Airport security
Transportation systems need robust physical security to protect human life, to ensure economic stability, and to maintain national security. Because transportation involves moving large numbers of people and critical goods across vast, often interconnected infrastructure, it presents a highly attractive target for various threats. More threats equate to a greater need for security. We asked our Expert Panel Roundtable: What are the emerging applications of physical security in the transportation...
3DX-RAY, a pioneer in advanced X-ray imaging technology, is pleased to announce the successful acquisition of a significant double-digit unit contract with the esteemed Indian partner for the ThreatScan LS1 system. This innovative solution has been selected for its impressive size, ruggedness, and exceptional capability to efficiently handle Passive Infrared (PIR) devices activated by X-ray technology. EOD and security applications The ThreatScan LS1 is an advanced X-ray imaging system specif...
Omnisys introduces the BRO (Battle Resource Optimisation) C-UAS system, a field-proven, real-time optimisation platform built to help airport organisations mitigate the growing threat of unauthorised and hostile unmanned aerial systems (UAS). The system enables data-driven, proportionate responses to aerial threats, ensuring passenger safety while maintaining airport operations. In recent months, airports across Europe and the US have faced repeated shutdowns due to unauthorised drones. Munich...
VITEC is pleased to announce that its IPTV and digital signage system will power content at the Dubai Airshow 2025, 17-21 November, at Dubai World Central. VITEC’s solution will deliver real-time video streaming of live flight demonstrations, exhibitor presentations, television streams and event details, powering 4K content to displays across the show floor. The VITEC system comprises a centralised IPTV server, Head-end chassis with g45xx Series Satellite Gateways, ultra-low latency encod...
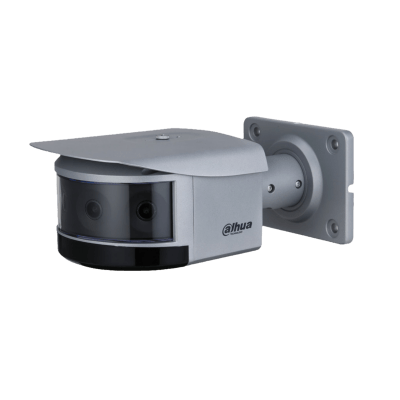
With the new Panomera® V8, Dallmeier presents a revolutionary camera that combines state-of-the-art multifocal sensor technology and artificial intelligence in one system – for a seamless 180° view without blind spots and the most precise analytics, even over large areas. Security redefined: 180° without compromise With eight lenses, eight sensors, and eight AI chips, the Panomera® V8 achieves a 180-degree field of view and enables coverage of a very large area...
Every morning, it happens in offices everywhere: that tiny, almost imperceptible delay. The brief pause to find a keycard, the slow queue at the security desk, the momentary friction that interrupts the rhythm of the day. This isn't just a minor annoyance—it's a Productivity Tax. These small moments add up, draining efficiency and leaving teams frustrated before they even get to their desks. But what if they could eliminate that friction with a single glance? What if access control wasn't...
News
Building on their highly popular series of integrated high-security solutions events, the CNI Security Group has announced their next event, ‘Protecting CNI Scotland – The importance of cyber-secure solutions in critical national infrastructure’. Designed for all end users, consultants and system designers in the CNI sector, the free-to-attend event will be held at Dakota Eurocentral, Motherwell, on Wednesday 19th November, between 9:30 am and 4 pm. The event will show insights from multiple perspectives into the importance of cyber-secure solutions in critical national infrastructure environments. Cybersecurity and end-users The format of the day will include presentations and panel discussions from specialists in cybersecurity and end-users in the CNI space - all looking to share their own 'real world' experiences. In addition, pioneering security industry manufacturers barox Kommunikation, Hirsch UK, Nedap Security, ISM Ltd, Commend, Overview and Lochrin Bain, will be showcasing the very latest in cutting-edge CNI/NPSA security technologies - suitable for deployment across high security sites, including, utilities, power, prisons, nuclear, and airports. Cyber and physical security The highlight of the morning programme will be a keynote presentation from the award-winning Mike Gillespie FCIIS MSyl CIRM of Advent IM. A specialist in Cyber Security and Governance, Mike is a Chartered Institute of Information Security Fellow and Senior Vice President Europe at CSCIS, and a seasoned expert in cyber risks. A former Security Institute Director, he advises globally and contributes to major media, and will be speaking about cyber and physical security and promoting awareness of organisational threats. National security policy and implementation In the afternoon, what is set to be a mind-blowing panel discussion session, entitled ‘What lessons have we learnt from experience? What does the future hold? How can we be more CNI resilient?’ comprising of senior pioneers in the CNI space, will be led by Chair of CNI Scotland, Malcolm Warr OBE. Malcolm has over 20 years’ experience in National security policy and implementation, and has chaired defence, cyber and physical security conferences internationally. Details of additional speakers and panellists will be released in the coming weeks. Cyber security on a global scale “We are so excited about our first event in Scotland, particularly as it is building up to be the best one so far. Once again, we have a fantastic line-up of presenters and panellists, from specialists in cyber security on a global scale, to end users in the CNI space,” says Sara Fisher, Chairperson CNI Security Group. “More than that though, and on a personal note, I feel extremely privileged to be working with such an amazing team of people, from fellow CNI Security Group members and partners, to those experts who are giving up their time to share their knowledge and experience with our audience. Our delegates are in for a really spectacular day.” Full agenda and register for the free-of-charge event Lunch will be provided for all attendees, and the day will finish with post-event drinks. To see the ‘Protecting CNI Scotland’ full agenda and register for the free-of-charge event, interested parties should visit the website. As places are strictly limited, allocated tickets will be offered on a ‘first come, first served’ basis, so please book early to reserve your place. Due to limited space, strictly no other manufacturers or suppliers can be accepted to this event.
Just a few months after the release of RDID 1.0, Spotter Global is proud to announce the release of RDID 2.0. This sensor is for detecting and tracking FAA-compliant Wifi and Bluetooth drones as well as their pilots. Upholding the Spotter Global motto, “First to Detect, First to Protect™”, RDID 2.0 will empower law enforcement and security personnel with a cost-effective solution to reliably detect 90+% of drones in their airspace, with zero false alarms and swiftly reach the location of the drone pilot for any needed intervention. GSX visitors can see a demonstration of RDID 2.0 at booth #1319 or in Honeywell’s Commercial Security Suite #341. Law enforcement branches RDID’s unparalleled Drone ID tracking system capitalises on the FAA requirement for all drones over 250 grams to broadcast their serial number, location, and pilot location when in flight. RDID is easily deployed, can be set up anywhere on a simple tripod, covers nearly 700 acres of area (3 km range, 360°) with a single device, generates zero false alarms, detects and tracks both drone and drone operator locations with precision. Combined with Spotter’s NetworkedIO (C2 software) the RDID seamlessly integrates with existing infrastructure including PTZ cameras, radars, and VMS systems. This new CUAS solution will enable law enforcement branches and security teams charged with protecting critical infrastructure, data centres, college campuses, crime scenes, and other locations to quickly “Find the pilot. Stop the Drone.” Mitigating active drone threats Production units will be delivered in November of 2025, and are available for pre-order Just this summer, RDID enabled a city law enforcement office to catch two drone pilots illegally flying their drones over a high-attendance stadium event. Because security and law enforcement teams must abide by FAA restrictions that prevent them from jamming or using hard-kill solutions against drones, the ability to quickly locate drone operators engaged in ongoing criminal drone activities is one of the few legal avenues open for mitigating active drone threats. “Spotter is on a very rapid development pace, focusing on delivery not just the best radar and Drone ID sensors in the world but solutions to customer’s security problems,” says Logan Harris, Spotter’s CEO & President. “The release of RDID 2.0 is exciting because now the RDID also detects the very cheap and shorter range drones that one can buy on Amazon for a few hundred dollars” Preventing harmful incidents Production units will be delivered in November of 2025, and are available for pre-order. Driven for 16 years in the mission of “Preventing Harm™,” Spotter Global produced the very first compact surveillance radars for Special Forces back in 2009. The company later pioneered radar AI software, revolving radar drone detection, and recently released the first C2 security software to combine Radar AI and Video AI. RDID 2.0 represents Spotter Global’s latest step in breaking security industry barriers to prevent harmful incidents before they happen.
