A single compromised account can be a gateway for attackers to access confidential data, leading to financial loss, legal consequences, and damage to the company’s reputation. This threat is not limited to any specific platform and affects everything from email accounts to secure business databases.
Before exploring strategies for MSPs to mitigate this cyber risk, let’s first understand what an account compromise is, its security impacts, and ways to detect it.
What Is a compromised account?
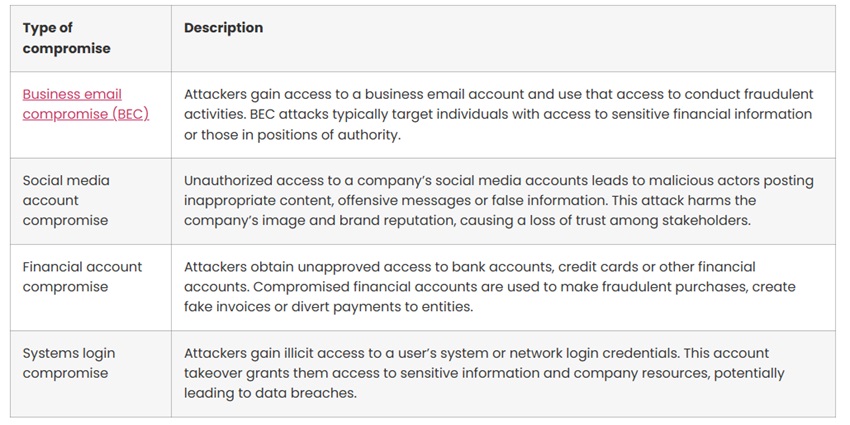
A compromised account is when unapproved individuals or threat actors access a user’s credentials or find another way to act on their behalf. It is often the first sign of a security breach.
A compromised account leaves the door open for dangers such as:
- Ransomware locks the digital systems or encrypts the data until the user pays a ransom.
- Data breach, which involves theft of personal or business data.
These attacks usually occur through social engineering, brute force attacks, or keylogging malware.
The ripple effects of compromised accounts
The impact of an account compromise extends beyond the initial unauthorised access. Here are the main consequences:
Data Theft
MSPs must prioritise robust security measures, including password policies, and multi-factor authentication
Account compromises can lead to loss or unauthorised access to sensitive data, including customer information, intellectual property, and proprietary business data. Data theft is a critical concern for MSPs and their clients. Kaspersky found that 50% of consumers would stop using an online business if it suffered any form of data breach.
MSPs must prioritise robust security measures, including password policies, multi-factor authentication, and continuous monitoring of account activity to detect and promptly respond to suspicious actions. Discover key strategies to prevent data breaches.
Legal and Compliance Implications
Individuals or entities affected by the account compromise may file lawsuits against the organisation responsible for safeguarding their data. For instance, most MSPs sign contractual agreements with clients that include provisions for data security and confidentiality. A compromise may lead to a contract breach, triggering legal consequences and financial penalties.
If an account compromise leads to a breach, users may also face increased scrutiny from regulators and the public. This loss of trust leads to higher compliance costs and strict legislation.
Financial Loss
The time required to investigate and remediate the compromise causes operational delays
When attackers gain unauthorised access to accounts, they can directly siphon funds from bank accounts, execute fraudulent transactions, or make purchases using stolen credit information.
This financial loss requires a complex recovery process involving banks, credit companies, and law enforcement. The time required to investigate and remediate the compromise causes operational delays, affecting project timelines and business operations.
How to detect if an account was compromised
To ensure the security of both their own and their client’s data, MSPs must diligently monitor internal networks and client systems. The following indicators of compromise (IOC) help MSPs identify if an account has been attacked:
- Unusual data movements: Data transfers to external networks or file transfers during non-business hours.
- Abnormal user activities: Users with high-level access that deviate from their regular patterns, such as logging in at unusual hours or accessing data irrelevant to their role.
- Geolocation anomalies: Login attempts from unexpected locations, particularly countries where the client organisation has no presence.
- Failed login attempts: A surge in unsuccessful login attempts as a result of a brute force attack.
- Database query spikes: An unusual increase in database access or queries due to attackers probing for sensitive information.
- Sensitive file access: Increased attempts to access critical files, whether through sheer volume or phishing.
- Unexpected changes in configuration management: Modifications to system settings not aligned with standard operations.
Strategies for account compromise prevention
Stolen account credentials are the reason behind 49% of cyberattacks. To mitigate this threat, MSPs need both immediate response tactics and long-term preventative measures.
Immediate Response Strategies
- Suspend account/revoke access: The first step involves immediately suspending or revoking access to the compromised account to prevent further wrongful activities.
- Update passwords: Immediately update the compromised account’s password and any other accounts sharing that password.
- Notify affected users: Many data protection regulations, such as GDPR, require organisations to promptly notify affected users and authorities in the event of a data breach.
- Conduct a security audit: Review and analyse how the compromise occurred to close security gaps and prevent similar breaches.
Examine account activity:
Closely examine account activities such as sent mail and shared, downloaded, or deleted files. If the bad actor made changes to the account settings, roll back the changes needed to immediately secure the account.
If law enforcement or cyber insurance carriers need to get involved, try to preserve the evidence needed for a proper investigation.
Long-Term Preventive Measures
- Multi-factor authentication (MFA): Add an extra layer of security to account access, making it harder for attackers to gain unwarranted entry.
- Employee training: Regularly educate staff on security best practices, phishing awareness, and safe internet habits to build a human firewall.
- Regular risk assessments: Periodic assessments help MSPs identify potential weaknesses and take corrective measures before attackers exploit them to compromise accounts.
- Threat detection tools: These systems identify and flag suspicious activities, such as data exfiltration or unusual file downloads, for MSSPs and MSPs to respond to threats promptly, preventing further compromise.
Mitigate the risk of account compromise with SaaS Alerts
With SaaS Alerts, MSPs get continuous visibility into activities within cloud-based applications to detect potential account compromises. SaaS security software analyses user behavior and raises security alerts when deviations from normal patterns occur, such as login attempts from unauthorised locations and changes in user permissions.
SaaS Alerts also integrates with internal MSP tools, providing a centralised dashboard for monitoring and managing security alerts across multiple client environments. In the event of an account compromise, our remediation capabilities automatically lock down compromised accounts to minimise potential damage.
Discover how AI, biometrics, and analytics are transforming casino security













