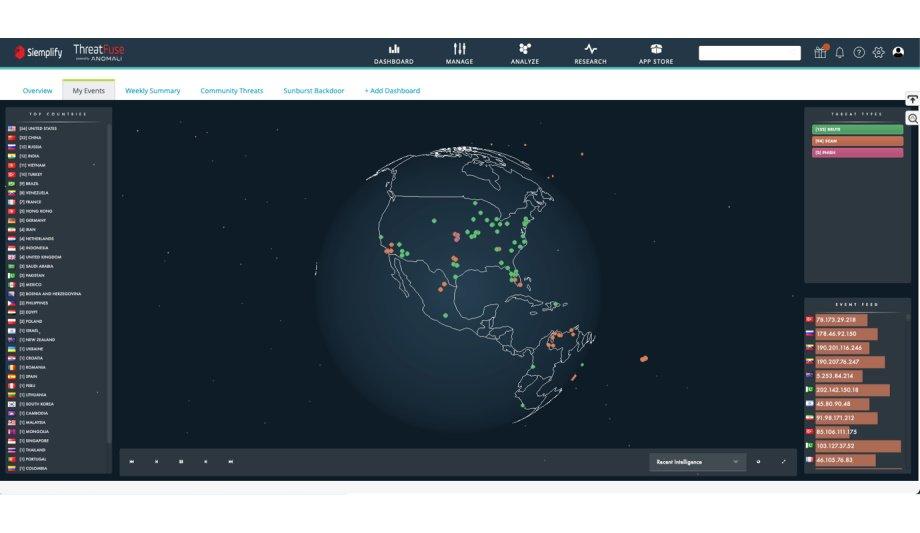
The Siemplify ThreatFuse dashboard used for enrichment with real-time threat indicators, through threat hunting and intelligence sharing, security analysts can validate, investigate and respond to threats with unprecedented speed and precision
“Until today, organisations looking for a unified SOAR and TIP solution were forced to compromise on one or both of these critical security operations capabilities,” said Dennis Shaya, general manager and head of alliances at Siemplify. “We are thrilled to partner with Anomali to offer our customers a best-in-class TIP offering that is tightly embedded in the Siemplify SOAR platform.”
“Supporting Siemplify in its introduction of ThreatFuse was a natural evolution of our existing partnership,” said Dan Maier, CMO of Anomali. “ThreatFuse offers a streamlined experience, allowing customers seeking robust TIP-SOAR integration to benefit from simplified implementation and management.”
Intelligence-based investigations
The unified SOAR/TIP solution accelerates time-to-value by delivering several use cases out-of-the-box to better perform:
- Event Triage: Aggregated threat intelligence supports event triage and decision-making by determining if an indicator is suspicious and at what severity level. Deep intelligence context is added to events, providing detailed information about associated threat actors and any known campaigns when a malicious threat is discovered.
- Intelligence-Driven Investigation: Contextual intelligence drives intelligence-based investigations that use associated indicators from an enriched entity to find other relevant indicators of attack.
- Proactive Defence: Newly discovered indicators can be used to trigger playbooks that defend networks through automatic detection and response. Filters and thresholds can be applied to limit the types of threats or entities that trigger automated response.
- Intelligence Sharing: False positives in an environment can be shared to make sure the data is not used in the future. ‘Trusted Circles’ enable intelligence sharing with the security community when new threat indicators are discovered.
Siemplify and Anomali have planned a joint webinar on February 4 to provide more information about this partnership. Reserve spot to learn how one can combine SOAR and TIP to drive intelligence-driven security operations.
Find out about secure physical access control systems through layered cybersecurity practices.