 |
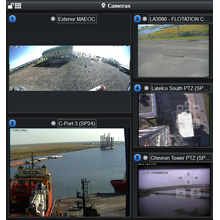
| Milestone XProtect is a day-to-day VMS, providing the video inputs and archives to the officers at the port |
Port Fourchon plays a strategic role in supplying the United States with nearly 18 percent of its oil supply, servicing over 90 percent of the Gulf of Mexico’s deepwater exploration and production. Securing such an essential portion of the Gulf Coast requires a hands-on team of security professionals to watch for unauthorised activities and enhance the safety of workers and officers. When evaluating options for a surveillance system to feed its new maritime domain awareness platform GLPC-C4 (C4), Port Fourchon officials chose Milestone XProtect® Enterprise video management software (VMS).
“On a day-to-day basis, we are observing numerous points of interest throughout the port, in addition to providing a helping hand to the security officers. The video surveillance system has been taken to an entirely new level, integrating multiple systems for complete coverage. Milestone’s open platform allows us to feed video analytics and disparate cameras through it, and the entire port is benefiting immensely.” April Danos, Director of IT, Port Fourchon.
The challenge: As the first land point of contact for approximately 90 percent of all Gulf of Mexico deep-water activities, including more than 600 rigs and platforms within a 40-mile radius, Louisiana’s Port Fourchon has unique safety standards to combat potentially devastating safety issues that may damage vessels, equipment, products and people working at the port. Obsolete surveillance equipment previously used to monitor the area was not sufficient to support the new C4 platform. A new video system was required to provide clearer imaging, improved storage capabilities, wider coverage and flexible video management.
The solution: Milestone XProtect® Enterprise software has been deployed by Convergint
Technologies to manage 64 cameras from Bosch and Pelco. With Milestone’s ability to display video in real time and its open platform architecture for integration with analytics from BRS Labs, the port’s personnel have the benefit of much more comprehensive and responsive video surveillance. Alerts from the video analytics system are fed through XProtect®, and into the Port’s C4 platform, where they are integrated with other alerts to create improved overall situational awareness.
The advantages: Several strategic elements are deployed in the port’s surveillance network, and these elements work in unison to create complete behavioral analytics. The biggest advantage seen by the port is the ability to have the dispatchers, through the C4 common operating picture, pull up all camera views that they need to address an alert or an incident. It is also easy to add more cameras to the port’s surveillance network (which the Port did in conjunction with the installation of a new radar system from DMT), since the Milestone open platform supports the largest variety of manufacturer models.
A Top Hub in Our Nation’s Oil Supply Chain
About 80 percent of all Gulf oil comes from deepwater, and Louisiana’s Port Fourchon services more than 90 percent of the Gulf of Mexico’s deepwater activities. In addition to being the premier service base for the Gulf’s tremendous domestic hydrocarbon supply, Port Fourchon is the land base for Louisiana Offshore Oil Port (LOOP), which handles 10 percent of imported oil.
Port security and the police have their work cut out for them, ensuring the nation’s oil supply, the workers and vessels, and every piece of equipment used to transport the product, are kept secure on a day-to-day basis.
The previous surveillance system, installed more than a decade ago, was not up to the standards required by the Port for its new C4 installation. Many members of the Port’s security department and police force experienced difficulties with the old video system for its less-than-user-friendly interface, slow feeds, minimal storage and need for more cameras.
"Alerts come right through the port’s Milestone XProtect setup. We can provide a brief clip of any target, time-and-date stamp it and inject it into the alarm" |
“We all agreed that our new video management system should be easy to integrate and allow us to dovetail with our legacy equipment while having an opportunity to shop around for upgraded hardware without any proprietary restrictions,” stated April Danos, Director of IT, Port Fourchon.
“The ability to scale up over the years to increase the port’s protection was another very important aspect that needed to be addressed with the incoming VMS solution.”