Navigating through the annals of airport security, one discerns a compelling narrative of evolution and innovation tailored to address the fluctuating threat levels and the burgeoning number of air travelers globally. From manual checks to the current era, where technology plays an instrumental role in securing airports, the trajectory of advanced airport security systems illustrates a relentless pursuit of enhanced safety and efficiency. The paramount need to shield airports from potential threats has propelled continuous advancements in their security systems, ensuring a safe transit space for millions of passengers. Biometric security A surge in the adoption of biometric technology within airport security paradigms exemplifies the integration of enhanced security with operational efficiency. Biometric security systems, leveraging unique physiological characteristics such as fingerprints, facial features, and iris patterns, not only fortify security but also streamline passenger flow through airports. By automating identification processes, airports can ensure secure and expedited transitions for passengers, from check-in to boarding, while minimising queues and facilitating smoother operations. The global pandemic further bolstered the adoption of contactless biometric systems, contributing to a safer and more hygienic travel environment. Advanced CCTV systems CCTV systems within airports have transcended beyond mere surveillance to become comprehensive security solutions, interweaving advanced technologies such as Artificial Intelligence and Machine Learning. Modern CCTV systems provide real-time analytical data, enabling security personnel to detect and respond to anomalous activities swiftly and effectively. According to the Civil Aviation Authority, the UK hosts some of the world’s busiest airports, necessitating a vigilant eye that can concurrently ensure safety and manage enormous passenger volumes. The data and insights derived from these advanced CCTV systems are pivotal, enabling strategic deployment of security resources and facilitating preemptive actions against potential security breaches. Sophisticated door entry systems Ensuring secure access to critical areas within an airport is paramount to safeguarding both passengers and assets. Advanced door entry systems, which employ technologies such as smart cards, biometrics, and multi-factor authentication, restrict access to authorised personnel, thereby fortifying physical security barriers. These systems not only deter unauthorised access but also provide a traceable log of entries and exits to sensitive zones, ensuring accountability and enhancing investigative capabilities in the event of a security incident. Unified airport security systems Conjoining the various strands of security technologies, unified airport security systems stand out as a beacon for the future trajectory of airport security. Integration of biometric security, CCTV surveillance, and advanced door entry systems, underpinned by a robust cybersecurity framework, manifests as a cohesive security apparatus that is both resilient and adaptive. By fostering seamless communication and interoperability among various security technologies, airports can cultivate an environment that is comprehensively secure, efficiently managed, and prepared to adapt to the evolving threat landscape. Power of Artificial Intelligence The advent of Artificial Intelligence (AI) has inaugurated a new chapter in the book of advanced airport security systems, by adding a layer of predictive analytics and automated functionalities that enhance the responsiveness and effectiveness of security protocols. AI integrates into various facets of security systems, including CCTV surveillance and access control, offering a smart, adaptive, and highly efficient security management approach. For instance, AI-enabled cameras can autonomously identify and alert security personnel about suspicious activities, unattended objects, or crowd anomalies, ensuring that potential threats are identified and mitigated in real-time. Furthermore, AI’s capability to analyse and learn from data enables airports to continually refine and augment their security measures based on emerging trends and threat patterns. Cybersecurity In an era where data is paramount and connectivity is pervasive, safeguarding the digital realms of physical security apparatus emerges as a pivotal facet of airport security. Cybersecurity in airport security systems ensures that the technologies deployed, such as biometric scanners, CCTV networks, and door entry systems, are impervious to cyber-attacks and data breaches. A secure cyber framework not only protects sensitive data from being compromised but also ensures that the integrated security technologies function cohesively without being sabotaged digitally. This includes employing firewalls, encryption, and multi-factor authentication, and also ensuring regular audits and updates to safeguard against evolving cyber threats, thereby maintaining the integrity and functionality of the physical security infrastructure. Standardisation in airport security As air travel inherently connects various corners of the globe, the standardisation and collaboration in security protocols across international borders are essential to ensuring a universally secure and efficient passenger experience. The International Civil Aviation Organisation (ICAO) and various regional bodies work towards crafting guidelines and standards that shape the security protocols of airports globally. Through international collaboration, airports can share insights, innovations, and threat intelligence, enabling a collective enhancement of security measures. Additionally, standardised security practices ensure that passengers encounter a consistent and predictable security process, irrespective of their travel destination, thereby enhancing passenger experience and global security simultaneously. Monumental advancements In conclusion, the paradigm of airport security has witnessed monumental advancements, each epoch ushering in more refined and robust security measures. As the volume of air travelers escalates and the complexity of potential threats magnifies, the continuous evolution and integration of advanced airport security systems remain paramount. In navigating towards a future laden with unseen challenges, the harmonious fusion of technology, strategy, and proactive security management will steer the course towards safer skies and secure journeys.
Texas-based Garrett Metal Detectors announced that its Paragon walk-through metal detector had met the European Civil Aviation Conference (ECAC) Standard 2.1 with SMD performance requirements. Meeting the laboratory testing requirements and subsequently receiving the review and endorsement of the ECAC CEP Management Group is the most stringent prerequisite to achieving ECAC certification, and grants automatic eligibility for EU approval of the product along with the stamp that marks products as confirmed by the CEP to meet ECAC/EU performance standards. Products listed on the European Commission's KSDA site are also eligible to pursue non-aviation bids and RFQs that list ECAC-certification as a product spec. ECAC certification "ECAC certification is a critical confirmation of Paragon's premium capabilities and suitability for high-security applications in the global marketplace," said Leonid Zelenkevich, Garrett Director of International Security Sales. He adds, "ECAC testing standards are respected well beyond the borders of the European Union, and this achievement will allow Paragon to bring its advanced feature set and industry-renowned detection precision to the fast-moving and sophisticated world of airport security." Leonid Zelenkevich continues, "Airports and other pedigree institutions previously forced to settle for outdated – but certified – models can breathe a sigh of relief now that a modern metal detection system has achieved this important performance benchmark." Long future of product development "More than that, end users can look forward to a long future of product development within this advanced platform, with groundbreaking software updates, powerful new accessories, and other enhancements designed especially to serve the needs of the aviation industry," concluded Leonid Zelenkevich. The Garrett Paragon is manufactured at Garrett's Garland, Texas facility with appropriate design patents and trademark protections. All Paragon units with software version 2.00.1 or later contain the passing version of the ECAC screening programme. Garrett encourages security customers to insist on buying genuine products from reputable companies to ensure quality, product performance, and effective security operations.
3DX-Ray announces a contract for the sale of further ThreatScan®-AS1 systems to a Middle Eastern Law Enforcement Agency. This sale is a follow-on order to multiple similar systems already in service with the agencies EOD and search teams. The 3DX-RAY ThreatScan®-AS1(ISC) is a robust amorphous silicon portable X-ray inspection system. It comprises as standard a detector panel with an imaging area of 43cm x 35cm, a new high penetration 150kV generator, and a laptop along with batteries, chargers, the user-friendly 3DX-RAY ThreatSpect software, wireless communication and transport case. The AS1(ISC) is simple to use and produces extremely high-quality, sub-millimetre resolution images in real time. User applications and threat scenarios The system is fully integrated, with a primary display, computer, communications and power supplies consolidated into a single, waterproof rugged case. With the addition of a secondary display tablet, ThreatScan®-AS1(SC) offers high flexibility in deployment to meet the wide variety of user applications and threat scenarios. Inspection of suspicious bags and packages ThreatScan®-AS1(ISC) is perfectly suited for the EOD community and the inspection of suspicious bags and packages The ThreatScan®-AS1(ISC) is perfectly suited for the EOD community and the inspection of suspicious bags and packages in environments like mass transit rail and bus stations, shopping centres, airports, and sports venues. This system is engineered for straightforward deployment and operation, delivering optimal imaging capabilities within a single integrated unit for first responders, including police, border officers, military personnel, and both private and government security agencies. General security inspection All ThreatScan® systems can be used to inspect suspect bags and packages in mass transit areas as well as general security inspection by first responders such as Police, Military and Private and Government Security agencies. 3DX-RAY LTD, CEO, Vincent Deery, said: "This follow-on contract shows that a long-established user has continued faith in our systems but also underscores our commitment to supporting our law enforcement customers with advanced technology that enhances their capabilities in ensuring public safety."
