Fujitsu Laboratories Ltd. has developed a digital identity exchange technology that makes it possible for individual users and service businesses involved in online transactions to confirm the identity of other parties in transactions. The rapid advance of digitalisation in recent years has been accompanied by a dramatic rise in the number of online transactions in which users cannot see one another face to face, making it difficult to judge the credibility of the other party and leading to heightened concerns around trust.
With reports of fraud and instances of people falsifying personal credentials like work history and professional qualifications growing increasingly prevalent, ensuring the circulation of high-quality, reliable identification data poses an urgent challenge to users and businesses alike.
DID utilising blockchain
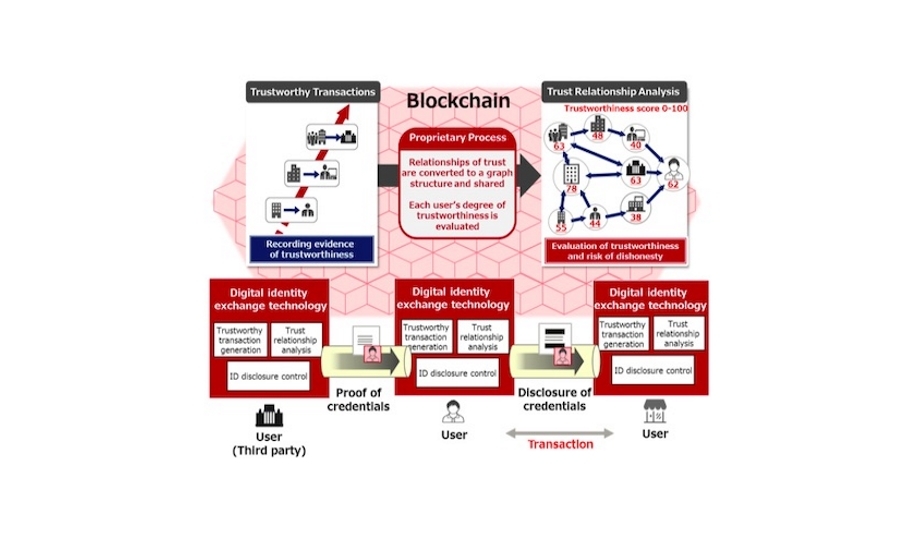
Fujitsu's new digital identity exchange technology promises a future in which people can enjoy online services more safelyTo address this, Fujitsu Laboratories has developed technology based on a Decentralised Identification (DID) utilising blockchain that analyses the risk of falsification and the trustworthiness of the other party's personal credentials when a user conducts a transaction online. The new technology achieves this through a mutual evaluation of the users when a transaction occurs, and by inferring the relationships between users based on past transaction data.
Fujitsu's new digital identity exchange technology promises a future in which people can enjoy online services more safely, offering user-friendly features including graphics to visualise the relationships between users, as well as a unique ‘trust score’ that makes it easier to determine each user's trustworthiness before starting a transaction.
Accurately discloses party’s identity
In recent years, there has been an increase in new forms of business based on trust between people or companies, including sharing and matching services. In these sorts of digital businesses, it remains crucial to accurately convey the identity of other party in the transaction.
There are now ongoing discussions around the use of blockchain technology in these kinds of transactions as a form of decentralised identification that accurately discloses each party's identity to the other parties, as guaranteed by an impartial third party.
DID is a system in which a third party guarantees the accuracy of an individual's identity and personal credentials
DID is a system in which a third party guarantees the accuracy of a given individual's identity and personal credentials. However, if a service business or user conspires with a third party acting in bad faith, it is possible to falsify a person's history or credentials, creating the risk that this falsified information will spread very widely without being discovered.
Digital identity exchange technology
Moreover, as the number of users who utilise these services increases, it becomes more difficult for users or a third party to grasp what sort of people the other parties are, increasing the possibility of maleficence. This necessitates a system whereby users can evaluate for themselves the truthfulness of the identity of the other parties in the transaction.
Expanding on its past use of blockchain technology, Fujitsu Laboratories has developed a new digital identity exchange technology for safely circulating personal credentials in a form that enables users to confirm the trustworthiness of the other party, drawing on factors including the status of previous transactions and evaluations by users who had engaged in transactions with the party in question, as part of a decentralised identification system.
- Generating trustworthy transaction data
With Fujitsu's new identity exchange technology, evaluations (e.g. reputation and rating) for each user in a transaction are recorded as a series of transaction data. By storing these evaluations on the unfalsifiable distributed ledger of a blockchain, this system can improve the reliability of insights into the trustworthiness about each user.
- Analysing relationships of trust
This system converts the trustworthy transaction data about individuals shared on the blockchain into a graph structure so that the relationships between users can be understood. A trustworthiness score is attached to each user by weighting factors including how many trusted users evaluate them highly. Even if a user colludes with a third party to improperly raise their evaluation, the graph-structured relationships will reveal information such as the weakness of their relationships with other users, giving the system the potential to identify misrepresentations.
- Disclosing necessary information only
Users can have their credentials verified with only a partial disclosure of relevant data, allowing for safe and highly reliable transactions without forcing users to offer unnecessary personal details.
Determining trustworthiness of other party
Fujitsu Laboratories will continue to develop IDYX as a trust-based service platform supporting digital businessThe newly developed technology analyses the trust relationships of each user, allowing the system to pre-emptively determine the trustworthiness of the other party in a transaction. The newly developed technology allows users to easily confirm information about which companies and individuals can be trusted in transactions in a variety of digital business situations, helping to build a digital ecosystem that transcends the boundaries of companies and industries and makes safe and secure online transactions a reality for all.
Fujitsu Laboratories will continue to develop IDYX as a trust-based service platform supporting digital business, conducting trials in a variety of fields, beginning with the finance industry. In addition, Fujitsu aims to implement this technology during fiscal 2019 as a new functionality in its Fujitsu Intelligent Data Service Virtuora DX Data Distribution and Utilisation Service, a cloud-based solution for data utilisation powered by blockchain technology.
Learn why leading casinos are upgrading to smarter, faster, and more compliant systems