Key points in the port’s request for proposals included a system with minimal maintenance requirements, video display in real time, user-friendly operation and the ability to easily integrate a variety of already installed and soon-to-be-installed components: new servers, cameras, and analytics software, for instance. Milestone XProtect Enterprise VMS was chosen and implemented by Milestone certified partner Convergint Technologies.
GLPC-C4 Priority 5’s Touch Assisted Command and Control System (TACCSTM) powers the Port’s C4 system. TACCS is an all-hazards command and control operations platform that integrates the VMS inputs with other data feeds to support the Port’s security and situational awareness requirements. Developed in response to requirements by the Department of Defense, the platform aligned with Port Fourchon’s vision for a centralised system into which all elements would be integrated, providing directors and police with full coverage of the analytics, radar, access control and security systems. With input from the Port and other early adopters, TACCS and the C4 system have evolved over the years, and now provide wide area situational awareness and response capabilities to Port Fourchon's Harbor Police dispatchers, Lafourche Parish Sheriff’s Office, the parish EOC, LOOP, and the Port Administrative, Operations and IT departments.
“Our goal is to enable the Port to use TACCS and its open architecture to create the most comprehensive and flexible situational awareness solution possible,” said Joe Kammerman, Vice President of Priority 5. “Working with other companies such as Milestone that design their solutions around open architectures has proven to create a real value to customers, especially in today’s environment where budgets are tighter and people need to do more with less.”
“Many companies claim to provide an integrated system, but what they deliver is more likely to consist of a large number of windows scattered on a screen, without any data integration,” noted Danos. “Milestone’s integration of video management and very detailed analytics literally gives our operators one single data feed through which the port’s entire surveillance system can be readily accessed as needed. We don’t miss a beat, which is priority number one when dealing with the safety of those at the port.”
 |
| Several C4 stations throughout the port contain command centers equipped with Milestone |
The Setup
Several C4 stations throughout the port contain command centers equipped with Milestone: three within the main office in Galliano, LA, one setup two miles from the port in the harbor police headquarters and one in the port itself. The LOOP system is networked into the Milestone software and Lafourche Parish Sherriff’s Office, with access to the port’s live feeds. The Federal Emergency Management Agency (FEMA) is also connected to the port for cases of emergency.
Each registered user in the port security team has immediate access to Milestone video archives, going back as far as two months.
“We have a good mixture of different makes and models of camera hardware and different analytics strategically deployed. We are very pleased with the way Milestone’s open platform enables us to explore multiple opportunities without worry of technology being rejected or reworking our entire system,” continued Danos. “All of the systems we implement in the port are brought in with the security factor in mind. Milestone has been very impressive as we adapt our system to improve operations every day.”
All of the port’s surveillance systems work in unison with a behavior analytics system.
Milestone is the only interface that can process this large amount of information, according to Bruce Whitaker of BRS Labs. “Alerts come right through the port’s Milestone XProtect setup. We can provide a brief clip of any target, time-and-date stamp it and inject it into the alarm. The users are looking at real-time video with the alerts built right in. No event goes unseen.”
The Benefits
Milestone XProtect is a day-to-day video management system, providing the video inputs and archives to the officers at the port to protect against criminal activity and helping to identify damage done to the docks or vessels that have been left unattended for long periods of time, among numerous other activities.
The Milestone video product feeds the C4 common operating picture, enabling the dispatchers to maintain the big picture while having the ability to monitor video surveillance throughout the port. There are hundreds of continuous activities going on at any time. With all systems integrated, the officers can concentrate on security itself, not worry about the system working properly.
“Nothing held up to the qualities of Milestone when we were researching for the port software integration,” stated Whitaker. “During the selection process, its capabilities were front and center. If we had any limit on our VMS options, we wouldn’t have a fraction of the benefits the port offers its security team now.”
“The port has transformed its security platform to a new level,” concluded Danos. “We are working to be as far-sighted as possible, with the integration of our numerous best-of-breed applications, so the C4 system will always provide the highest level of maritime domain awareness. Starting with the Milestone open platform has allowed us to integrate numerous video applications through it, and the entire port is benefiting immensely.”





