At Inter Airport Europe 2025 (7-9 October 2025) in Munich, Germany, Dallmeier electronic and Navtech Radar will be showcasing their latest technologies for integrated security and process solutions in airport operations at stand 720 in hall B6. The focus will be on video and radar technologies to increase security, make processes more efficient, and reduce costs significantly. Dallmeier solutions are used at airports worldwide throughout the entire process chain, including car parks, terminals, the apron area, and the runway, as well as perimeter security. Combining “Made in Germany” video technology with Navtech Radar’s highly developed radar systems enables holistic situational awareness for airside operations in all weather and lighting conditions. Integrated video and radar solutions Dallmeier has developed the Panomera Perimeter solution, which uses specialised AI Fences and patrols alone are no longer sufficient to prevent unauthorised access to or disruption of the airside area. In response, Dallmeier has developed the Panomera Perimeter solution, which uses specialised AI to provide optimum perimeter protection. In cooperation with Navtech Radar, a fully integrated system of radar and video data has been created that enables the seamless monitoring of large areas. Security forces and those responsible benefit from a lower false alarm rate and direct visual verification in real time. Panomera S8 Runway Runways also present a significant challenge for optical monitoring systems. Without an overview, it is difficult to control processes efficiently. This is where the Panomera S8 Runway comes in. The combination of two multifocal sensor cameras at a single installation point creates an extremely wide horizontal field of view, making it ideal for seamless runway protection. This comprehensive view is supplemented by various high-resolution zooms in all image areas. The results are smooth processes and reduced infrastructure costs. Remote tower Regional airports, in particular, are struggling with limited budgets and staff shortages Regional airports, in particular, are struggling with limited budgets and staff shortages. One possible solution is the remote tower, developed by Dallmeier in collaboration with its technology partner TRIAC. This allows air traffic controllers to oversee flight operations remotely at multiple regional airports from a central location. Integrating Panomera technology and extended video analysis functions, such as automated aircraft tracking and displaying flight data directly in the video stream, improves the situational awareness of air traffic controllers and mitigates runway incursions. Optimised passenger flow Dallmeier’s Panomera multifocal sensor technology provides high-resolution video images It is becoming increasingly important for airport management to enhance the passenger experience and minimise the time spent on check-in, security checks, and passport control. Dallmeier’s Panomera multifocal sensor technology provides high-resolution video images and valuable metadata such as the number of people, waiting time data, and information on crowds. This information enables precise real-time analysis and control of passenger flow and provides airport management with a sound basis for optimising processes. The result: shorter waiting times, increased passenger satisfaction, and more efficient operations across all departments. Greater efficiency With a clear focus on holistic security and process solutions, Dallmeier will demonstrate at Inter Airport Europe how intelligent video surveillance, supplemented by radar technology, can contribute to effective security and increased efficiency in airport operations. “Our solutions enable airport operators to recognise security risks at an early stage, respond appropriately and significantly improve operational efficiency,” explains Karlheinz Biersack, Director Business Development Airport at Dallmeier.


Expert commentary
In today’s fast-evolving aviation landscape, innovation isn’t optional — it’s essential. With passenger traffic in the Asia-Pacific continuing to surge, the region is facing a pivotal moment: adapt with scalable tech, or fall behind. In January 2025 alone, APAC carriers accounted for 56.6% of global passenger traffic growth. Airports are operating at near capacity, with a record-high Passenger Load Factor (PLF) of 82.1%, leading to pronounced congestion at check-in counters, security checkpoints, and boarding gates. Increasing passenger volumes As airports strive to manage increasing passenger volumes without resorting to costly and time-consuming infrastructure expansions, technology — particularly facial recognition and biometric automation — emerges as a viable solution. However, the full realisation of these innovations requires more than just installing new system However, the full realisation of these innovations requires more than just installing new systems. It’s about building the right ecosystem of partners, processes, and policies to ensure sustainable, secure, and scalable growth. Presenting physical documents According to their estimates, over 120 APAC airports have already deployed biometric solutions at key travel touchpoints, including check-in, bag drop, security, and boarding. Thailand exemplifies this shift, with facial recognition deployed at six major airports — Suvarnabhumi, Don Mueang, Chiang Mai, Chiang Rai, Phuket, and Hat Yai — dramatically reducing passenger processing times. These systems allow travelers to verify their identities seamlessly at multiple touchpoints, from check-in and security screening to boarding gates, without presenting physical documents. This case reflects the Airports of Thailand’s (AOT) commitment to leveraging technology to improve operational efficiency and passenger experience. Digital identity programs Biometric solutions also extend beyond the airport: digital identity programs enable travelers to verify their identities before arriving at the terminal, creating seamless journeys from curb to gate. In this environment, facial recognition is not merely a futuristic innovation; it has become an operational imperative. Airports that fail to adapt risk falling behind, unable to manage burgeoning passenger volumes or meet evolving traveller expectations. True operational efficiency Despite its transformative potential, biometric technology cannot be successfully deployed in isolation. Achieving true operational efficiency through facial recognition requires strategic collaboration among technology vendors, IT integrators, airports, airlines, and regulatory authorities. Several pillars underpin a successful biometric implementation: Interoperability: Biometric systems must integrate seamlessly with a wide array of airline platforms, security protocols, and airport infrastructure. Lack of interoperability can lead to fragmented systems that frustrate staff and passengers alike. Scalability: Passenger volumes are forecasted to continue rising. Biometric solutions must be designed to scale rapidly in response to demand surges and future security challenges. Data Privacy and Security: With growing public scrutiny over personal data usage, airports must implement robust security frameworks that prioritise privacy and transparency. Encryption, consent-based use, and strict access controls are critical to gaining and retaining passenger trust. Future security challenges BKI can achieve significant throughput gains without major construction disruptions A case study illustrates these points: Malaysia’s planned revamp of Kota Kinabalu International Airport (BKI) aims to boost capacity by 33% over the next few years. Rather than expanding physical infrastructure alone, authorities are exploring facial recognition solutions to increase efficiency within existing spaces. By integrating biometric checkpoints at key touchpoints, BKI can achieve significant throughput gains without major construction disruptions. Such outcomes are only possible through well-coordinated technology partnerships, where vendors, airports, and integrators work toward a shared vision of future-ready travel. AI-powered computer vision What’s Next: Fully Biometric-Enabled Travel Looking ahead, the pressure on APAC airports is set to intensify. Airports Council International projects 9.5 billion air travelers globally by the end of 2025, a volume traditional processing methods cannot manage effectively. In response, AI-powered computer vision and facial recognition will continue to refine biometric processes, delivering higher accuracy rates and faster verification. Future systems will leverage real-time liveness detection, predictive analytics for crowd management, and seamless integrations across all travel stages. A fully biometric-enabled journey is becoming reality: Check-in with a glance at a kiosk Drop bags without producing an ID or boarding pass Clear security with automated facial recognition portals Board flights through biometric-enabled gates — without ever presenting a physical document. Experiencing significant growth Seamless integration across touchpoints creates a unified, frictionless journey In this vision of the future, identity becomes the ticket. Seamless integration across touchpoints creates a unified, frictionless journey. For APAC airports experiencing significant growth, full biometric enablement is becoming increasingly important for maintaining efficiency and staying competitive. At the same time, such a future demands robust technology ecosystems, where ongoing innovation is supported by partnerships that align regulatory, operational, and technological goals. Expanding physical infrastructure Building the Smart Airports of Tomorrow: Join the Conversation The aviation sector in APAC stands at a critical crossroads. Passenger growth, operational challenges, and heightened security requirements are converging, creating an urgent need for innovation. Facial recognition and biometric automation offer a clear path forward, enabling airports to handle growing volumes, enhance security, and deliver superior passenger experiences without necessarily expanding physical infrastructure. Facial recognition solutions Yet, the success of these innovations hinges on strategic, trusted technology partnerships. Airports must collaborate with technology vendors, IT system integrators, airlines, and regulators to ensure interoperability, scalability, and data security. At RecFaces, they believe the future of APAC airports is fully biometric-enabled. To explore how tech collaborations and advanced facial recognition solutions can transform airport operations, they invite users to join their free online panel discussion on April 30: ‘Smart Airports Start With Smart Tech: Facial Biometrics for APAC Airports.’
