Access Controllers (735)
Browse Access Controllers
- Controller Type
- Networkable
- Standalone
- Standalone/Networkable
Access control controller products updated recently
Access control controllers - Expert commentary

In this article, Peter Jackson, Managing Director at Jacksons Fencing, emphasises the significance of implementing and upholding robust security measures, highlighting their role i...

A study found that over 80% of smartphones have biometric protection enabled, up from 68% a few years ago - these statistics alone show the trajectory of biometric security solutio...
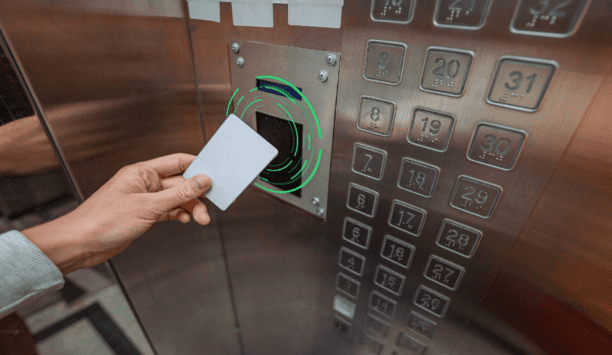
RFID and emerging mobile access technologies are easy to implement and allow elevator access to be integrated with other access control solutions throughout the building, from buil...
Related white papers
Cybersecurity in keyless access management
Three essential reasons to upgrade your access control technology in 2022
Securing unmanned infrastructure at the network edge
Trending topic articles
Alcatraz, the pioneer in facial biometric authentication for physical access, now announced the successful completion of its SOC 2 examination as of November 7, 2025. The independent audit was conduc...
Datalogic, a pioneer in automatic data capture and process automation, will demonstrate how its integrated portfolio is empowering the intelligent store at NRF 2026, thanks to AI-driven integration....
Deep Sentinel, the pioneer in AI-powered proactive video surveillance with real-time human intervention, now announced the launch of its Mobile Monitoring Trailer — a fully mobile, solar-powered...
The contract was signed, live at the SPS in Nuremberg, Germany: CADENAS is now the newest member of the Eplan Partner Network. CADENAS Managing Director Terry Jonen and Eplan Managing Director Ha...
AI is one of the fastest-growing technologies in the history of modern business, with the ability to revolutionise industries, optimise operations, and drive innovation, but it is also introducing sec...
Smeup, a key partner for companies engaged in digital transformation, now announced the expansion of its adoption of Cubbit, the first geo-distributed cloud storage enabler, as part of a Business Alli...
WatchGuard® Technologies now announced that its endpoint security solution delivered outstanding performance in the latest MITRE ATT&CK® Enterprise Round 7 (ER7) Evaluation. The results h...
EnGenius Technologies Inc., a pioneer in advanced connectivity and cloud-managed networking solutions, today announced that Crossroads Church in Rowlett, Texas, has completed a comprehensive security...
The Physical Security Interoperability Alliance (PSIA) has now announced the release of a new PKOC Explainer Video, created to offer a clear and visual overview of the Public Key Open Credential (PKOC...
Integrated Control Technology (ICT®), a pioneering provider of intelligent access control, intrusion detection, building automation and security solutions, is pleased to announce the appointment o...
Zimperium, the pioneer in mobile security, today announced new research from its zLabs team uncovering DroidLock, a rapidly evolving Android malware campaign targeting users in Spain. Unlike traditi...
Bugcrowd, a pioneer in crowdsourced cybersecurity, has launched new platform functionality, Bugcrowd AI Triage Assistant and Bugcrowd AI Analytics, to bring unprecedented spee...
HENSOLDT AG announces that Sven Heursch, previously Head of Software-Defined Defence & Digitalisation, will be appointed Chief Digital Officer (CDO) with effect from 1 January 2026. In this role,...
Videonetics, the pioneer in True AI-powered video analytics and unified video computing platforms, reaffirmed its commitment to shaping the future of intelligent video technologies at Videonetics...
To serve various vertical markets and industries effectively, security professionals must recognise that each sector has unique assets, risks, compliance requirements, and operational needs. Instead o...
One system, one card
DownloadAligning physical and cyber defence for total protection
DownloadUnderstanding AI-powered video analytics
DownloadEnhancing physical access control using a self-service model
DownloadHow to implement a physical security strategy with privacy in mind
Download