Security and IT teams have recently been facing a tidal wave of highly publicised breaches stemming from unpatched vulnerabilities, such as the attacks originating from a zero-day Windows printer spooler vulnerability dubbed ‘PrintNightmare’ (CVE-2021-34527). These software vulnerabilities are a major threat vector that security teams need to address.
They are excited to announce the launch of the vulnerability management module for VMware Carbon Black Cloud Endpoint. By adding vulnerability management to VMware Carbon Black Cloud Endpoint, customers can further streamline and consolidate key security functionality into a single cloud-native agent and console.
Delivering risk-prioritisation
VMware’s new offering delivers risk-prioritisation and increased visibility so security teams can focus on exploitable vulnerabilities. “In the first half of 2021, we’ve well surpassed the number of zero-days exploited than were seen in all of 2020. Vulnerability management must be a core functionality for security teams as they fight back against an onslaught of attacks.”
Organisations can now monitor their Windows and Linux endpoints for OS and application vulnerabilities
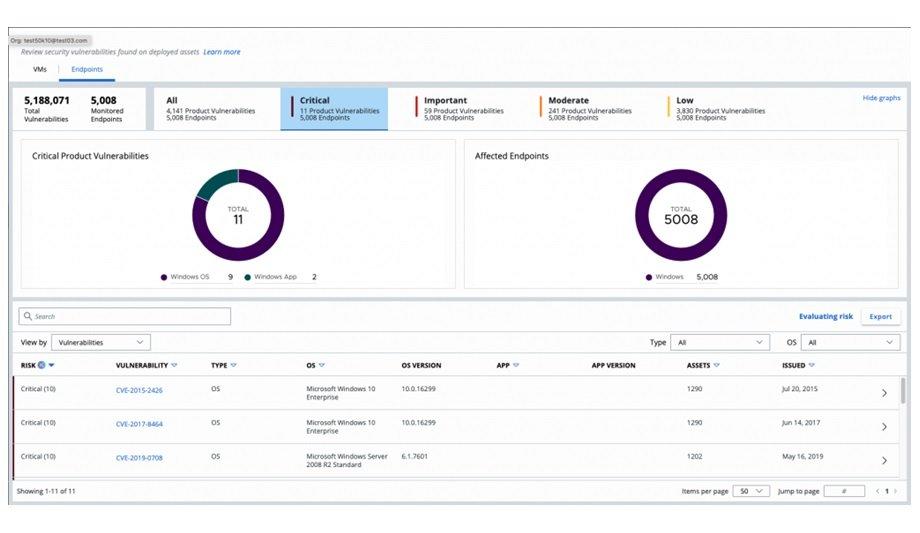
“Our vulnerability management module allows defenders to easily prioritise which vulnerabilities are considered critical, all within one single platform,” said Scott Lundgren, CTO, Security Business Unit, VMware. Organisations can now monitor their Windows and Linux endpoints for OS and application vulnerabilities and prioritise remediation based on the risk of exploit.
Day security tasks
By leveraging the existing lightweight VMware Carbon Black Cloud Endpoint sensor to collect application and OS data and combining it in the cloud with Kenna Security’s enriched vulnerability insights and risk scores, customers can reduce the system impacts and manual efforts associated with point-in-time vulnerability scans and manage their vulnerabilities in an ongoing fashion alongside their other day-to-day security tasks.
The vulnerability management module helps security teams understand the current state of endpoint vulnerabilities within the VMware Carbon Black Cloud console so they can act quickly and with context in the event of an attack. The increased visibility proactively reduces the attack surface because organisations can better identify vulnerabilities and harden endpoints before a vulnerability is exploited.
Creating resource overhead
This new offering extends VMware’s existing partnership with Kenna Security to provide dynamic risk scoring
It’s important to note how increased visibility is achieved. Traditionally, legacy vulnerability vendors would perform a scan on the endpoint itself, creating resource overhead. Because of this overhead, customers had to schedule time (usually once a month or quarter) to perform the scan during downtime. This meant more planning and less frequent data updates.
With this new offering, VMware Carbon Black Cloud not only offloads the overhead from the endpoint to the cloud, but it automatically updates vulnerability data every 24 hours. This scanless approach to vulnerability management eliminates the need to plan for downtime before scanning and automatically provides up-to-the-minute vulnerability information. This new offering extends VMware’s existing partnership with Kenna Security to provide dynamic risk scoring and prioritisation for endpoint vulnerabilities without the need to rely on scanner data alone.
Science-based approach
Within the VMware Carbon Black Cloud, one will see a prioritised list of CVEs (Common Vulnerabilities and Exploits) that is updated with a no-touch, incredibly low-impact data collection. Their partnership with Kenna Security enables the integration of their unique data science-based approach to risk prioritisation.
Their partnership with Kenna Security enables the integration of their unique data science-based approach
“Modern vulnerability management requires visibility, accuracy, and velocity to achieve successful outcomes. Extending our partnership with VMware Carbon Black Cloud from their workload offering to their endpoint offering will arm security teams with visibility into the vulnerabilities in their endpoints, accurate data science-based risk scoring, all at the speed required for businesses to prioritise the right actions at the right time and meaningfully reduce the risk for their organisations,” said Ed Bells, CTO and Co-Founder, Kenna Security, a Cisco Company.
Additional overhead cost
This new offering enables risk-based vulnerability management to be built into one single agent and delivered with the standard VMware Carbon Black Cloud sensor at no additional overhead cost. By focusing on intelligent risk scores that go beyond the industry standard of CVSS and indicate real-world exploits of vulnerabilities, security teams can reduce the number of noisy alerts and false positives and spend time remediating vulnerabilities that create real risk in their environments.
This allows organisations to better identify the true risk of every endpoint, with easy-to-understand risk scores and detailed intelligence. Meanwhile, security teams can focus on the vulnerabilities that matter, remediate them faster, and adopt a proactive security posture focused on protecting against emerging threats.
From facial recognition to LiDAR, explore the innovations redefining gaming surveillance