In today's rapidly evolving security landscape, facial recognition has become a buzzword that often triggers privacy and data protection concerns. However, many security professionals may not realise that "facial recognition" is an umbrella term encompassing various technologies, each with distinct applications and privacy implications. Let's dive into what these technologies really mean for security system resellers, integrators, and end-users. Facial recognition tech At its core, facial recognition technology re-identifies or verifies individuals based on their facial features, which are used as biometrics. However, not all biometric systems are based on unique identifying features. Some analyse general characteristics like facial hair style or other distinctive marks. Such traits, known as soft biometrics, can aid in identification but aren't unique enough to verify someone's identity uniquely. Personally identifiable information Modern systems incorporate robust safeguards, including data encryption and strict retention policies While facial recognition technology has applications ranging from access control to crime prevention to investigation, its implementation varies widely depending on specific needs. Modern systems incorporate robust safeguards, including data encryption and strict retention policies, to ensure the responsible handling of any personally identifiable information (PII). Understanding key technologies and applications Facial recognition encompasses several distinct technologies, each serving specific purposes. Here's a comprehensive breakdown of these technologies and their real-world applications. Key technologies: Face Verification (1:1): A one-to-one comparison where a person claims an identity (e.g., by showing an ID card), and the system verifies whether the face matches the provided identity. Example: In airports, face verification is used for automated passport control. When a traveler approaches a gate, their face is scanned and compared to the photo stored in the government database. If the face matches, the traveler is allowed through the gate without manual checks. Face Identification (1 to many): A one-to-many comparison, where a face captured by a system is compared to a database of multiple faces and facial features to identify the person. This process is often used in security or surveillance contexts. Example: In the case of a missing child at an airport, a system could scan the faces of all passengers passing through checkpoints and compare them to a photo of the child in a database. If a match is found, it triggers an alert. Face Re-identification (Many to Many): Many-to-many comparisons where multiple faces are compared to multiple other faces. This is typically used to track a person’s movement anonymously across different areas by matching their facial images at different checkpoints, without knowing their identity. Example: In a retail environment, facial re-identification might be used to track how long an anonymous person spends moving from one section of a store to another by re-identifying their face as they enter and leave different camera views. Facial recognition can be used both for real-time and offline applications. Real-Time Facial Recognition: Real-time facial recognition refers to the immediate processing of a live video feed, comparing faces to a database to generate instant alerts when a match is found. Example: At large public events like sports stadiums, real-time facial recognition might be used to detect banned individuals (e.g., known hooligans) as they attempt to enter. Post-Event (Recorded) Facial Recognition: This refers to analysing video recordings after the event has occurred, rather than in real-time. Facial recognition is applied to recorded data to identify or track individuals. Example: After a crime, investigators could use facial recognition software on recorded video from security cameras to identify suspects by matching their faces to known databases. These definitions cover various aspects of facial recognition technology, its different applications, and how biometrics are used for identification and tracking purposes. Biometrics: Biometric technologies use a person’s distinguishing physical characteristics, such as their face, fingerprint, or iris, to identify them. Example: Fingerprint or face scanning for unlocking a phone or using iris recognition for secure entry at high-security buildings like data centers. Hard Biometrics: Hard biometrics refer to physical characteristics that are sufficiently unique enough to be used for identifying a specific individual, such as a face, fingerprint, or iris. Example: Using iris recognition at airport security checkpoints to confirm the identity of a traveler. Soft Biometrics: Soft biometrics (personal features) include general attributes like height or body shape, which are not unique enough to identify a person on their own but can help narrow down re-identification when combined with other information. Example: Using height and body shape to help identify a suspect in a camera scene when facial features alone are unreliable. Appearance Similarity: This refers to distinguishing between people based on their appearance (e.g., clothing, accessories) rather than biometric features. It’s often used for accelerated investigation and statistical analysis rather than identification. Example: A retail store may track customers based on the clothes they are wearing to monitor how long they stay in the store, without tracking their faces or personal details. Liveness Detection: A method used to determine whether the subject in front of a facial recognition system is a live human being and not a photo or a video recording. Example: In some mobile payment systems, facial recognition requires users to blink or move their head slightly to ensure they are a live person and not someone trying to use a photo for authentication. Mathematical Representation: Non-reversible mathematical representations are lists of numbers based on a person's facial image or appearance based on clothing. These numbers represent characteristics but cannot be easily used to recreate the face. Example: When an organisation stores only the mathematical representations from a face rather than an actual image, even if the data is stolen, it is nearly impossible to recreate the person’s face or use the data with another system. Privacy and security considerations Modern facial recognition systems prioritise privacy through various protective measures, moving far beyond the basic security protocols of the past. Solutions integrate multiple layers of protection designed to safeguard personal data while maintaining system effectiveness. These sophisticated privacy controls work in concert to ensure responsible data handling and comply with evolving security standards. Key protective measures include: Biometric template isolation that keeps facial recognition templates separate from other personal data, with dedicated secure storage environments. Template encryption frameworks specifically designed for biometric data, using industry-standard protocols that protect facial features during both processing and storage. Biometric data anonymisation that converts facial features into non-reversible mathematical representations – into numbers - prevents the reconstruction of original face images. Cascading deletion protocols automatically remove both raw facial data and derived biometric templates after their authorised use period. Segmented access controls that separate facial recognition administrative functions (like enrollment and template management) from regular system operation. Privacy standards The key is selecting the right tool for each application and ensuring that personal data is collected The security industry continues to evolve, finding innovative ways to balance effective surveillance with privacy protection. By understanding this comprehensive range of technologies, security professionals can better serve their clients with solutions that address specific needs while maintaining appropriate privacy standards. The key is selecting the right tool for each application and ensuring that personal data is collected only when necessary and protected when it is not. Statistical analysis and pattern recognition The variety of facial recognition applications demonstrates that not all systems require storing personal information. Many modern solutions focus on statistical analysis and pattern recognition rather than individual identification, offering powerful security benefits while respecting privacy concerns. This balance of capability and responsibility represents the future of video security technology.
The average business owner or investor has some kind of security precaution in place, especially in the after-hours when there are fewer deterrents to inhibit criminal activity. Security guards, video surveillance systems, motion sensor lights, or even just fake cameras placed around the property are some of the common options people choose. Future of overnight security Smart business owners are starting to realise, however, that some of these traditional security measures are becoming antiquated and no longer cutting. The now and future of overnight security is in remote guarding. Pioneered by companies like Los Angeles-based Elite Interactive Solutions, which was founded back in 2007, remote guarding is revolutionising the overnight security business. Minimising criminal activity Remote guarding is fast becoming the most popular choice among commercial end-user property owners Remote guarding utilises a combination of cutting-edge technology, “digital guards,” highly trained security agents, and local law enforcement if and when necessary to minimise the potential of criminal activity. For those adequately enlightened to its overwhelmingly impressive crime prevention capabilities, remote guarding is fast becoming the most popular choice among commercial end-user property owners to secure and protect their investments. What Is remote guarding? Remote guarding is a revolutionary concept and increasing trend in security systems that utilises a combination of methods to effectively analyse potential threats to property. Cameras and/or other monitoring devices running highly advanced algorithmic software are installed in strategic areas or vulnerable places onsite and remotely located security agents are immediately notified of any activity within a designated perimeter of the property. A blend of AI, cybersecurity, and video analytics When properly deployed by an expert provider, the technology stack includes a proprietary blend of video analytics, artificial intelligence, cybersecurity, and more. Done right, “noise” is effectively filtered out, allowing agents to act on legitimate alerts and achieve zero false alarms communicated to first responders. Today, there are a lot of terms and descriptions tossed around about remote guarding, remote video, virtual guarding, etc., but those attributes must be present to represent the true definition of the offering and its many virtues. Realtime situational awareness Many systems have a two-way speaker that allows the security agent to give a verbal warning When specially trained security agents are alerted to trespassers, possible intruders, or other suspicious activity, they analyse the situation in real-time and determine the necessary level of action. Many systems have a two-way speaker that allows the security agent to give a verbal warning, known as a voice-down, to the individual(s) that they are being watched. Most perpetrators, often believing the response is emanating directly from security personnel on the property itself rather than from a remote command centre, flee immediately. However, if the threat persists, the security agent enlists local law enforcement to get on the scene. Customised remote guarding When properly deployed, remote guarding systems are also customised to specific properties. A team of consultants visits the client’s property to evaluate its vulnerabilities and where to best place cameras and/or other monitoring devices for system efficacy. Traditional security shortfalls According to Keith Bushey, a retired commander for the Los Angeles Police Department, there is much frustration between law enforcement officers and potential victims of crime due to the historically unreliable performance of traditional burglar alarm systems and central monitoring stations. He states about 90% of security-related calls are false alarms, a problem that has been well-documented through the years. Onsite challenges When a legitimate emergency does occur, the perpetrators have often already done their damage When a legitimate emergency does occur, the perpetrators have often already done their damage and/or escaped by the time law enforcement arrives. Onsite security guards are not the remedy either as they bring their own set of issues and challenges. Unexpected costs Traditional security systems can also have unexpected costs. The cost is not only in the security guards’ paycheck or the cost of the equipment itself. The cost comes when an actual incident occurs. In worst-case scenarios, the security guard(s) are injured, the business suffers inventory loss, and/or damage is sustained to the property. The medical and other costs for the security guard(s), the loss of inventory, property damage, deployment of law enforcement resources, and possible fallout of legal expenses all add up. Even in the best-case scenario, false alarm expenses incur if law enforcement is dispatched. These, among many others, are some of the primary issues that remote guarding resoundingly answers as a superior alternative. A bounty of benefits Remote guarding systems have been proven to cut costs and be more effective than traditional security systems. Even though the monthly monitoring costs of remote guarding are significantly higher than traditional intrusion detection system monitoring, the much higher effectiveness in crime reduction, elimination of false alarms, and augmenting or replacement of manned guards result in a substantially higher return on investment (ROI) to the end user. Easy tracking of threats The security cameras already have their image captured on record, making them easier to track down For example, case studies have demonstrated reduced security costs for clients by 60%, on average. These reductions have come from the costs of security staff, inventory, or property loss, plus saving money on insurance premiums and deductibles. The nature of remote guarding reduces the risk and costs of false alarms, with professional security agents able to determine an actual threat before law enforcement is called. In a rare instance when a perpetrator escapes before law enforcement arrives or can detain the individual(s), the security cameras already have their image captured on record, making them easier to track down and identify. Reduction of false alarms The significant reduction in false alarms is greatly appreciated by law enforcement, as it allows them to focus on real emergencies or crises. Better relationships are also developed between clients and law enforcement, as remote guarding systems are highly reliable in providing accurate and real-time information to officers as they approach the scene. In short, it assists law enforcement in doing their job more effectively, as well as more safely thanks to having eyewitness information before engaging in an active crime scene. Partnership When you combine the decreased cost with the increased efficiency and success rate, it is easy to see why many commercial end-user property owners across the country are making the shift to remote guarding. It’s also an outstanding opportunity for professional security dealers and integrators to partner with a remote guarding services provider to bring a superior solution to their end customers and pick up a recurring monthly revenue stream in the process.
Security beat
Companies at GSX 2023 emphasised new ways that technologies such as artificial intelligence (AI) and the cloud can address long-standing issues in the security market. Among the exhibitors at the event in Dallas were companies seeking creative ways to apply technology, lower costs, and make the world a safer place. Reflecting on the exhibition, here are some additional takeaways. Expanding AI at the edge i-PRO is a company reflecting the continued expansion of edge AI capability in the security market. Today, more than half of the company’s lineup supports AI at the edge so the customer has a wide choice of form factors when seeking to leverage the feature set. AI processing relay, extended warranty i-PRO is increasing their warranty period from 5 to 7 years, which could be a lifetime warranty in some cases I-PRO also has an “AI processing relay” device that accepts non-AI video streams and applies edge analytics. AI has progressed from a high-end technology to a feature available in a variety of cameras at different price points. i-PRO is also increasing its warranty period from 5 to 7 years, which could be a lifetime warranty in some cases depending on a customer’s refresh schedule and lifecycle management. Active Guard, MonitorCast The company’s video management system (Video Insight) is continuing to build new features including “Active Guard,” an integrated metadata sorter. Their access control platform, MonitorCast, is a Mercury-based solution that is tightly integrated with Video Insight. Their embedded recorders now have PoE built in. “We can move at a faster pace to fill out our product line since leaving Panasonic,” says Adam Lowenstein, Director of Product Management. “We can focus our business on adapting to the market.” Emphasis on retail and other verticals Shoplifting is a timely issue, and retail is a vertical market that got a lot of attention at GSX 2023. “We see a lot of retailers who are primarily interested in protecting employee safety, but also assets,” says Brandon Davito, Verkada’s SVP of Product and Operations. “Shrinkage is a CEO-level priority.” “Retailers are getting more engaged with security posture, instead of letting perpetrators walk,” Davito adds. Intrusion detection Verkada has an intrusion product that will notify a central station if there is an alarm On the alarm side, Verkada has an intrusion product that will notify a central station if there is an alarm, and operators can review videos to confirm the alarm. Other capabilities seeking to discourage trespassers include sirens, strobes, and “talkdown” capabilities. International expansion Verkada continues to expand internationally with 16 offices in all, including Sydney, Tokyo, and London. The core value proposition is to enable customers to manage their onsite infrastructure more simply, including new elements such as PTZ cameras, intercoms, and visitor management. Verkada emphasises ease of use, including a mobile application to allow access to be managed across the user base. Forging partnerships “We are committed to the channel and industry, and we continue to build relationships and expand our reach,” says Davito. Among the industry relationships is a new partnership with Convergint, which was hinted at during the show and announced later the same day. They are also expanding their partnerships with Schlage, Allegion, and ASSA ABLOY. Working with other verticals They offer new features for K -12 schools, and a new alarm platform is easier to deploy and manage Verkada has also found success across multiple other verticals, notably healthcare, where they integrate with an electronic medical records system. They offer new features for K-12 schools, and a new alarm platform is easier to deploy and manage. They are integrating wireless locks to secure interior doors in schools, looking to secure the perimeter, and installing guest management systems. Transitioning the mid-market to the cloud Salient is squarely focused on the “mid-market,” a large swath of systems somewhere between small businesses and enterprise-level systems. Pure cloud systems are not as attractive to this market, which has a built-out infrastructure of on-premise systems. Adding a camera to an existing system is easier and less expensive than tying it to the cloud. Benefits of cloud It’s a market that may not be ready for the pure cloud, but there are benefits to be realised from adding a cloud element to existing systems. “We are continuing to augment our premise-based solutions with added cloud capabilities and flexibility,” says Sanjay Challa, Salient’s Chief Product Officer. The feedback Salient hears from their customers is “I want to own my data.” The hybrid cloud approach offers the right mix of control, flexibility, and unit economics. Cloud add-on capabilities We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive" Cloud add-on capabilities include bringing more intelligence about system operation to the user via the cloud. Over time, Salient expects to sell more cloud-centric offerings based on feedback from integrators and customers. “We want to provide the flexibility for customers to go full-cloud as it becomes more economically attractive over time,” says Challa. Vaidio AI technology Salient seeks to be a transition pioneer to help customers realise the path to the cloud. Their approach is “crawl, walk, run,” and helping customers make the transition at each stage. Salient has added AI to its product offering, incorporating Vaidio AI technology from IronYun into a powerful suite and broad array of on-premise analytics, which are gaining traction. The seamless approach makes it easy for customers to embrace AI analytics, although Salient remains broadly committed to open systems. Addressing ‘soft’ features for integrators AMAG is in the process of enhancing its product line with the next generation of access control panels. However, “product” is just part of the new developments at AMAG. In addition to “hard” features (such as products), the company is looking to improve its “soft” features, too; that is, how they work with the integrator channel. Integrator channel Rebuilding a process to make your organisation more efficient, is relatively easy; it just takes a lot of persistence" “We have the depth of our legacy customer base we can learn from, we just need to close the feedback loop quicker,” says Kyle Gordon, AMAG’s Executive Vice President of Global Sales, Marketing, and commercial Excellence, who acknowledges the value of reinstating face-to-face meetings after COVID. “We are laser-focused on nurturing our integrator channel,” he says. “Developing new features takes time, but rebuilding a process to make your organisation more efficient, that’s relatively easy; it just takes a lot of persistence,” says Gordon. More cohesive internal communication is another useful tool, he says. Disrupting the cloud based on price Wasabi is working to make cloud applications less expensive by offering a “disruptive” price on cloud storage, $6.99 per terabyte per month (80% less than hyperscalers). Contending “hyperscalers” like AWS are charging too much for cloud storage, Wasabi is using its own intellectual property and server equipment co-located in data centres around the world. Wasabi sells “hot cloud storage,” which refers to the fact that they only have one tier of storage and data is always accessible. In contrast, a company such as AWS might charge an “egress fee” for access to data stored in a “colder” tier. Cloud storage “We saw that several video surveillance companies had not yet adopted cloud storage, and we saw an opportunity to make it easy to use,” said Drew Schlussel, Wasabi’s Senior Director of Product Marketing. “We just install a little bit of software that allows them to store data in the cloud and bring it back from the cloud.” Performance, protection (cybersecurity), and price Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies Wasabi works with integrators, resellers, and distributors and also integrates with VMS companies such as Genetec and Milestone. Emphasising performance, protection (cybersecurity), and price, their data centres are certified to SOC 2 and ISO 27001 standards. Faster throughput for weapons detection Xtract One is a young company focusing on weapons detection in a time of accelerated concern about gun issues post-COVID. Founded in Canada and based on technology developed at McMaster University, Xtract One has found a niche in providing weapons detection at stadiums and arenas. These customers already have budgets, and it is easy to shift the money to a newer, faster technology. Madison Square Garden in New York City is among its customers. Cost savings solution Xtract One can increase throughput to 30 to 50 people per entrance per minute (compared to 5 to 6 people per minute when using metal detectors). The solution doesn’t require anyone to empty their pockets and the system alarms on items beyond guns and knives. Using Xtract One allows customers to reduce the number of screening lanes and security staff, providing additional cost savings, all while getting fans through the screening process in half the time. Purpose-built sensors The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties In addition to stadiums and arenas, Xtract One, formerly Patriot One, is also getting “inbound” interest from schools, hospitals, manufacturers, and other verticals that makeup 50% of their business. “We’re on a rocket ride, mainly because the weapons issues are not going away,” says Peter Evans, CEO and Director at Xtract One. The system uses purpose-built sensors looking for specific characteristics, such as reflective and density properties, all correlated by an AI engine. Providing early warning of violence ZeroEyes is another company focused on weapons detection. Their AI gun detection system works with video images to identify if someone is “brandishing” (carrying) a weapon. In other words, the system does not detect concealed weapons. Identifying someone carrying a weapon provides early warning of a possible violent act. Increased response with AI-enables images Images are identified by AI and sent to a monitoring centre where a human confirms the image before contacting first responders. Knowing the location of a shooter enables staff to lock entry points, move people to safety, and direct first responders. The company was founded to leverage existing camera views to stop mass shootings and gun violence by reducing response times.
Audio-video technologies have historically been a silo in the enterprise, separated from the larger network infrastructure by their use of analogue, hard-wired and proprietary connections. Software-defined system However, AV devices such as video walls and corporate signage add more value to security and emergency response operations when they are connected to the larger IT network and can interface seamlessly with other systems. That’s the approach provided by Userful, which offers a software-defined system for end-to-end control of audio-video applications in an enterprise, using a web browser and standard industry protocols. The use of software avoids the need for proprietary hardware and the compatibility challenges of multiple hardware systems operating in silos. It also yields visibility and control throughout the system. Single software system The single software system grants IT, administrators, the ability to govern multiple platforms The single software system grants IT, administrators, the ability to govern multiple platforms, while providing individual departments access to the specific applications they need. The emphasis is on meeting stakeholders’ functional requirements using a system governed by the IT department. The data travels across the IT network infrastructure without being blocked by the use of proprietary hardware and cabling, for example. Digital transformation Avoiding the analogue (hardwired) approach enables enterprises to “digitally transform” the operation of their audio-video devices. The approach is especially useful at the intersection of security and digital signage. “We give the power back to the local IT administrators, who can govern the system and enable customers to govern their applications,” says Shane Vega, VP of Product Marketing at Userful. The company’s software aggregates video information and distributes it as needed to individual video displays. Real-time event monitoring The software enables various video devices to become a seamless part of the IT infrastructure. It also facilitates sharing of information throughout the enterprise, even in an emergency. In contrast, proprietary, siloed systems hamper the free flow of information when it is needed the most. For example, if there is an emergency or active shooter situation, video devices throughout an organisation can be leveraged to inform occupants about the details of the event in real-time and to provide actionable instructions specific to an occupant’s location in the building. Visual communications When security is integrated into a larger platform, it can spread the message visually throughout the enterprise Visual communications, such as digital signage, comprise a powerful extension of a security system that actively monitors threats, and offers the ability to communicate to a large group of people. When security is integrated into a larger platform, it can spread the message visually throughout the enterprise. Strategic messaging can guide building occupants to their best course of action during an emergency, whether it is to flee or to shelter in place. Situational awareness The software-driven IT system can aggregate information from multiple sources, such as video camera feeds or information from an access control system, and display it on a large video wall, for example. Free-flowing information promotes situational awareness in a control room, and enables immediate response, whether it’s to call the fire department, sound an alarm, or initiate a mass exodus of building occupants. IT software approach “It makes everyone strategically aware and sends the appropriate messaging to those who need it, rather than to everyone at once,” says Vega. Facilitating more effective operations centers is the “tip of the spear” of what Userful offers customers, he adds. The IT software approach simplifies video wall applications, which are becoming increasingly complex, by enabling content to be scaled, chopped, and aggregated to fit the demands of a display wall. An analytic might trigger the system to enlarge a camera view on the full screen, to send video to the police, or “take over” screens throughout a building to provide strategic messaging. Third-party integrations Designing video walls more strategically in an operations centre can help operators interpret information quickly Designing video walls more strategically in an operations centre can help operators avoid fatigue and interpret information quickly and efficiently. “Userful’s role in the display world is to make sure software can distribute the information despite the hardware,” said Vega. Userful works with third-party integration to add system functionality and automate responses. Software flexibility “We’re a platform that pulls in sources of information, maybe it’s a hundred cameras, and then we manage the entire solution,” says Vega. “We enable users to take data from multiple sources and send it to a wide range of displays, creating a repository of information.” “When you have a software-defined platform, you can extend the solution using the flexibility of the software into a system that cannot be achieved with hardware,” says Vega. “If people want to scale their system to multiple locations, we can add a source remotely.” Proactive responses to security “Security is an important market for everyone, paramount for any organisation,” says Vega. “Individuals are responsible for the safety and security of constituents and require a proactive, not reactive response.” “We can provide proactive responses because of the nature of AV-over-IP, which is interoperability. It can draw attention to threats and proactively communicate response plans.” Managed service provider The “software-defined” approach can help systems integrators position themselves as a managed service provider Getting away from siloed solutions should be a priority for any IT purchase by an organisation, says Vega. “We need to train end-users to take a holistic view and not to look at it from a siloed perspective. A fuller understanding helps them gain efficiencies.” The “software-defined” approach can help systems integrators position themselves as a managed service provider rather than just “selling boxes.” “Think about how you can partner with end-users over the long term,” advises Vega. Information-based automation “Think of technology as a holistic part of the business for better outcomes across the whole business. More information is better information, and integrators can help customers create automation that will provide more awareness.” The Userful proposition offers especially good value in transportation markets, such as ports and airports; and in campus environments, such as enterprise, higher education, and airports. In any scenario where there are a lot of screens, the system can distribute corporate and emergency messaging, whether on a baggage claim screen or a way-finder screen.
Travel volumes at airports have been increasing of late, although still below the 2.5 million or so passengers the Transportation Security Administration (TSA) screened every day, on average, before the pandemic. As passengers return, they will notice the airport security experience has changed during the pandemic – and many of the changes are likely to continue even longer. Need for touchless technology The lowest U.S. air travel volume in history was recorded last April, with approximately 87,500 passengers. As passenger traffic plummeted, the aviation community sought to explore the potential of new technologies to make security checkpoints more contactless and flexible when the traffic numbers return. The pandemic has seen an increase in touchless technology deployed in the screening area. Used for cabin baggage screening, Computed Tomography (CT) produces high-quality, 3-D images to enable a more thorough analysis of a bag’s contents. Imaging Technology Millimeter-wave body scanners began replacing metal detectors globally as a primary screening method Enhanced Advanced Imaging Technology (eAIT), which uses non-ionising radio-frequency energy in the millimeter spectrum, safely screens passengers without physical contact for threats such as weapons and explosives, which may be hidden under a passenger’s clothing. Millimeter-wave body scanners began replacing metal detectors globally as a primary screening method. AI algorithms Other innovations include an automatic screening lane, centralised image processing, and artificial intelligence (AI). Looking ahead, AI algorithms have the ability to clear most passengers and bags automatically, making the process smoother and freeing up staff to focus only on alarms. The pandemic’s need for contactless screening may accelerate the adoption of AI. CAT machine Credential Authentication Technology (CAT) machines automatically verify identification documents presented by passengers during the screening process. The TSA continues to accept expired Driver’s Licenses and state-issued IDs for up to a year after expiration, based on the premise that license renewals may be delayed and/or more difficult during the pandemic. The REAL ID enforcement deadline was extended to Oct. 1, 2021. Health precautions Checkpoint health precautions have been a part of the airport screening experience since early in the pandemic. Last summer, the TSA announced the “Stay Healthy. Stay Secure” campaign, which included requirements such as social distancing among travelers, ID verification without physical contact, plastic shielding installed at various locations, and increased cleaning and disinfecting. In January 2021, President Biden signed an Executive Order requiring travellers to wear face masks when in airports and other transportation facilities (to remain in effect until May 11). Checkpoint screening Clear is a privately owned company that provides expedited security that uses biometrics either a person’s eyes or face to speed along the process of getting people through checkpoints. TSA officers wear masks and gloves at checkpoints and may also wear eye protection or clear plastic face shields. The limits on allowable liquids a passenger may take on board were broadened to include a hand sanitiser container of up to 12 ounces, one per passenger in a carry-on bag. A paradigm shift Just as aviation security changed after 9/11, the COVID-19 crisis is expected to lead to a paradigm shift to create a safer and more secure environment. Measures were implemented so that passengers, staff and other stakeholders could have continued assurance and confidence in airports amid and after the pandemic.
Case studies
Xtract One Technologies announced its SmartGateway has been selected by Nova Scotia Health to strengthen security measures and provide AI-powered weapons detection across facilities province-wide, with an initial order of 25 systems. Nova Scotia Health, in tandem with its nurses’ union, is working to modernise and strengthen security across its facilities to ensure a safe environment for all patients, visitors, and staff. Adopting and deploying advanced technologies like SmartGateway is an important step toward achieving that goal. Safe and secure health care By helping to limit the number of potentially dangerous items entering their hospitals, this technology supports its commitment to providing safe and secure health care. Xtract One was selected for its proven efficacy to accurately detect knives, a top priority for the organisation. Previously tested in Truro, Nova Scotia, over a 12-day trial period, SmartGateway successfully scanned 7,400 individuals entering the facility and detected 49 prohibited items during that period, mostly pocket knives and box cutters. Deploying SmartGateway “Violence against healthcare workers is a challenge that persists and demands addressing. By deploying SmartGateway, Nova Scotia Health is setting an important example for what it means to take meaningful action to protect frontline healthcare workers, patients, and visitors,” said Peter Evans, CEO of Xtract One. “This installation marks another key step in our expanding work with Canadian healthcare organisations, having deployed in Manitoba earlier this year. We look forward to continuing to deliver effective threat detection as more providers take proactive measures to prioritise security and peace of mind for their teams.” Overall approach to security “Our goal is to deliver first class healthcare, and ensuring the safety of all who enter our facilities is a critical step in providing that service,” said Dean Stienburg, Director of Security for Nova Scotia Health. “With SmartGateway, we’re making tangible strides in bolstering our overall approach to security. We were impressed by the system’s effectiveness during the trial period and are looking forward to the deployment helping us mitigate and respond to the threats of today’s environment.” Maximising security screening outcomes SmartGateway delivers fast, discreet, and accurate individual screening, utilising AI-powered sensors to unobtrusively scan for weapons and other prohibited items upon entry. This technology replaces intimidating, traditional metal detectors and mitigates the need for individuals to remove personal items. This prioritises individual privacy and comfort, all while maximising security screening outcomes. SmartGateway is designed to enable seamless passage through checkpoints and promote the uninterrupted flow of movement.
ATÜ Duty Free, Turkey’s pioneering duty-free retailer, aimed to establish a comprehensive security and AI-powered surveillance system in the Antalya Airport new terminal building project to maximise operational efficiency and customer experience. This critical project was successfully implemented thanks to Hanwha Vision’s high-performance camera solutions and deep learning-based AI capabilities, combined with the flawless implementation by integrator Arte Teknoloji. This project, utilising over 1,450 cameras, serves as a model for modern retail security and business intelligence applications. ATÜ Duty Free ATÜ Duty Free is one of Turkey’s and the world’s pioneering players in international standard duty-free retail. Operating in major Turkish airports such as Istanbul, Ankara, Izmir, and Antalya, as well as abroad, ATÜ is committed to providing travellers with a luxurious and enjoyable shopping experience. Due to its wide product range, high customer traffic, and sensitive duty-paid/duty-free sales processes, security systems are not only a means of protection for ATÜ but also a critical resource for business intelligence and operational management. Arte Technology A pioneer in the electronic security systems sector since 2006, Arte Technology is an integrator company specialising in low-voltage systems that has delivered hundreds of successful projects. Arte Technology offers its customers comprehensive services, from sales to after-sales support, in line with international standards and local regulations, providing solutions from global brands such as Hanwha Vision. Project objectives and challenges The new terminal building at Antalya Airport, with its high passenger traffic and extensive and complex store layout, required the following objectives: Advanced security: Prevention of in-store theft, inventory losses, and security breaches in critical areas. Operational efficiency: Effective management of customer flow, congestion levels, and checkout processes in the retail area. Business intelligence: Collecting data to analyse customer behaviour, optimise in-store layouts, and increase sales. Integration and management: Seamless and reliable management of over 1,450 cameras and analytical data through a centralised VMS (Video Management System). Hanwha Vision’s solution The backbone of the project consists of Hanwha Vision cameras, chosen for their reliability and high image quality. A total of 1,450 cameras have been deployed at the terminal’s most critical points: QNV-C6083R (Dome) – 1200 cameras for in-store areas, corridors, warehouses and customer tracking. QNO-C6083R (Bullet) – 250 cameras for exterior facades, entrances/exits, and critical surveillance points. AI applications: enhancing efficiency and customer experience Using Hanwha Vision’s camera and Genetec’s VMS integration, three critical AI analytics solutions tailored for ATÜ were implemented: People counting: By accurately measuring passenger density in different sections of the store and at the main entrances, working hours and staff distribution were optimised. Queue management at checkouts: Cameras installed in checkout areas detect queues forming and send alerts to staff to manage. Heatmap: Areas where customers spend the most time within the store are analysed visually. This data has become an indispensable business intelligence tool for optimising product placement (merchandising) and window displays. Software integration All camera and analytics data is consolidated on the industry-pioneering Genetec VMS platform. This powerful integration has provided ATÜ with the following capabilities: Centralised monitoring and recording management. Rapid visualisation and reporting of Hanwha Vision AI data within the VMS interface. Establishment of alert mechanisms for immediate response to incidents. Results and benefits Thanks to this comprehensive project, ATÜ Duty Free has achieved significant gains not only in security but also in operational excellence at Antalya Airport: Precise inventory control – High-resolution surveillance minimises the risk of theft and loss, particularly in areas containing luxury and duty-free goods. Enhanced customer experience – Queue Management has reduced waiting times, for improved customer satisfaction. Efficient staff deployment – The right number of staff were assigned during peak hours using people counting data. Store optimisation – Heatmap analytics highlight the most popular store areas, maximising sales potential. This case study demonstrates how Hanwha Vision’s reliable camera hardware, alongside distributor Entpa Elektronik A.Ş. and its Project Manager Eyüp Tetik, combined with Arte Technoloji’s integration expertise, provides the retail sector not only with video recording but also with actionable business intelligence that delivers value.
Gunnebo Entrance Control has partnered with Queenstown Airport (ZQN) and Custom Technology Systems Ltd to elevate the domestic departure experience, providing greater convenience and security for passengers. Queenstown Airport, a key gateway to New Zealand’s South Island and the country’s fourth-busiest airport, has evolved continuously since opening in 1935. Now serving more than 2.6 million passengers each year, it connects major domestic destinations and east coast Australia, driving ongoing improvements to passenger facilities and operational efficiency. Entrance control solution As part of a dedicated programme to enhance the domestic departures journey, ZQN reworked existing café space. A glass wall was installed to relocate the café airside, integrating it with the gate lounge. This provided direct food and beverage access for passengers and created additional seating, all within the same footprint. To support the new layout, Custom Technology Systems Ltd and Gunnebo Entrance Control worked closely with the on-site teams to deliver a tailored entrance control solution that balanced security and passenger flow whilst accommodating spatial limitations. Adapting to unexpected challenges “The success of this project was achieved by working together, adapting to unexpected challenges, and staying focused on delivering a secure, seamless journey for every passenger,” said Chris Walker, Project Manager at Queenstown Airport. “Every challenge we encountered was met together. Whether it was refining the design, resolving compliance issues, or adapting to the space, we relied on each other’s strengths to get it right.” Gunnebo Entrance Control’s PasSec solution To optimise style, security and passenger movement, the team installed Gunnebo Entrance Control’s PasSec solution, a sleek one-way corridor system designed to prevent backflow while maintaining compliance with strict local and international aviation regulations. Brett Copeland, Managing Director at Custom Technology Systems Ltd, added: “For this works programme, there was a genuine sense of problem-solving together. It wasn’t about one party leading and others following but instead a collaborative process from initial design and specification through to project completion. We each brought ideas, worked through constraints and stayed focused on making the solution fit.” Challenges together to deliver smarter Clive Dillen, Regional Manager at Gunnebo Entrance Control, concluded: “We’re proud of what we achieved here, and the result reflects the true essence of coordination, discussion and trust. That’s what true partnership looks like and marks a major step forward in Queenstown Airport’s continued development." "It stands as a clear example of what can be accomplished when organisations work through challenges together to deliver smarter, more effective outcomes for passengers and operators.”
Cognitec Systems Pty Ltd is working with Home Affairs Australia to deliver 250 camera devices for facial image capture, image quality check, and traveller identity verification at all major international airports in Australia. With approximately 41 million international travellers entering and leaving Australia each year, the Department uses facial biometrics to collect and electronically verify the identity of eligible international travellers. Cognitec hardware and software systems Cognitec’s capture device, FaceVACS-Entry, detects the person’s height, automatically adjusts the camera position to capture a frontal pose photo, and uses automated face recognition to verify person identity. Cognitec is also providing integration software, mounting hardware, device installation services, as well as ongoing support and maintenance services for all Cognitec hardware and software systems. Relationship with the Department of Home Affairs “Cognitec is proud to continue a successful relationship with the Department of Home Affairs, and to deliver our technology for quick collection of biometric photos and for accurate traveller verification at the Australian border primary lines,” says Terry Hartmann, Cognitec’s Vice President Asia Pacific, adding “This project contributes to the security and ongoing digitisation of the Australian border, ensuring trusted traveller identities.” FaceVACS-Entry is used by governments worldwide for applications that require the acquisition of standards-compliant photos, and the verification of a live image against reference images, such as access control, border control, and entry/exit programs.
Ecuador’s border control authorities have significantly enhanced their identity verification capabilities by deploying a suite of advanced document examination devices from Regula. The nationwide upgrade, supported by the International Organisation for Migration (IOM) and local partner INSETK, brings automation, precision, and speed to the country’s border checkpoints, which collectively process nearly 1.5 million travellers annually. Regula’s advanced forensic devices The project is a major step in Ecuador’s mission to modernise all land, air, and maritime entry points The project is a major step in Ecuador’s mission to modernise all land, air, and maritime entry points, including key international airports in Quito and Guayaquil, as well as northern and southern border crossings. These strategic locations now benefit from Regula’s advanced forensic devices, which enable fast and reliable detection of fraudulent documents—critical in the fight against identity-related crime. Closing the gap with a set of forensic devices Previously, document checks at Ecuador border crossings were largely manual and supported by outdated equipment, often handled by just two officers per site. This made the process slow, error-prone, and vulnerable to sophisticated fraud. To address this, Ecuador’s border checkpoints were equipped with the following Regula solutions: Regula 4308 at Quito International Airport: Ideal for high-traffic airports, this dual-video spectral comparator supports the full spectrum of light sources and optical filters. It also offers high-quality image capture capabilities thanks to its up to 320x optical zoom and up to 140,000 ppi resolution. As a result, border officers can thoroughly inspect all of the ID security features, including printing techniques, holograms, optically variable inks, and more. Regula 4306 at Guayaquil International Airport and major land borders: A space-saving device with an 8 MP high-resolution camera and over 40 LED light sources for analysing document authenticity, just like its counterpart, the Regula 4308. Regula 4205D at frontline checkpoints: A multi-functional device tailored for primary control zones. It includes 12 light sources, automated cross-checks, and up to 30x on-screen magnification for thorough document authentication. Regula 8333M at mobile checkpoints: Designed for remote or non-standard border control situations, such as processing charter flights or cruise ship passengers, this compact mobile document reader ensures that ID checks remain reliable and consistent outside traditional migration offices. Regula’s Information Reference System Regula’s video spectral comparators are controlled via Regula Forensic Studio (RFS), a cross-platform software solution for advanced document checks. It enables precise measurements, image comparison, report generation, and scripted workflows for faster, consistent inspections. With RFS, officers can also verify MRZs, RFID chips, barcodes, and IPI—all without extra tools. For deeper document examination, border control officers have real-time access to Regula’s Information Reference System (IRS), which provides synchronised reference images and lighting presets for fast, precise comparison of travel documents. Data cross-verification and robust authenticity checks RFS also integrates with Regula Document Reader SDK to automate travel document verification RFS also integrates with Regula Document Reader SDK to automate travel document verification and prevent fraud through data cross-verification and robust authenticity checks. Importantly, Regula’s software is backed by its proprietary identity document template database—the world’s largest—featuring over 15,000 templates from 252 countries and territories, ensuring reliable validation at border checkpoints. Trusted results, faster than ever Since implementing Regula’s solutions, Ecuadorian border control authorities have noticed notable improvements: Document authentication now takes minutes instead of hours. Detection of forged documents has significantly increased. Automation reduces human error and increases operational efficiency. Officers have more time to focus on complex cases and decision-making. Technology upgrade and fraud detection “Apart from the technology upgrade and fraud detection improvement at the border crossings, our collaboration with Regula demonstrated another success." "The project was fulfilled very smoothly. From the beginning, we’ve received full support from Regula’s team—they were always ready to help with any issue, even those caused by users on the ground. It’s definitely a level of service that makes a real difference,” says Diego Calderon, Chief Executive Officer at INSETK. How technology can turn critical inspection tasks “Border security is where precision, speed, and trust must converge. We're proud to support Ecuador in modernising its checkpoints with tools that meet forensic standards while being easy to use in the field." "This project shows how technology can turn critical inspection tasks from time-consuming to streamlined, without compromising security,” comments Arif Mamedov, CEO at Regula Forensics, Inc.
SightLogix, a pioneer in AI-powered thermal security for critical infrastructure environments, has announced that an undisclosed South Florida airport has completed a lifecycle refresh of SightSensor cameras, the core component of the airport’s advanced perimeter security infrastructure. The perimeter surveillance system from SightLogix leverages advanced thermal cameras with edged-based artificial intelligence capabilities to validate threats, minimising false alarms by over 90% and reducing monitoring resources, increasing operational efficiency. Durability of the SightSensor camera The durability of the SightSensor camera provides clients with a reliable and wide approach Cutting-edge SightSensors can detect intrusions at long distances, in complete darkness, and without false alarms—even in challenging Florida environmental conditions including heavy rain and extreme heat and humidity. The durability of the SightSensor camera provides customers with a reliable and comprehensive approach for intelligent airport perimeter monitoring. AI-driven thermal cameras “The SightLogix solution automates surveillance of the entire perimeter at the airport,” noted Dan Flynn, President of SRI, the system integrator. “The AI-driven thermal cameras provide consistent performance regardless of lighting or weather conditions, which is crucial for airport security, and the system integrates into the existing access control system to leverage previous investments.”


Round table discussion
Headlines of violence in our schools are a reminder of the need to keep educational institutions safe. In fact, if there is a positive aspect to the constant bombardment of headlines, it is that it keeps our attention perpetually focused on how to improve school security. But what is the role of physical security systems? As the new school year begins, we asked this week’s Expert Panel Roundtable: Are schools safer because of physical security systems? Why or why not?
As physical security technologies become more complex, it is incumbent on the dealer/integrator to have the skills and expertise needed to ensure that a system operates smoothly. The value of integrators increasingly rests on the skill sets they bring to bear when installing a system. If the skills are missing, there is a problem. We asked this week’s Expert Panel Roundtable: What missing skills among security integrators can cause problems for customers?
Driving the smart homes market is the convenience of simple technology solutions. Almost every home now has a “smart speaker” that makes it easier than ever for homeowners to interface and control their technology. But where does security fit into the new landscape of smart home systems? We asked this week’s Expert Panel Roundtable: What’s new in smart homes and residential security systems?
Products


White papers

Physical access control
Download
Precision and intelligence: LiDAR's role in modern security ecosystems
Download
How security systems ensure healthy workplaces during COVID and after
Download
Ensuring cybersecurity of video
Download
RFID and smartphone readers in physical access control
Download
Access control & intelligent vehicle screening
Download

Videos
Airport security: Manufacturers & Suppliers

One system, one card
Download
Aligning physical and cyber defence for total protection
Download
Understanding AI-powered video analytics
Download
Enhancing physical access control using a self-service model
Download
How to implement a physical security strategy with privacy in mind
Download